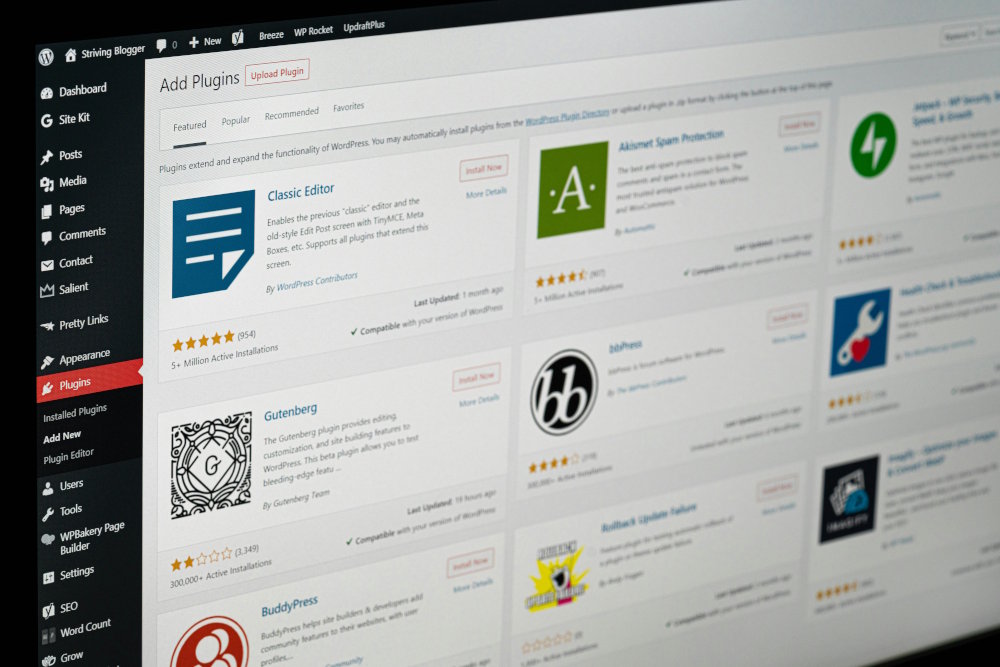
Browser security tools struggle to detect malicious extensions
Despite the expanding use of browser extensions, the majority of enterprises and individuals still rely on labels such as ‘Verified’ and ‘Chrome Featured’ provided by extension stores as a security indicator.
However, new research from SquareX points up architectural flaws in how browser security tools work which mean they’re unable to detect or prevent the latest advancements in malicious browser extension attacks.

