Want to launch your own DDoS attacks on a website? $200 will get you everything you need

Cybercriminals don’t have to make their own malware these days, they can simply purchase ready-made kits. They don’t need to take out a bank loan to do so either -- malware is more affordable than you might think.
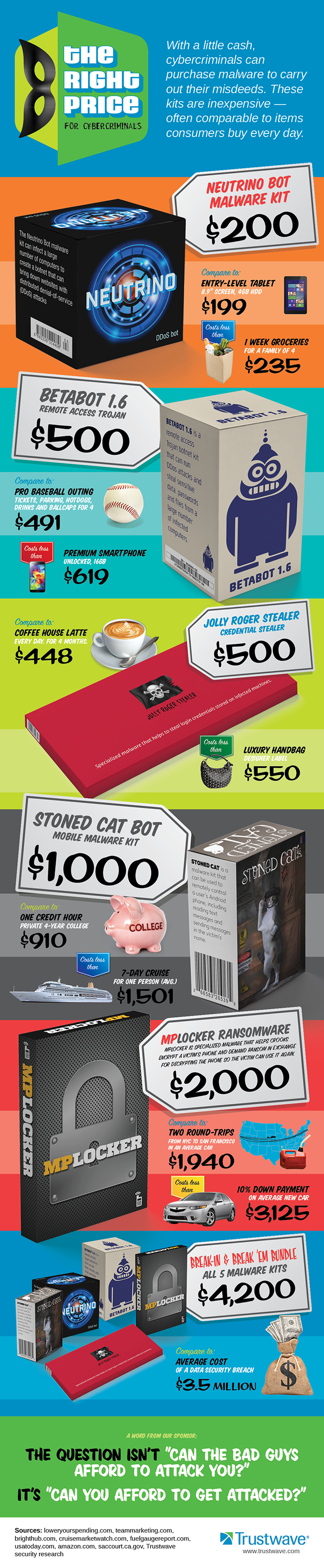
Trustwave’s security researchers did a little digging and found that depending on the type, malware can cost as little as two hundred dollars on the black market, and the tools on offer are pretty sophisticated too. Got your wallet ready? Here’s a price list of just some of the currently available malware:
$200 -- For this you can buy the Neutrino Bot Malware Kit which can be used to infect a large number of computers, create a botnet, and launch distributed denial of service (DDoS) attacks against websites and services you don’t like.
$500 -- Want something more sophisticated? BetaBot 1.6 is a remote access Trojan that can run DDoS attacks, and steal sensitive data, passwords and files from infected systems. Alternatively, for the same asking price you can buy the Jolly Roger Stealer which helps nab login credentials from infected machines.
$1000 -- For a grand you can pick up the Stoned Cat Bot, a mobile malware kit that can be used to remotely control a user’s Android phone, giving you access to their texts, and allowing you to send messages in their name too.
$2000 -- For this price you can get your hands on the MPLocker Ransomware. This nasty tool will let you encrypt a victim’s phone and demand a fee to unlock it again. The asking price might seem a little steep, but you’ll earn your initial outlay back in no time.
$4,200 -- If money’s no object, why not go for the Break-In & Break ‘Em Bundle -- all five of the previously mentioned malware kits for well under $5K.
While the affordability of malware kits like this might shock you, Karl Sigler, Threat Intelligence Manager at Trustwave, is far less surprised by the findings. "Supply and demand affects malware markets like they do any market. Even though demand is high, there is an increasing amount of malware competing with each other and this helps drive down the cost. There is also a cost-benefit issue. Criminals look at how much they can make by selling stolen data acquired using the malware. Finally, age plays a role. The longer malware is on the market, the cheaper it tends to get".
And don’t make the mistake of thinking it must be pretty hard to get your hands on these kits -- turns out that’s very straightforward too. "It's quite easy to access black markets", Sigler says. "They tend to be available over Tor and the links are often shared in public hacker forums. The most popular kind of malware are Remote Administration Toolkits (RATS) and banking Trojans like GameOver Zeus".
The problem of malware affects both businesses and individuals alike. Sigler offers the following tips for keeping safe:
"Because malware is so affordable, the greater the appeal for criminals to buy it and launch attacks. That’s why businesses need to bolster their anti-malware defenses so that they are continuously staying ahead of the criminals and making it harder for them to win. Anti-malware defenses include deploying gateway technologies that detect and block malware in real-time and making sure businesses have enough manpower and skillsets to help ensure those technologies are updated and working properly. Individual users also need to be careful when clicking on links and opening attachments. If you receive an email that includes a link or an attachment, you should confirm with the sender that he/she did in fact send it before clicking on or opening anything. Security awareness education training helps users better understand best security practices and flags to look for that may indicate they have been breached".
Trustwave has put together a lovely infographic showing the malware kits on offer, and what you could buy for the same price (or a little more) if you’re not criminally minded...