Serious app permissions flaw will not be fixed until Android O, leaving users at risk
The security of Android has been questioned many times, but the general thinking is that installing apps from Google Play offers a decent level of protection. But research by Check Point shows that this is not the case due to a flaw in permissions.
The permission model used by Google grants apps installed from the Play Store extensive access, and opens up the risk of malware, ransomware and other threats. Google is aware of the problem, but does not plan to address it until the release of Android O, meaning that an unknown number of apps pose a risk to millions of users.
Since Android Marshmallow, Google has grouped together permissions so that those considered "dangerous" are only granted during runtime, and users must provide permission for them to run. But this does not account for all of the exploitable permission types, as Check Point explains:
In addition to the "dangerous" permissions, another category exists, which contains a single permission -- SYSTEM_ALERT_WINDOW. Unlike the other permissions, to grant it, the user must go through several menus (Settings -> Apps -> Draw over other apps) and manually allow an app to use it.
The reason SYSTEM_ALERT_WINDOW is unique is the extensive capability it withholds, by enabling an app to display over any other app without notifying the user. This entails a significant potential for several malicious techniques, such as displaying fraudulent ads, phishing scams, click-jacking, and overlay windows, which are common with banking Trojans. It can also be used by ransomware to create a persistent on-top screen that will prevent non-technical users from accessing their devices. According to our findings, 74 percent of ransomware, 57 percent of adware, and 14 percent of banker malware abuse this permission as part of their operation. This is clearly not a minor threat, but an actual tactic used in the wild.
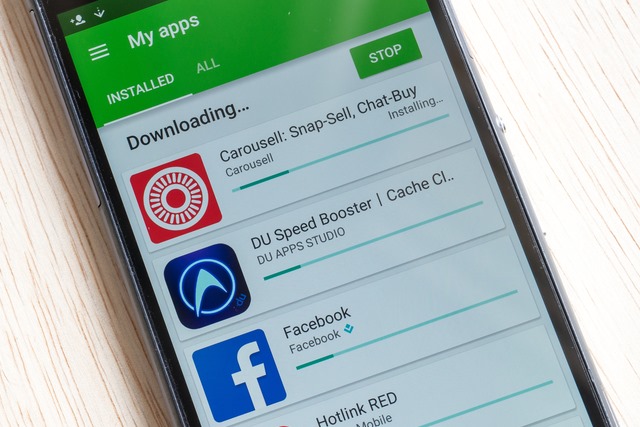
While this permission is potentially problematic, it also has legitimate uses -- such as by Facebook Messenger's chat heads. As such, in Android 6.0.1, Google applied a patch that meant the SYSTEM_ALERT_WINDOW permission could be automatically assigned to apps installed from Google Play, both innocent and dangerous. Check Point says that this effectively allows them to bypass Google's previous security mechanism.
In Android O, Google plans to introduce a new permission TYPE_APPLICATION_OVERLAY which will overcome the problem -- but this is some time away. In the meantime, Check Point recommends taking care with apps and permissions, and suggests installing security software just like on a PC.
Image credit: N Azlin Sha / Shutterstock