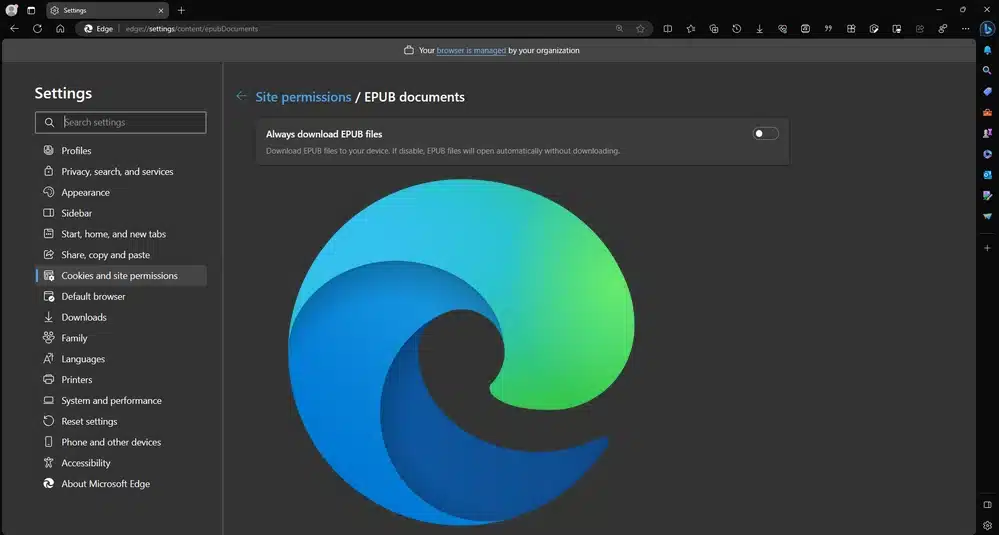
Microsoft Edge can now be used to read ebooks in EPUB format
The number of formats for ebooks is a little bewildering. While PDF may be queen, there are plenty of other formats vying for attention. Some are proprietary, but others are open -- including the widely used EPUB format, which Microsoft Edge can now open.
In the very latest build of its web browser, Microsoft has re-introduced EPUB support having removed it a few years ago. The feature is not enabled by default, and there are steps you need to take if you want to use Microsoft Edge as an EPUB reader.

