Best-selling router ships with vulnerable firmware

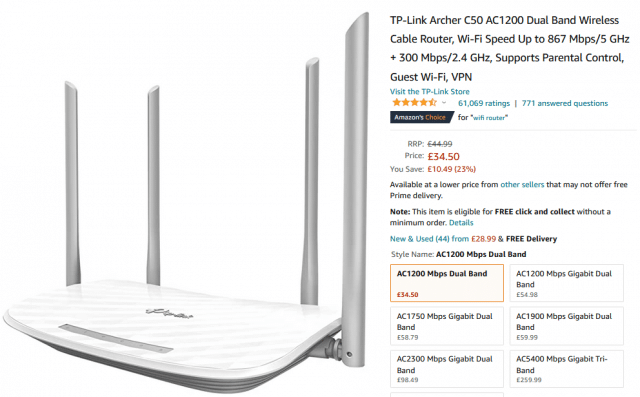
Researchers at CyberNews have uncovered security flaws within the default firmware and the web interface app of the TP-Link AC1200 Archer C50 (v6) router.
The router -- an 'Amazon's Choice' product -- is shipped with outdated firmware that is vulnerable to dozens of known security flaws and could put users at risk of man-in-the-middle and Denial of Service attacks.
Among the flaws WPS is enabled by default, potentially allowing threat actors to brute-force the router. Session tokens are not deleted server-side after logging out of the router app and are accepted for subsequent login procedures.
The router's administrator credentials and configuration backup files are encrypted using weak protocols and can be easily decrypted by attackers. Plus the default version of the router's web interface app suffers from multiple bad security practices and vulnerabilities, including clickjacking, charset mismatch, cookie slack, private IP disclosures, weak HTTPS encryption, and more.
CyberNews notified TP-Link of the problem on July 18. TP-Link states that the company will force firmware updates on the affected devices, while the owners will receive 'relevant notifications' about these updates via their management interface, 'whether they manage the device through the web terminal or the mobile app Tether.'
You can read more about the issue on the CyberNews site.
Image credit: Narith Thongphasuk38 / Shutterstock