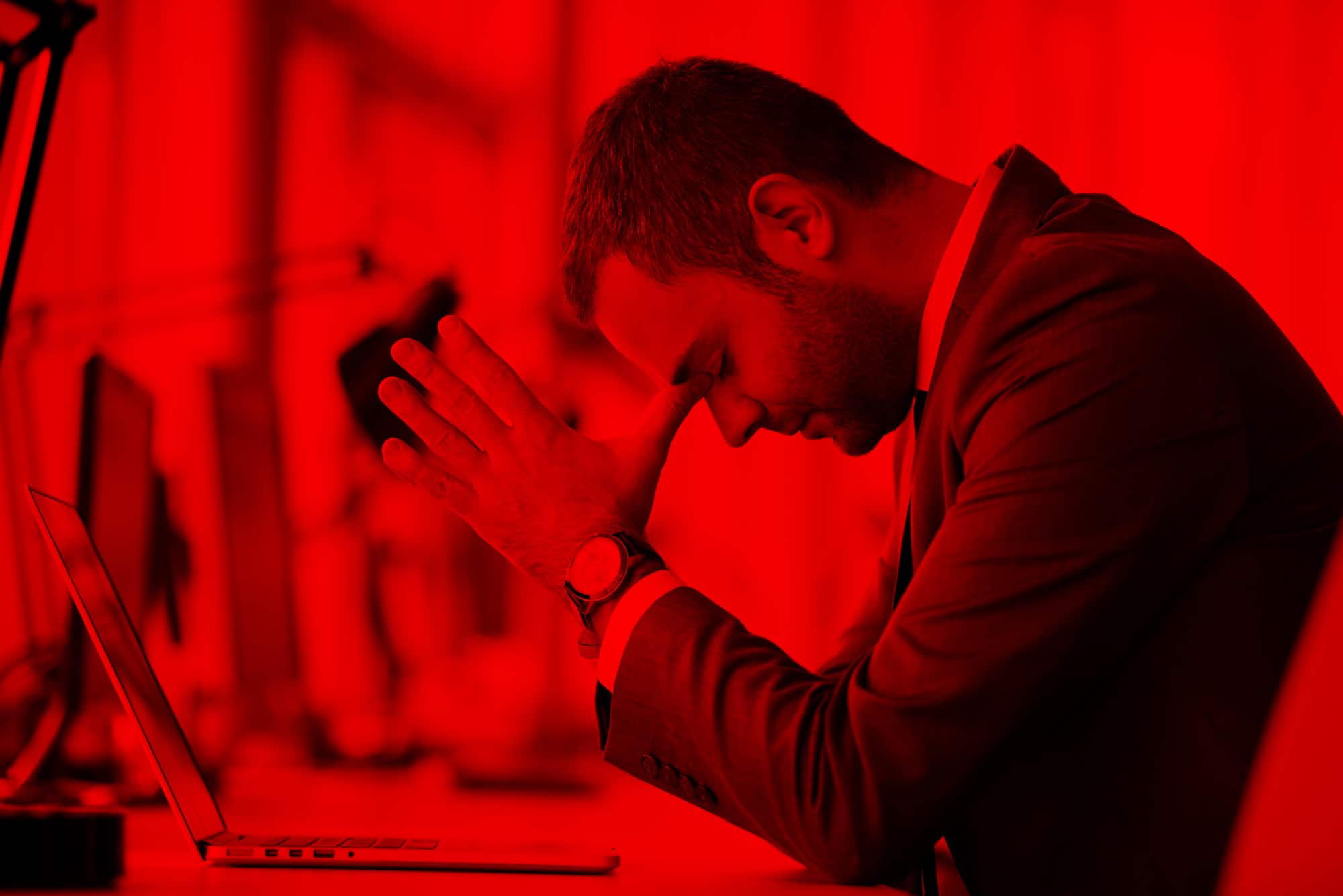
Managing cyber risks is getting harder
A new study reveals that that 90 percent of leaders find managing cyber risks harder today than they did five years ago, resulting in higher reports of burnout (47 percent), including more than one in ten who say they’re on the verge of quitting.
The report from Bitsight shows the leading causes of poor cyber risk management, and therefore burnout, include an explosion of AI (39 percent), and rapidly expanding attack surfaces (38 percent).

Navigating the hidden dangers in agentic AI systems [Q&A]
According to Gartner 33 percent of enterprise applications are expected to incorporate agentic AI by 2028, but are their security teams equipped with the latest training and technology to protect this new attack surface?
We spoke with Ante Gojsalić, CTO and co-founder at SplxAI to uncover the hidden dangers in agentic AI systems and what enterprises can do to stay ahead of the malicious looking to exploit them.

AI emerges as a cybersecurity teammate
On its own artificial intelligence isn’t a solution to cybersecurity issues, but new data from Hack The Box, a platform for building attack-ready teams and organizations, reveals that cybersecurity teams are increasingly beginning to adopt AI as a copilot for solving security challenges.
Based on real-world performance data from over 4,000 global participants in Hack The Box’s Global Cyber Skills Benchmark, a large-scale capture the flag competition, the report highlights how cyber teams are starting to use AI as a teammate to their security staff.

Data silos -- why they’re flawed and what to do about it [Q&A]
Every application, database, filesystem and SaaS service inevitably creates another data silo. From Hadoop-based data lakes to modern data warehouses and lakehouses, enterprises have invested millions in the promise of a single source of truth. But these grand visions invariably fall short.
We talked to Saket Saurabh, CEO and co-founder of Nexla, to discuss a more practical approach that embraces the existence of data silos while ensuring seamless access and usability.