Proton Pass is now an independently security audited, open source password manager
Privacy-centric firm Proton has announced that its password manager, Proton Pass, is now more than just open source. The company has had the code of its apps, browser extensions and APIs subjected to an independent security audit by German security specialists Cure53.
With passwords providing access to some of the most value and sensitive personal information imaginable, reliable security is essential. The auditors' assessment that Proton has a "commitment to maintaining a high-level of security" and that "the state of security across Proton's applications and platforms is commendable" will serve as helpful recommendations for anyone looking for a safe and secure password manager.
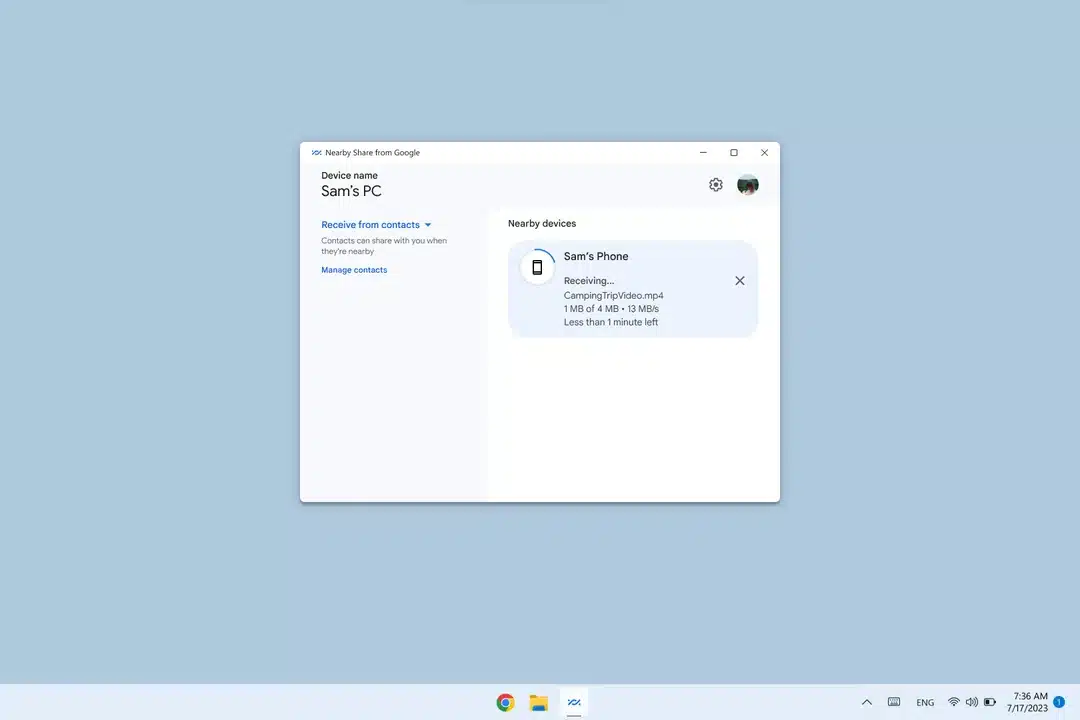
Google's Nearby Share officially comes to Microsoft's Windows 11
Google's innovative feature, Nearby Share, used by nearly 3 billion Android devices worldwide, has long made file sharing a breeze across smartphones, tablets, and Chromebooks. Earlier this year, in a move to expand its reach, Google initiated a beta version of Nearby Share for Windows PCs.
The expanded capability of Nearby Share opened the doors to a new kind of hardware connectivity between Android devices and Windows PCs. The Nearby Share for Windows app, which was globally available for download as a beta, has already seen an installation count exceeding 1.7 million, showcasing its growing demand.
Samsung ushers in new era of graphics with industry's first GDDR7 DRAM
In an move that is sure to excite PC gamers, Samsung today revealed the industry’s first Graphics Double Data Rate 7 (GDDR7) DRAM. The company is planning to incorporate this groundbreaking memory tech into the next-gen systems of their key customers for verification later this year. This innovative step is predicted to spur growth in the graphics market, while further solidifying Samsung's standing as the technological leader in this domain.
This announcement comes on the heels of Samsung's development of the industry’s first 24Gbps GDDR6 DRAM in 2022. Their latest 16-gigabit (Gb) GDDR7 offering promises to outperform this, offering the industry’s highest speed to date. Samsung has achieved this leap through innovations in integrated circuit (IC) design and packaging, ensuring stability even at top speeds.

Microsoft releases Windows 11 Build 23506 with Windows Copilot Preview, new passwordless experience, and local file sharing improvements
Windows 11 Insiders in the Dev Channel have a new test flight to install today, and Build 23506 comes with a good number of fixes and improvements, as well as some new features.
Chief among the new additions is a passwordless experience with Windows Hello for Business (WHFB). This, Microsoft says, "provides organizations with a strong, phish-resistant credential, helping customers move to a passwordless future", and it's available to try now.

NVIDIA technologies enable Saildrone to navigate the oceans with AI
Saildrone, a Bay Area startup, is redefining oceanic exploration and data gathering with its innovative use of autonomous uncrewed surface vehicles (USVs). With an impressive track record that includes tracking North Atlantic hurricanes, discovering underwater mountains, and mapping the world’s ocean floor, Saildrone is revolutionizing the way we interact with our oceans.
This game-changing technology utilizes a broad array of sensors in its USVs, with the data they gather processed by NVIDIA Jetson modules for efficient AI at the edge. The company is currently optimizing their prototypes with NVIDIA DeepStream software, a leap forward in intelligent video analytics.

