Symantec battles the ZeroAccess botnet
 Information security specialist Symantec has announced on its Security Response blog that it has taken the first steps towards combating the ZeroAccess botnet. The company has "sinkholed" more than half a million bots -- making a serious dent in the number of bots under attacker control. Symantec is actively working with ISPs and CERTs (Computer Emergency Readiness Teams) worldwide to help get infected machines cleaned up.
Information security specialist Symantec has announced on its Security Response blog that it has taken the first steps towards combating the ZeroAccess botnet. The company has "sinkholed" more than half a million bots -- making a serious dent in the number of bots under attacker control. Symantec is actively working with ISPs and CERTs (Computer Emergency Readiness Teams) worldwide to help get infected machines cleaned up.
ZeroAccess has a highly technical and sophisticated infrastructure. It uses a peer-to-peer architecture giving the botnet a high degree of redundancy with no central command and control server. It also uses various advanced methods to survive on infected machines. It uses click-fraud and Bitcoin mining to carry out two revenue generating activities potentially earning millions of dollars a year.
Symantec engineers have been studying ZeroAccess since March which allowed them to identify a weakness that offered a way to sinkhole the botnet. Sinkholing is a technique that uses DNS servers to give out false information preventing infected PCs from communicating with each other. When a new version that addressed this flaw began to roll out at the end of June Symantec decided to act.
"Having seen the changes beginning to roll out, and with a viable plan in place, we were faced with an option: start our operations now or risk losing the initiative. On July 16, we began to sinkhole ZeroAccess infections. This operation quickly resulted in the detachment of over half a million bots and made a serious dent to the number of bots controlled by the botmaster," the blog entry says.
Disrupting peer-to-peer botnets is hard since they're designed to be resilient, but Symantec has shown that it is possible, which is good news for the future. Just how much of an economic impact ZeroAccess has you can see on the infographic below.
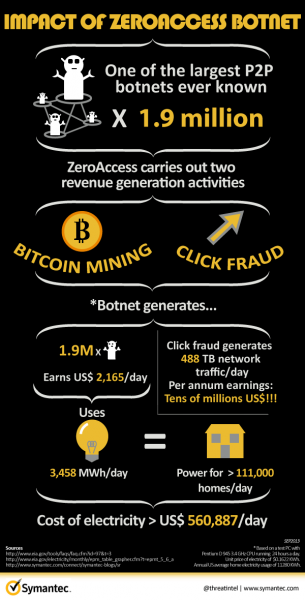
Photo Credit: Pavel Ignatov/Shutterstock