PDC 2008: Windows 7 will add a 'volume knob' to UAC
Will users feel better about Windows 7 when they have the option of turning off one of Vista's least understood features? Or will they instead make the attempt to understand it? That's the problem which Microsoft's Mike Nash is now facing.
LOS ANGELES - Since the original RTM version of Windows Vista, a Registry-based switch has existed for changing the running state of User Account Control -- the feature that stops processes from performing tasks that haven't been launched by human users. So even today, it's feasible, albeit not easy, to turn up the volume and have UAC prompt for passwords (as was originally planned in the early betas), or turn it off.
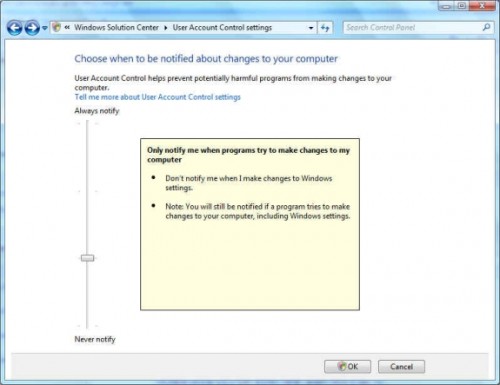
With Windows 7, the current plan is for at least four varying states of operation. But this time, rather than hide the setting in a Registry key that users of the Home SKUs won't be able to change without REGEDIT, we learned on Monday at PDC that users will be able to change their UAC settings directly, from a Control Panel applet.
That said, Microsoft's Vice President for Design and Development for Windows 7 -- the man who, in his previous job as VP for Security, spearheaded its implementation -- would rather you think twice before pulling this switch.

"It had to be done," Nash told us Tuesday, referring to the Vista feature he once championed, and which others -- myself included -- trumpeted as a sign of Microsoft's redoubling of its attention towards security. "We know that machines that run Vista are 60% less likely to be infected than machines that run XP. Is it all UAC? No, but it was enough UAC that [it made an impact]. It caused the ecosystem to realize what it meant to build applications that ran in Standard Mode; it helped us to refine the experience."
But the problem ended up being the experience: While it demonstrably made Vista more secure, it didn't make users feel more secure, and it didn't help users get everyday work done.
"My biggest regret is that we should've focused on that more within the Vista timeframe," Nash said. "It's an example of an area where we made a change late enough that the ecosystem didn't have a great chance to respond to it."
Actually, the ecosystem -- the collection of third-party developers and vendors who support the Windows-driven PC -- had plenty of time to prepare for the onset of UAC. What they didn't have was the incentive. As it turned out, Nash said, "it churned so much late in the game."
What hasn't been said very much in the discussion of User Account Control is the role that applications -- particularly those not made by Microsoft -- play in invoking those UAC prompts, sometimes needlessly. The prompts are supposed to be invoked whenever a process that's normally running as a standard user requires administrator privileges. And the whole point of insisting that more Windows users run with standard privileges is so that the misuse of their accounts wouldn't lead to bestowing privileges upon processes that shouldn't have them.
"Let's remember when people are getting prompts. Primarily today, they're getting prompts on setup, and a lot of that was for the older applications that weren't written with the knowledge of running as a standard user," explained Nash. "So a lot of work we had to do originally with Vista is to say, a lot of applications when they first turned on, they say, 'Am I running in admin mode?' If the answer is no, they shut down. We know the reason they were asking that question wasn't because they needed to run in admin mode; they were actually asking that question because the vendor didn't want to test them in anything but admin mode."
In other words, developers of setup routines and other processes simply found it easier to require admin mode than to adopt the practices that made it possible for them to run as standard users -- something Nash implied was, and is, quite feasible.

"So our original approach for a lot of the applications that we profiled was to say, 'Look, this application is only querying...as a useless test, so we're going to tell them they are admins when they're not.' But never really let them do anything that was privileged without being privileged. So it's really about being very pragmatic here."
Changing the system so that processes would quit requesting privileges when they didn't need them, required cooperation from, as they say, the ecosystem. That's one reason, Nash told us, why the "pre-beta" of Windows 7 was released now, to start -- or, more accurately, to reboot -- the process of bringing the ecosystem up to speed.
"So our ecosystem partners can get a chance to start learning about Windows 7, and then start building for Windows 7," he said, "And then when the beta comes, it'll be feature-complete, which means the things that happen post-beta are bug fixes and edge conditions, versus adding features and making the ecosystem deal with new things."
Of course, the problem now could be that third parties may presume Windows 7 users will turn UAC off, or as will be their prerogative come RTM, down. So one very real possibility in the final presentation of this lever mechanism for the UAC Control Panel is that it clearly represents to the user the tradeoffs she may experience when she sets UAC to anything less than "on."
"My analogy is, I had a friend who had a house who put in a nice alarm system, but she never knew how to set it, so she never set it. So the least secure house is the one with the alarm off," he said. "The least secure system here is the one where you're blowing by security. So if the security is so annoying that you can't use it, then people turn it off."
Thus the option will be there, and although it's not Mike Nash's favorite element of Windows 7, it has a purpose which he's fine with, at least for now:
"It really goes to this theme of personalization. If you want to work in a way where you're a developer, you're a gamer, you just don't want to get bugged, fine. Different people know the risk, and for most people, we'll put in what's most appropriate for them. If we want to be in a place where we're helpful and improving safety...but our approach to improving safety is so in-their-face that they can't use it, then it's not helpful at all."