Android users, beware -- a new Trojan may hold your files for ransom
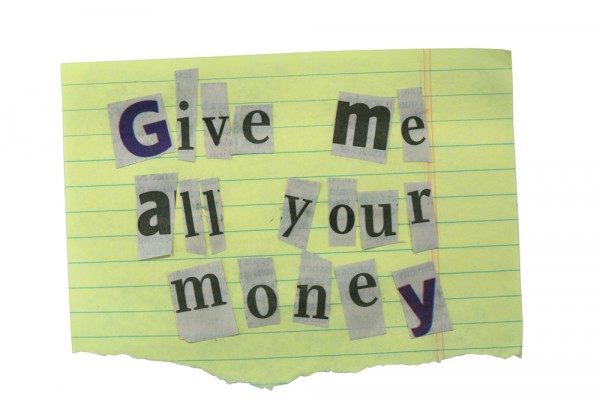
Security experts have discovered a new Trojan that scrambles the files on memory cards in Android devices and demands a ransom to open them.
Slovakian security company Eset claims it is the first discovery of file-encrypting ransomware for Android. Called "Simplelocker", the Trojan targets SD cards inserted into Android tablets and mobile phones, encrypts the files and demands payment in order to decrypt them.
You'd be forgiven for thinking you've heard this warning before. Last year, Symantec reported the discovery of ransomware masquerading as a legitimate Android security app called Android.Fakedefender, and Sophos told us to be wary about Android scareware called AndroidDefender. But, according to Eset, this is the real thing.
"Last weekend saw the (somewhat anticipated) discovery of an interesting mobile Trojan -- the first spotting of a file-encrypting ransomware for Android by our detection engineers. This malware, after setting foot on an Android device, scans the SD card for certain file types, encrypts them, and demands a ransom in order to decrypt the files", says Eset security researcher Robert Lipovsky
Lipovsky further explains, "the malware is fully capable of encrypting the user's files, which may be lost if the encryption key is not retrieved".
After launch, the Trojan displays a ransom message in Russian saying that the device was locked because the owner had viewed and distributed child pornography, zoophilia and other perversions, and encrypts files in the background. Payment is then demanded in Ukrainian hryvnias.
Simplelocker will scan the SD card for files with the following image, document or video extensions: jpeg, jpg, png, bmp, gif, pdf, doc, docx, txt, avi, mkv, 3gp, mp4 and encrypt them using AES.
According to Eset, because Simplelocker is a "proof-of-concept or a work in progress" the implementation of the encryption, while nasty, "doesn't come close to Cryptolocker on Windows". Hundreds of thousands have been targeted by Cryptlocker, which has netted fraudsters up to $30 million in ransom.
Eset advises not to give into ransom demands because it "will only motivate other malware authors to continue these kinds of filthy operations" and "there is no guarantee that the crook will keep their part of the deal and actually decrypt them. Instead, it is better to protect yourself against such a threat by using a mobile security app and staying away from untrustworthy apps and app sources.
Photo Credit: Robynrg/Shutterstock