Google has broken SHA-1 encryption
After two years of research, Google has shown that it has successfully broken SHA-1 encryption. The company is yet to release details of how it achieved the first SHA-1 "collision", but has released a proof of concept.
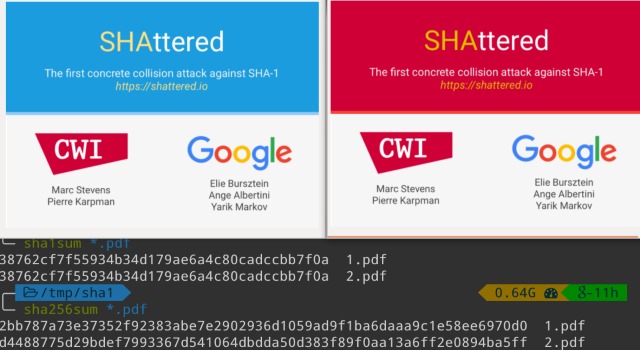
In keeping with its own disclosure policy, details of how the encryption was effectively broken will be released after 90 days. In the meantime, you can take a look at two specially-crafted PDF files that have identical SHA-1 hashes but different content (the definition of a collision).
The implications of the revelation are perhaps not as far-reaching as some people might expect. While once very popular, SHA-1 is now far less common, with experts having predicted the day the technology would be cracked quite some time ago. There has been a general move away from this form of encryption in recent years, but Google says that "we hope our practical attack on SHA-1 will increase awareness and convince the industry to quickly move to safer alternatives, such as SHA-256."
On the Shattered.it website created to publish the SHA-1 collision news, Google says:
We have broken SHA-1 in practice.
This industry cryptographic hash function standard is used for digital signatures and file integrity verification, and protects a wide spectrum of digital assets, ranging credit card transactions, electronic documents, open-source software repositories and software updates.
It is now practically possible to craft two colliding PDF files and obtain a SHA-1 digital signature on the first PDF file which can also be abused as a valid signature on the second PDF file.
For example, by crafting the two colliding PDF files as two rental agreements with different rent, it is possible to trick someone to create a valid signature for a high-rent contract by having him or her sign a low-rent contract.
Creating the collision was no small feat. Google shares details of the technicalities of what was involved:
- Nine quintillion (9,223,372,036,854,775,808) SHA1 computations in total
- 6,500 years of CPU computation to complete the attack first phase
- 110 years of GPU computation to complete the second phase
In practical terms, breaking SHA-1 is unlikely to have much impact on general security. All modern web browsers issue a warning when visiting a site that uses the encryption, so only older systems that have not been updated for a few years should be affected.