Enhancing workplace security: A comprehensive approach to Mac and mobile device compliance
Workplace modernization has emerged as an important trend impacting organizations of all sizes, in all industries, and across all geographies. The move by so many businesses to embrace modern end-user technologies is anticipated to help improve recruitment, enhance employee productivity, and may have a measurable impact on talent retention.
One of the main forces behind workplace modernization is a belief that employees will be happier and ultimately more productive if they’re able to choose the devices they use for work. Coupled with both technical and organizational support for anywhere work styles, employees are finding they have a much stronger voice in the selection of IT tooling and the accompanying workflows.

Building high-performing tech teams from the ground up
Putting together a technical team from scratch isn’t quite as simple as setting up a few interviews and hiring the candidates that seem like they might be up to the job. Hasty decision-making often leads to unbalanced and misaligned teams, which is why research, planning and patience are all essential when developing a new branch of a business.
When the person responsible for constructing the team is new themselves, this introduces an array of potential stumbling blocks, as they will begin work on the project with a lack of understanding of organizational culture and the overall business structure.

New beta program lets Unity developers create games and apps for Apple Vision Pro
Unity, the global leader in real-time 3D (RT3D) content creation and growth, has announced the launch of its beta program for visionOS, the operating system used in Apple's new mixed media headset. This program will allow Unity developers to create games and apps for Apple Vision Pro using Unity PolySpatial.
The integration of Unity PolySpatial with the Unity editor will allow creators to build experiences that run in visionOS, taking full advantage of the features offered by Vision Pro.

Training makes critical infrastructure employees better at spotting phishing attacks
New research from security behavior change specialist Hoxhunt shows that 66 percent of active participants in security behavior training programs at critical infrastructure organizations detect and report at least one real malicious email attack within a year.
The report -- based on analysis of over 15 million phishing simulations and real email attacks reported in 2022 by 1.6 million people participating in security behavior change programs -- shows the effectiveness of training in making staff more engaged in organizational security.
Get 'Cybersecurity Threats, Malware Trends, and Strategies -- Second Edition' (Worth $33.99) for FREE
Cybersecurity Threats, Malware Trends, and Strategies, Second Edition builds upon the success of the first edition that has helped so many aspiring CISOs, and cybersecurity professionals understand and develop effective data-driven cybersecurity strategies for their organizations.
In this edition, you’ll examine long-term trends in vulnerability disclosures and exploitation, regional differences in malware infections and the socio-economic factors that underpin them, and how ransomware evolved from an obscure threat to the most feared threat in cybersecurity.

