Winning the race against the threat of emerging vulnerabilities

Zero-day vulnerabilities are frequently reported on, but remain a major challenge for organizations, especially when it comes to quantifying the real threat posed by an unpatched instance of a vulnerability.
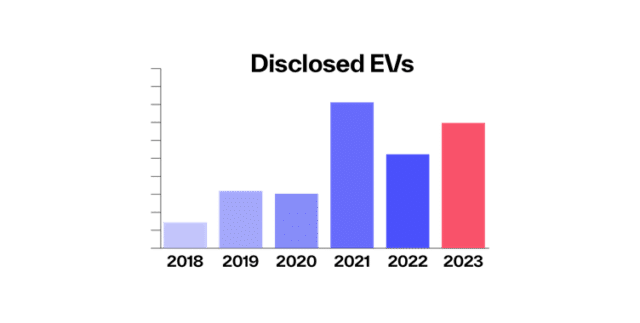
In 2023 the number of disclosed zero-days, or emerging vulnerabilities (EVs), increased from the previous year, rising from 55 in 2022 to 69 in 2023. While this wasn’t as high as the record in 2021 (with 81 disclosures) the prevalence of zero-day vulnerabilities has been rapidly trending upwards over the last 5 years. To stay ahead of the potentially devastating impact of being breached via an emerging vulnerability, organizations must be aware of how to stay ahead of attackers.
The Zero-Day Race
When a zero-day vulnerability is disclosed, it starts a race between sophisticated threat actors and the security response capabilities of affected organizations. If attackers can identify exploitable instances of the vulnerability in a company’s infrastructure or in the infrastructure of a third party that the company is connected to, it can result in a breach with devastating consequences. The average cost of a data breach in damages rose to $5.4 million in 2023, a number that has also been trending upward in recent years.
To counteract this threat, the presence of emerging vulnerabilities must be immediately identified by affected organizations, and remediated before attackers can exploit them. Timing is key.
Unfortunately, many organizations struggle with simply identifying how and where in their digital infrastructure EVs are leaving them open to attacks. EVs can be exploited within an average of 14 days, so modern organizations must be able to respond even faster to patch and remediate these threats.
Patching cadences remain notably low, however, even in enterprise organizations. In one example, the WS_FTP vulnerability (CVE 2023-42659) that was disclosed in late September of 2023, we observed that over 50 percent of organizations across the IPv4 space still had unpatched and vulnerable instances over a month after the disclosure. When compared to the above cited average of 14 days that it takes for attackers to exploit these vulnerabilities, many organizations are clearly still lagging behind.
Staying Ahead of Attackers: Patching and Vulnerability Remediation
As dangerous EVs can be, staying ahead of the threat is far from impossible. The first step in defending your organization from a newly disclosed EV is awareness: a security response team must be able to quickly identify all the assets within a digital infrastructure that host instances of the affected software, hardware or service.
To do this, you must be able to maintain a comprehensive view of your digital ecosystem through a “footprint” or mapping of your externally visible IT infrastructure. Good software and service inventory practices can be the key in identifying which systems are affected by a vulnerability once it is disclosed.
The Common Vulnerability Scoring System (CVSS) serves as a valuable tool in aiding organizations in determining the severity of disclosed vulnerabilities. It can form the backbone of an assessment, providing a way to capture the principal characteristics of a vulnerability and produces a numerical score to reflect its severity. However, one significant drawback is that the evaluation and publishing process can take days or even weeks. By the time CVSS scores are published, a staggering 65 percent of vulnerabilities are already being exploited.
Nevertheless, CVSS scores are still important prioritization tools for triaging and determining the need for patching a specific vulnerability, especially if patching is a decision that must be weighed against important business disruptions and service downtime.
Some general best practices for mitigating emerging vulnerabilities include:
● Ensure timely and effective patching across organizations and their third-party ecosystem. Patching safeguards businesses, organization and provides a defense for those engaging with that organization.
● Leverage continuous monitoring services to identify vulnerable instances of newly disclosed vulnerabilities in third parties to ensure that they are aware of those instances.
● Following up with third parties to confirm patching and vulnerability closures.
● Prioritize patching vulnerabilities on externally-facing assets.
● Ensure visibility and cataloguing of all digital assets, including inactive assets such as parked domains.
Getting a Head Start
The need to rapidly identify and mitigate zero-day threats will only increase as time goes on. As highlighted in the case of the WS_FTP vulnerability, many organizations are still struggling to stay ahead of attackers, largely due to the inability to promptly identify and remediate them. This is doubly true for vulnerabilities in their third-party ecosystems, where a breach can have equally devastating consequences.
For organizations that face this looming threat, modern third-party cyber risk monitoring solutions can assist in both rapidly identifying and alerting on the presence of the externally visible emerging vulnerabilities in both client environments and in your third-party suppliers.
Using technology that can immediately predict the severity or score of new common vulnerabilities and exposures (CVEs) will enable organizations to remediate and mitigate against these vulnerabilities on the same day they are announced.
When timing is key, adopting robust, comprehensive approaches to dealing with emerging vulnerabilities is essential for organizations to protect their digital infrastructure.
Image credit: Profit_Image / Shutterstock
Jon Leather is Head of European Supply Chain Defense Advisory at BlueVoyant.