New ‘hardened runtime’ standard aims to make organizations more secure
Traditional runtime security solutions have tended to focus on detection and as a result generate thousands of low-fidelity alerts. Edera is launching what it says is a new software security category aimed at ending the era of 'move fast and break things'.
Edera's ‘hardened runtime’ provides production-grade sandboxing that assumes a breach before it occurs. This architectural approach eliminates the root causes of privilege escalation, lateral movement, and data exfiltration while dramatically reducing operational overhead for security teams.

Just six percent of CISOs have AI protection in place
While 79 percent of organizations are already using AI in production environments, only six percent have implemented a comprehensive, AI-native security strategy.
This is among the findings in the new AI Security Benchmark Report from SandboxAQ, based on a survey of more than 100 senior security leaders across the US and EU, which looks at concerns about the risks AI introduces, from model manipulation and data leakage to adversarial attacks and the misuse of non-human identities.

Privileged access management is key to enterprise defense
New survey data reveals that 49 percent of organizations with privileged access management report fewer security incidents tied to privilege misuse.
The report from Keeper Security, based on a global survey of 4,000 IT and security leaders in the United States, Europe and Asia, explores the motivations driving PAM adoption, the most common obstacles to deployment and the features enterprises consider essential for securing access in today’s cybersecurity threat landscape.

Consumers are putting more trust in AI searches
A new survey of over 2,000 consumers across the US, UK, France and Germany looks at how people are adopting, and trusting, AI tools to discover, evaluate, and choose brands.
The study from Yext finds that 62 percent of consumers now trust AI to guide their brand decisions, putting it on par with traditional search methods used during key decision moments. However, 57 percent still prefer traditional search engines when researching personal, medical or financial topics.

MSPs struggle with complexity and tool sprawl
Newly released research from cybersecurity platform Cynet shows managed service providers (MSPs) are facing growing operational strain as they race to meet demand for cybersecurity services.
While cybersecurity services are driving growth and deepening client relationships, most MSPs are hitting operational roadblocks, held back by fragmented tools, limited automation and lean security teams.
60 percent of enterprise firewalls fail critical checks
New research from FireMon shows that 60 percent of enterprise firewalls fail high-severity compliance checks immediately upon evaluation, with another 34 percent falling short at critical levels.
Using data collected anonymously from AI-powered analytics platform FireMon Insights deployments across large enterprises and regulated industries, the study found misconfigurations, outdated rules, and bloated policies that bog down performance and leave security teams struggling to keep up.

What’s behind the recent rise in identity-based attacks? [Q&A]
Cybercriminals are increasingly using sophisticated identity-based attacks (phishing, social engineering, leveraging compromised credentials) to gain access as trusted users and move laterally across systems undetected.
We spoke to Cristian Rodriguez, field CTO, Americas at CrowdStrike, about the company’s recent research into these attacks and now organizations can defend against them.

Free tool uncovers API vulnerabilities
According to Verizon’s 2025 Data Breach Investigations Report, API-related breaches have increased nearly 40 percent year-on-year, with broken authorization cited as one of the most exploited flaws.
Now though Intruder, a leader in attack surface management, has launched Autoswagger -- a free, open-source tool that scans OpenAPI-documented APIs for broken authorization vulnerabilities.

83 percent of IT and engineering professionals bypass security controls
A new survey of 1,000 IT, security, and engineering professionals across North America uncovers a fractured landscape of legacy VPNs, slow manual processes, and overlapping tools -- with 99 percent of respondents saying they'd like to redesign their company’s access and networking setup from the ground up.
The study from Tailscale also shows that 83 percent of IT and engineering professionals admit to bypassing security controls in order to get their work done. Also worrying is that 68 percent say they have retained access to internal systems after leaving a previous employer, revealing critical gaps in offboarding and identity lifecycle management.

New AI-driven features set to help security remediation efforts
Security teams today are overwhelmed by fragmented data, inconsistent tagging, and the manual burden of translating findings into fixes.
A new release of the Seemplicity platform introduces an AI Insights feature along with Detailed Remediation Steps, and Smart Tagging and Scoping, three new capabilities that use AI to solve some of the most painful and time-consuming cybersecurity tasks.