
Huawei: 'There's no way the US can crush us'
The founder of Huawei, Ren Zhengfei, has hit back against Trump's ban on the use of his company's hardware because of concerns about Chinese espionage, saying "there's no way the US can crush us". The US has been trying to encourage other countries to follow its lead in shunning Huawei, but the UK has said it will not stop the company -- which is due to launch its P30 range of smartphones next month -- from getting involved in the rollout of 5G networks.
Ren also lashed out at the US, saying that the arrest of his daughter and Huawei CFO, Meng Wanzhou, was politically motivated.

Australian political parties hit by hack orchestrated by 'sophisticated state actor'
Australia's three main political parties -- Liberals, Labor and Nationals -- as well as the country's parliament have all been hit by a security breach which Prime Minister Scott Morrison says was carried out by a "sophisticated state actor".
Although the country is due to hold elections in the coming months, Morrison says there is "no evidence of any electoral interference". While it is not currently known who is responsible for the attack, various potential culprits have been suggested, including China, the US, Israel and Russia.

Unlike the US, the UK does not want to ban Huawei from 5G networks
With concerns about Chinese spying, the US has been embarked on a campaign to prevent Huawei from operating in the country. In addition to banning officials from spending money on Huawei equipment, the US government has been trying to convince other countries to follow its lead and shun the company.
Despite US pressure -- and similar moves by New Zealand and Australia -- the UK says that it has no plans to cut Huawei technology out of 5G networks. The National Cyber Security Centre says that there are ways to mitigate against any potential risk posed by Huawei equipment.

Security researcher 'concerned' to find Twitter is not deleting your deleted direct messages
When you delete a direct message on Twitter, it is gone forever, right? From a user's point of view, this is true -- a deleted message vanishes. But a security researcher has discovered that Twitter is actually hanging onto these messages.
Karan Saini found that he was able to see messages he deleted years ago when he downloaded an archive of his Twitter data from the site.

How to check to see if your data was part of the Marriott Starwood Hotel hack
When hackers hit Marriott's Starwood Hotel database last year, it was first thought that half a billion customers might be affected. This estimate was later downgraded to 383 million guests, but this is still a very large number, and it is understandable that many people are concerned that their data may have been accessed.
There was particular concern about whether passport numbers had been accessed, and this is what a new checking tool lets you check. Marriott has teamed up with security firm OneTrust to enable customers to check if their data was included in the security breach.

3 data leaks that could be undermining your online privacy
Protecting your online privacy is important. There has been a lot of discussion in recent years about how to stay safe online, and an increasing number of people are turning to Virtual Private Networks to keep their browsing data hidden from advertisers and overzealous intelligence agencies.
However, your privacy could still be at risk even behind the protection of a VPN. There are three common vulnerabilities that can leak information about you online: WebRTC and DNS leaks which affect VPN users, and app data leaks which can affect anyone and everyone. Read on to find out more about these three types of data leak, and what steps you can take to prevent them.

How contact centers have become a prime target for hackers [Q&A]
With growing security threats and compliance being taken seriously, companies are more aware than ever of the need to protect their data.
This means hackers must work harder to try to steal information and contact centers are in the front line. We spoke to Ben Rafferty, chief innovation officer at security and compliance specialist Semafone to find out how contact centers are under threat and what can be done to protect them.

Dark web tags harm website performance and put data at risk
Website tags, small pieces of JavaScript code or small images, are often used to collect information about users. But they can add to load times and if misused can be a security risk too.
A new study from digital governance specialist Crownpeak reveals over 1,700 'dark web' tags found on websites belonging to companies in the Fortune 100, causing a total average website latency of 5.2 seconds.

Roses are red, violets are blue, Valentine scammers are out to trick you
A Nigeria-based gang of scam artists, known as Scarlet Widow, have been using romance scams to trick victims out of large amounts of cash.
Secure email company Agari has uncovered the scam which involves posting fake personas on the largest dating websites like Match, eHarmony, and OKCupid.

Only one in three organizations is confident of avoiding a data breach
A majority of organizations are not confident in their ability to avoid major data breaches according to a new study.
The report for breach avoidance company Balbix, based on research from the Ponemon Institute, shows that 68 percent feel their staffing is not adequate for a strong cybersecurity posture and only 15 percent say their patching efforts are highly effective.
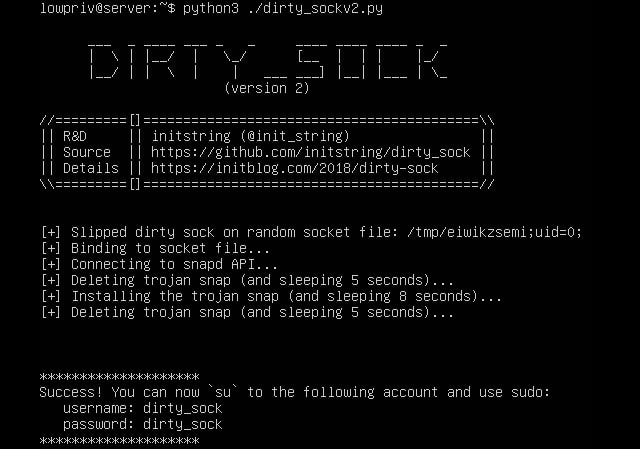
Dirty_Sock vulnerability in Canonical's snapd could give root access on Linux machines
A security researcher has discovered a vulnerability in Canonical's snapd package which could be exploited to gain administrator privileges and root access to affected Linux systems. The security issue has been dubbed Dirty_Sock and assigned the code CVE-2019-7304.
Chris Moberly found a privilege escalation vulnerability in the snapd API. This is installed by default in Ubuntu -- under which proofs of concept have been tested and found to work "100% of the time on fresh, default installations of Ubuntu Server and Desktop" -- but may also be present in numerous other Linux distros.

User data exposed in 500px security breach... that happened in the middle of last year
The photo sharing site 500px has revealed details of a security breach that took place in mid-2018.
The company says that its engineering team only became aware of the breach -- which is thought to have taken place around July 5, 2018 -- a few days ago. 500px launched an investigation in conjunction with a third party and police, and says that "an unauthorized party gained access to our systems and acquired partial user data".

Security worries hold back second-hand mobile device market
According to the results of a new study, 58 percent of global consumers have yet to trade in an old mobile device, though 64 percent report they would be willing to do so if more stringent data management processes were in place.
The research by data erasure specialist Blancco shows 66 percent of respondents have some concern that data on their old devices might be accessed or compromised after trade-in.
VFEmail hack wipes out all of the email provider's US servers
Email provider VFEmail has been hit by a huge attack that resulted in all of the data it stores in the US being wiped out.
Describing the attack as "catastrophic", VFEmail revealed that a hacker had breached its security and succeeded in deleted not only primary data systems, but also the backups. The attacker was caught in the act, and it was possible to intervene before damage was caused to servers in other countries. But for VFEmail users whose data was stored in the US, the news is far from good.

Could the 3D video selfie replace 2FA?
The industry is constantly looking for ways to bolster login security. Multi-factor authentication and knowledge-based systems are popular but can be cumbersome, so how about using something you carry around all the time, yourself -- or indeed yourselfie?
Identity specialist Jumio is launching Jumio Authentication, a video-selfie authentication tool enabling users to verify themselves during high-risk transactions and unlock everything from online accounts to rental cars, replacing passwords on any device.
