Why the concept of 'single pane of glass' in cybersecurity is a myth

As we approach 2021, there’s a new technology revolution underway. Yes, software is king -- but our data is siloed in applications. In order to achieve the next rung of technology innovation, we must take a Data-Centric and API-first approach to software development to allow for better connections between your ecosystems of tools.
The breed of software solutions that emerge in this coming decade will disabuse themselves of the dreaded, empty promise of the 'single pane of glass'. They will prioritize development for the API and reduce the reliance on UI for data management.
For the first time in enterprise security, we have evidence that suggests an app-centric approach has peaked in value. The 2020 Ponemon Cyber Resilience Study notes "Organizations with more than 50 tools ranked 8 percent lower in their ability to detect a cyber incident."
When you look at the 2020 Momentum Cyber Landscape report or take a stroll down through the expo hall of any cyber security conference (back when that was a thing), it’s no wonder.
In a typical app-centric mindset, we’re hopeful that an all-powerful app for automation or one-ring-to-rule-them-all solution will emerge. Of course, the industry analyst oracles have not helped by creating a category called Security Orchestration and Automated Response (SOAR) and stuffed a hodgepodge of incident response platforms and standalone orchestration tools - or what Dave McComb in The Data-Centric Revolution would call IFFTs for If-This-Then-That - designed to mimic human behavior by using data or a 'task' as an input and the output is a behavior that mimics a human action.
Gartner did get one thing right: identified that Customers and Vendors are embracing automation. Naturally the leading detection and response app vendors will be investing in automation and they are acquiring automation tools to accelerate their own in-app automation capabilities. The more that they can keep you in their app, the more revenue they can extract. But, if you are using multiple tools for detection and response and use multiple intelligence sources for enrichment, then there is no detection and response app that is going to remove the silos that they are incentivized to preserve. The first step is to stop looking for your detection and response apps to get us out of the silos that they are incentivized to preserve.
The only path to efficient and effective automation is to embrace what McCombs calls "organized and resilient data" independent of your detection and response apps to effectively drive automation. In other words, you need a place upstream to manage your intelligence, to design your Intel Workflows where data is the input and data is the output to be consumed by playbooks and automated workflows in your downstream apps.
Data-centric security automation recognizes that the primary purpose of intelligence is to accelerate automation in security operations. Adherents are born in the cloud, product releases are more about API contracts than User Interface features, and value is demonstrated through API amplifiers like Swagger or Postman or even through the User Interface of another, entrenched tool!
The coming wave of enterprise security products have significant ground to make up compared to products in other industries that spent the last decade innovating on data-centric approaches to sales, marketing, devops or support automation, but embracing a Data-Centric and API-first approach is the right first step to advance security in the era of ecosystems.
The influx of funding into the cyber security space in the last 10 years has led to an explosion of cyber security products and contributed to an app-centric view of enterprise security.
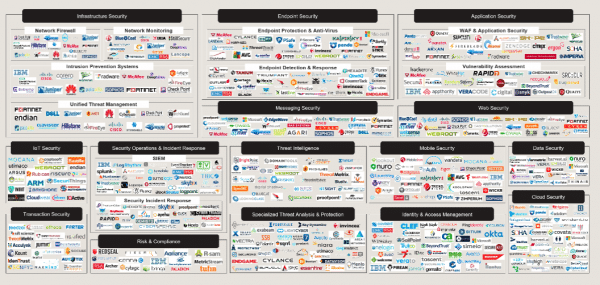
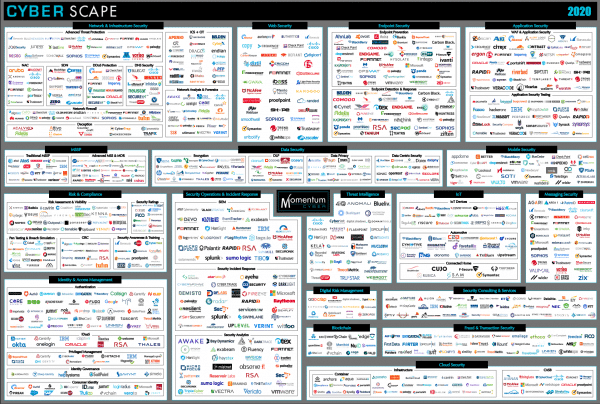
After decades of being bombarded with the newest and "Next-Gen-___" at the RSA or Black Hat circus, enterprise security leaders are recognizing we have finally reached the peak of an app-centric view. In data-centric terms, this proliferation of apps has led to what Dave McComb calls “Integration Debt” in his book Software Wasteland: How the Application-Centric Mindset is Hobbling the Enterprise.
Image credit: iunewind / depositphotos.com

Patrick Coughlin is the Co-Founder and Chief Executive Officer of TruSTAR. Before founding TruSTAR, Patrick led cyber security initiatives in the Middle East as a Director at Good Harbor International. Patrick also led counterterrorism analyst teams for Booz Allen Hamilton clients in the DoD and Special Operations Command.