DDoS traffic soars and the bots get cleverer
New research by website security specialist Incapsula looks at the impact of DDoS traffic on the internet with data collected over a five month period looking at over 154 million DDoS bot sessions.
It reveals some startling statistics, the main one being that at the application level DDoS bot traffic is up by 240 percent. More than 25 percent of all botnets are located in India, China and Iran, whilst the US ranks fifth in the top ten attacking countries.
The attack landscape is interesting too. 29.9 percent of DDoS bots can execute JavaScript and 40 percent of botnets attack more than 50 targets per month.
At network level, large scale SYN floods account for over half (51.5 percent) of all attacks and almost 81 percent of attacks are multi-vector threats.
The results show a shift towards so called "hit and run" attacks, relying on short bursts of traffic at frequent intervals, designed to exploit vulnerabilities in protection systems. The growth in multi-vector attacks is also being used to create "smokescreens" where one attack creates noise to divert attention away from the main vector. The first part of 2014 has also shown a rise in NTP (Network Time Protocol) amplification attacks which in February became the most commonly used method of large scale DDoS attack.
Whilst the volume of attacks is increasing, DDoS bots are becoming more sophisticated too. In the fourth quarter of 2013, Incapsula reported the first encounter with browser-based DDoS bots that were able to bypass both JavaScript and Cookie challenges -- the two most common methods of filtering bots. This trend has continued into 2014 with 30 percent of the encountered bots able to accept and store cookies.
In order to infiltrate systems bots are using spoofed user-agents. These help to bypass low-level filtering solutions, based on the assumption that bots which identify themselves as search engines or browsers won't be screened out.
You can read more and download the full report on the Incapsula blog or see an overview of the findings in the infographic below.
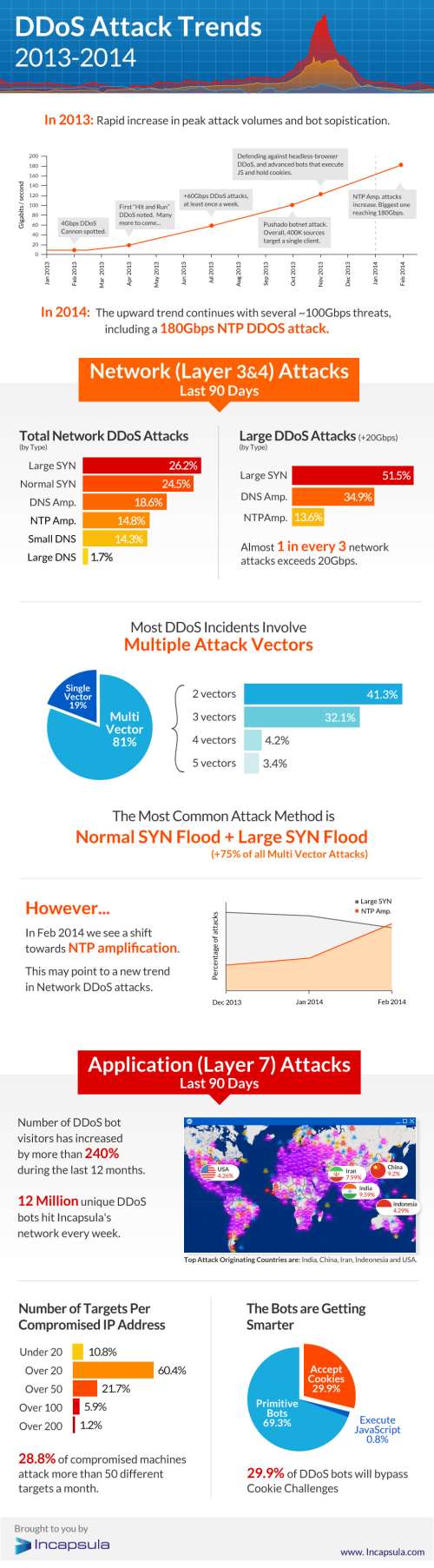
Photo Credit: Duc Dao / Shutterstock