71 percent of organizations may have been breached and not know it
A new survey of over 2,000 IT security analysts finds that 71 percent admit their organization may have been compromised and they don't know about it yet.
The study, from Vectra AI, details how analysts are being overwhelmed, as they receive 4,484 alerts on average per day, but can't cope with 67 percent of them. This leads 97 percent to worry that they'll miss important security events.
Data bias -- the hidden risk of AI and how to address it [Q&A]
Artificial intelligence is generally only as good as the data that it's trained on. However, when data is collected and used in the training of machine learning models, the models inherit the bias of the people building them, producing unexpected and potentially harmful outcomes.
We spoke to Matthieu Jonglez, VP, technology at Progress, to discuss the company's recent research around this topic and what organizations can do to reduce bias.
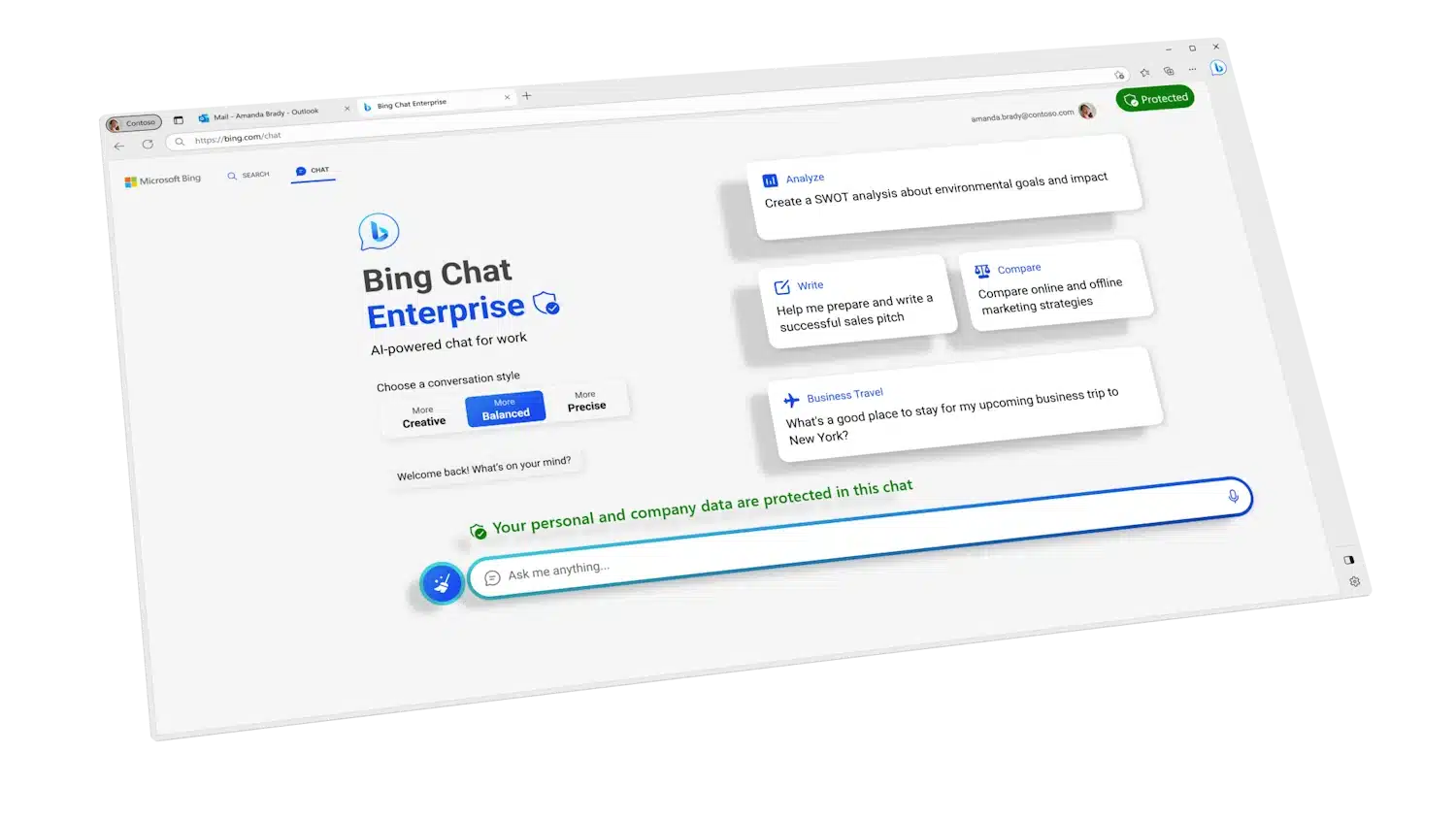
Microsoft 365 Copilot is going to be costly for enterprise and business AI users
As Microsoft, like just about every other technology company, continues to embrace artificial intelligence, there is a lot of interest in the slew of AI-powered tools that are emerging. One of the most intrigue-inspiring tools is Microsoft Copilot.
We've already seen signs of this generative AI utility in the preview builds of Windows 11, and while there is a great deal of anticipation from home users, Microsoft is setting its sights on businesses and the enterprise. At its Inspire 2023 event, the company has revealed more about its plans, including details of pricing.

Forget Winamp -- the ass-kicking Plexamp music player from Plex is now free
For those of a nostalgic bent, the recent revival of Winamp caused flutters of excitement. But for anyone who is uninterested in whippin' that llama' ass, Plex has just announced that its own music player, Plexamp, is now available free of charge.
Previously only available to paying Plex subscribers, the Winamp-inspired Plexamp was the fruit of Plex Labs -- the company's experimental playground for its developers. The standalone music player app has now been unshackled, and is free for all Plex users on iOS, Android, macOS, Windows and even Linux.