Why keeping old customer records could cost millions [Q&A]
The modern world thrives on data, but what happens when that data has outlived its usefulness? Legacy data can become a weak link in corporate security. These records don’t just take up space; they expand the exposure surface in a breach and can damage both finances and reputations.
We spoke with Rob Shavell, co-founder and CEO of DeleteMe, about why companies can’t afford to ignore legacy data and what they can do to address it.

Maturing ID wallets, investment for compliance and confidential AI -- privacy predictions for 2026
Privacy has been increasingly in the news over the last year with plans for government digital IDs and age verification for websites, as well as concerns about how eCommerce businesses and others use personal data.
What can we expect from the privacy landscape in 2026? Some industry experts give us their views.

How AI can supercharge fraud in the enterprise [Q&A]
The FBI reports that complaints around deepfake AI videos have more than doubled, and financial losses have nearly tripled this year.
Agentic AI is set to accelerate this process, making it even easier to commit fraud with deepfakes. We spoke to Alix Melchy, VP of AI at Jumio, to discuss the threat and how to combat it.

Data sovereignty, cloud and security [Q&A]
As more and more information is stored in the cloud, often with hyperscale providers, the issue of data sovereignty -- where the information resides and who can access it -- becomes increasingly crucial.
We spoke to Sergej Epp, CISO at Sysdig, and previously CISO at Palo Alto Networks, to explore the theme of data sovereignty, cloud and security.
AI video tools and how they’re changing business communication [Q&A]
The use of AI video has exploded in the past year. But while it’s deepfakes that make the headlines the technology also has the potential to change how businesses create and use video content in their messaging.
We spoke to Victor Erukhimov, chief executive officer of CraftStory, to find out more about AI video and how businesses can exploit it to their advantage.

AI risks, greater regulation and remote consultations -- healthtech predictions for 2026
Understandably perhaps the health sector has been slower than some to embrace the rush to AI. But more medical devices are now connected and AI is having an impact, offering benefits to patients but also opening up new risks.
We spoke to some leading industry figures to find out how they see healthtech developing in 2026

AI as a target, web-based attacks and deepfakes -- cybersecurity predictions for 2026
The very nature of cybersecurity makes it a constant arms race between attackers and defenders and recently that’s meant both sides utilizing AI.
This seems unlikely to change in 2026 but what else might we expect? Some industry experts give us their views.

Agent vs agent, reliable interfaces and value for money -- artificial intelligence predictions for 2026
Artificial intelligence has been driving much of the technical agenda for the last couple of years and is still evolving rapidly, finding its way into more and more areas.
Here some industry experts look at what we can expect to see from the AI space in 2026.
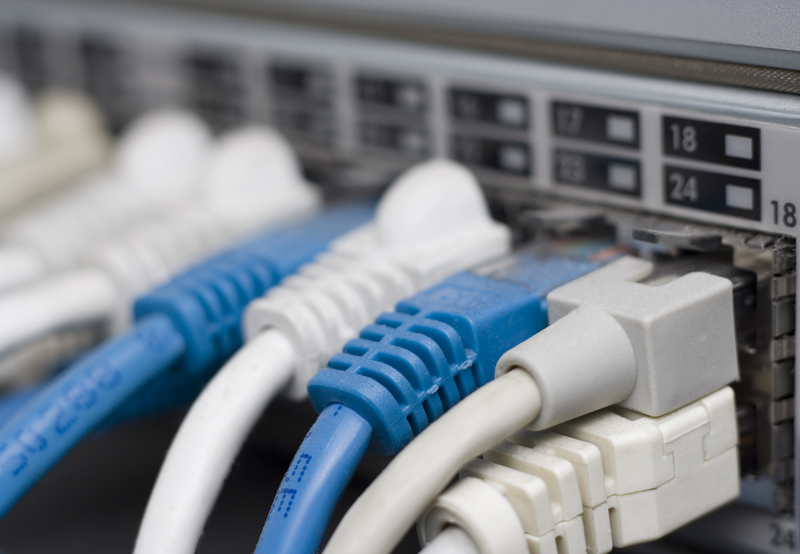
The silent danger of SSH key mismanagement [Q&A]
The recent AyySSHush botnet campaign compromised over 9,000 ASUS routers worldwide via SSH key injection. Unlike traditional botnets, this campaign flips the C2 model -- routers silently await inbound contact from the attacker, making detection incredibly difficult.
And since SSH key authentication happens after encryption is established, key usage remains invisible to most monitoring tools. Combine that with the fact that routers are critical, often unmonitored devices, and it’s easy to see why this attack is a sweet spot for adversaries.

Adapting to AI agents, growing risks and perimeter focus -- identity predictions for 2026
Identity remains key to cybersecurity with stolen IDs opening the door to many attacks. And with the rise of AI agents and machine identities it isn’t just just humans that we have to worry about. Here’s what some leading industry figures think we can expect from the identity landscape in 2026.
Itamar Apelblat, CEO and co-founder of Token Security, thinks compliance frameworks will need to be rebuilt to account for AI agents. “Traditional compliance models were designed for human-centric workflows, and they are already breaking. Over the next year, frameworks will evolve to recognize AI agents as workforce identities with their own permissions, accountability requirements, and control expectations. Organizations that fail to adapt will fall out of step with regulators and customers.”

AI data transparency shapes shopping behavior
A new survey of over 1,000 US consumers looks at how holiday shopping behavior is impacted by brand management of personal data in AI systems.
The study from Relyance AI suggests Americans are entering the gifting season emotionally depleted and digitally exposed, with most planning to shop online. But feeding more personal data into systems during periods of high stress and emotional depletion sets the stage for a fragile purchasing environment.

Why SaaS apps are a prime target for attackers [Q&A]
Attackers will always use tactics that are proven to work and with more business turning to SaaS for their systems obviously these apps are on the cybercriminal’s radar.
We spoke to Martin Vigo, lead offensive security researcher at SaaS security company AppOmni, to explore the reasons why SaaS apps are such fertile ground for attackers.

Hospitals struggle with visibility of connected medical devices
A new survey of CISOs at North American hospitals finds that 43 percent identified complete device visibility as the challenge they would most want to solve immediately, followed by ransomware threat detection (24 percent) and compliance automation (22 percent).
The study from Asimily also uncovered fragmentation in how hospital security teams approach vulnerability remediation. Only 22 percent of hospital CISOs base their prioritization on device usage and criticality, which is the most effective method for focusing resources on the highest-risk assets. Meanwhile, 18 percent rely on manual review and 15 percent report having no clear process at all for addressing IoMT (Internet of Medical Things) vulnerabilities.

Increased workloads, strategic influence and technical focus -- CISO predictions for 2026
The task of the CISO has historically been an underappreciated one. But as businesses wake up to the fact that cybersecurity issues can represent a threat to the entire business it has taken on more significance.
Here’s how a range of industry experts see the future for CISOs and their role as we head into 2026.

87 percent of enterprises are ready to switch productivity suites
IT leaders are unhappy with their productivity current setup and are forced to manage an average of over nine different tools. This is why, according to a new study, 87 percent of IT leaders will consider changing from their current productivity suite to adopt a more unified and secure platform.
The research from JumpCloud in collaboration with Google Workspace is based on a survey of 250 US IT leaders from enterprise organizations. Its findings show that IT teams are urgently searching for a new platform to make work simpler and more secure.

