Employees' bad habits could put businesses at risk
Individuals are frequently the weakest link in the chain when it comes to protecting business data, often through simple day-to-day lapses that can have a serious consequence.
Atlanta-based IT Services company Leapfrog Services has identified five common bad habits of employees that businesses need to manage in order to guard their information.
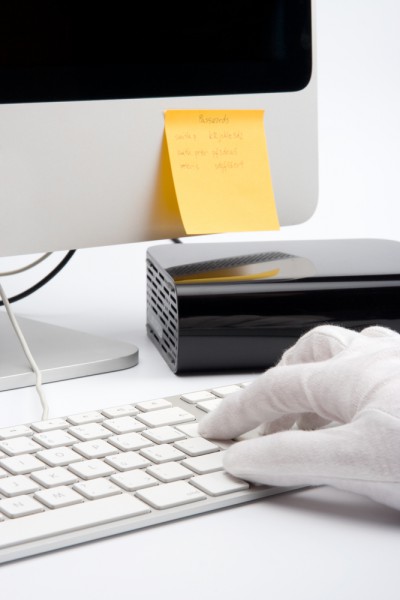
Poor password practices are top of the list. If employees fail to log out when they leave their desks, or write passwords on sticky notes attached to the monitor, they're putting company data at risk. It's important to establish and enforce security procedures especially if workstations are shared.
Updating social media may seem like a harmless activity, but badly-judged comments about products, clients or even colleagues can have serious consequences. Enterprises need to have a clear social media policy which outlines what can be shared and what needs to be kept confidential.
Sending texts may be convenient, but if employees use personal devices for business it risks losing the security that's in place for company systems. As a result something like sending links, images and quick thoughts by text may fall outside of the IT department's control or access.
Social engineering is a problem across all businesses and phishing emails do make it through to inboxes occasionally, even with protection in place. Opening an email mindlessly may be all it takes for hackers to infect a system or company network. Whilst it's important to keep security systems up to date, education is vital to make sure staff are aware of the potential threat posed.
Finally, seemingly helpful working methods such as using public clouds to share files or working via insecure home networks or access points can put company data at risk. If employees are allowed to work away from the office or on their own devices this needs to be backed up by security systems that keep the company safe but don't compromise convenience.
"Lines are now blurred between using company computers vs. personal devices for work," Leapfrog’s CTO Trey Hawkins says, "And as we learned with recent celebrity hacking incidents, even cloud-based platforms can be compromised. It is critical to have rules in place that protect company information".
Image Credit: Jirsak / Shutterstock