That Facebook account verification email in your inbox is a scam
If the scary email or app notification, and subsequent webpage, is to be believed, you have only a few days to verify your Facebook account or you’ll be out of luck. But don’t worry, a few days later you will magically get a few more days to verify, and so the scam goes.
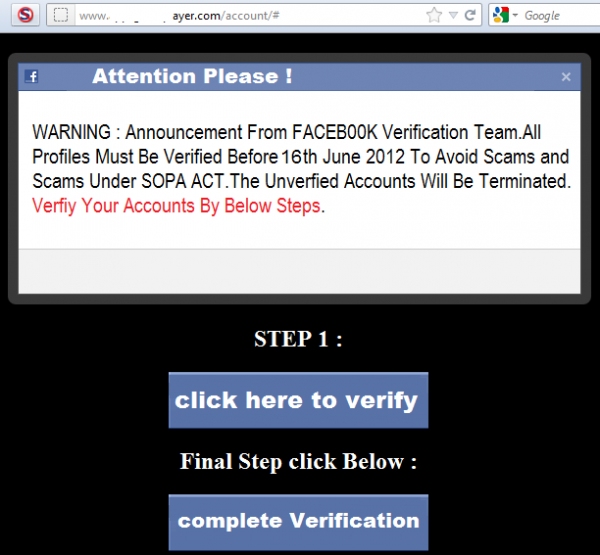
A Twitter follower with the handle of @chasapple sent us a tip on an app message they received, here’s a screenshot of what happens if you clicked the link.
Notice how target-word-rich this example is: There is scary sounding language about the SOPA ACT (and a few misspelled words and syntax errors, a tip the author probably doesn’t speak English as a first language). The call to action is in RED, apparently for added effect. The second thing to note is that the website is definitely NOT facebook.com, but some other domain name, which clearly wouldn’t be a host of an official notification with the ability to suspend your account.
Notice also that the Firefox NoScript add-on, which I have enabled on my system, caught 13 different scripts trying to execute when the page loaded. Along with a mix of ad revenue sites, there were various other scripts as well. Also, both buttons would lead a user to the same link, and potentially set them up for a host of ensuing nastiness no matter which one chosen.
It seems that tapping into the vast pool of over 900 million Facebook users is a favorite strategy among scammers these days, and this is no exception. But as my friend Randy Abrams has pointed out for some time, much of the nastiness could be averted simply by educating/imploring users not to click on suspicious-looking emails. The same is true of apps these days. The problem, he opines, is that the average user doesn’t really have a clear sense of what a suspicious-looking email/app is, and how to tell the difference between legitimate ones and scams.
While user education is an ongoing challenge, the simple version is to tell users to visit a website directly through their web browser and navigate from there, rather than clicking on an email/app link. But it’s not so simple in practice as our inboxes are exploding with email messages these days and the time to take a few extra steps can be hard to carve out. But it takes a lot longer to respond to having your account compromised, so there’s the tradeoff. It’s also a good idea to install script blocking technology in case the temptation to click on links is too strong, then add domains like this one to a network-based blacklist.
Reprinted with permission.
 Cameron Camp is a researcher for global security provider ESET and has played a critical role in building the ESET North America Research Lab. Cameron has been building critical technology infrastructures for more than 20 years, beginning as an assembly language programmer in 1987 and eventually becoming an evangelist for Linux and open-source technologies with an emphasis on the security sector. Prior to joining ESET, he founded Logical Web Host in 1998, a data-driven web services company.
Cameron Camp is a researcher for global security provider ESET and has played a critical role in building the ESET North America Research Lab. Cameron has been building critical technology infrastructures for more than 20 years, beginning as an assembly language programmer in 1987 and eventually becoming an evangelist for Linux and open-source technologies with an emphasis on the security sector. Prior to joining ESET, he founded Logical Web Host in 1998, a data-driven web services company.