
Remote working still presents security problems one year on
Even after a full year of remote work, many enterprises are still concerned about securing their off-site users according to a new study from cloud security company Bitglass.
The biggest remote work security concerns come from data leaking through endpoints (68 percent), users connecting with unmanaged devices (59 percent), and access from outside the perimeter (56 percent).

Passwords are bad for online business
According to a report from Transmit Security, more than half of consumers have stopped using a website because of the login process and more than 87 percent have been locked out of an online account because of an error-ridden password process.
The survey of 600 US consumers finds organizations are losing potential customers and a substantial amount of revenue because of their dependency on traditional password systems and outdated customer authentication models.

Cloud workloads increase but security concerns remain
A new study from the Cloud Security Alliance (CSA) and cloud security company AlgoSec finds that over half of organizations are running 41 percent or more of their workloads in public clouds, compared to just a quarter in 2019.
But 11 percent of respondents have reported a cloud security incident in the past year with the three most common causes being cloud provider issues (26 percent), security misconfigurations (22 percent), and attacks like denial of service exploits (20 percent).

One in five healthcare files is open to all employees
A new report from Varonis reveals some startling statistics about healthcare data, with almost 20 percent of files open to all employees in an organization.
In addition the average healthcare organization has over 31,000 files -- including those that include HIPAA-protected information, financial data, and proprietary research -- open to everyone.

2020 sees cybercriminals turn to Ransomware 2.0
Historically ransomware has relied on encrypting data and then demanding money in order to release it.
But a new report from F-Secure shows that 2020 has seen an increase in ransomware that also steals data, giving the attackers more leverage over their victims. If organizations first refuse to pay a ransom to decrypt their data, attackers threaten to leak the stolen information, increasing pressure on victims.

The growing risk from critical infrastructure cyberthreats [Q&A]
The more reliant businesses become on technology the more risk they face from a range of cyberthreats. This is especially true when it comes to critical infrastructure as it's an attractive target for nation state and other attackers.
We spoke to James Carder, chief security officer and vice president of labs at SIEM platform LogRhythm to discover more about critical infrastructure threats and how to guard against them.

Shifting attack patterns boost uptake of zero trust
As enterprises move more data to the cloud and grant higher levels of third party access, attackers are increasingly targeting non-traditional user populations that may not be adequately protected.
But a new survey of CISOs from identity specialist CyberArk shows that security teams are shifting to zero trust in response to these changing attack patterns.

Cryptocurrency scams almost double in 2020 with more on the way
Increases in the value of cryptocurrencies last year coupled with a rise in mainstream acceptance of Bitcoin has led to 400,000 crypto scams being created in 2020, a 40 percent increase compared to 2019,
A new report from Bolster, a deep learning-powered, next generation fraud prevention company, forecasts a further increase of 75 percent this year based on current levels of suspicious activity.

Digital first census raises security concerns
This year for the first time the UK's ten yearly census -- used to collect information to determine future government policy and spending -- is 'digital first' with people encouraged to fill in their returns online rather than use a paper form.
But research conducted by YouGov for security analytics and automation company Exabeam finds that many people are worried about how the data will be stored and used.

Security and privacy knowledge is good but bad habits persist
New research from NordVPN finds that people around the world generally have good security and privacy knowledge, but still indulge in bad habits.
NordVPN ranked 21 countries by their performance, placing Germans at the top and -- perhaps surprisingly -- the Japanese at the bottom.
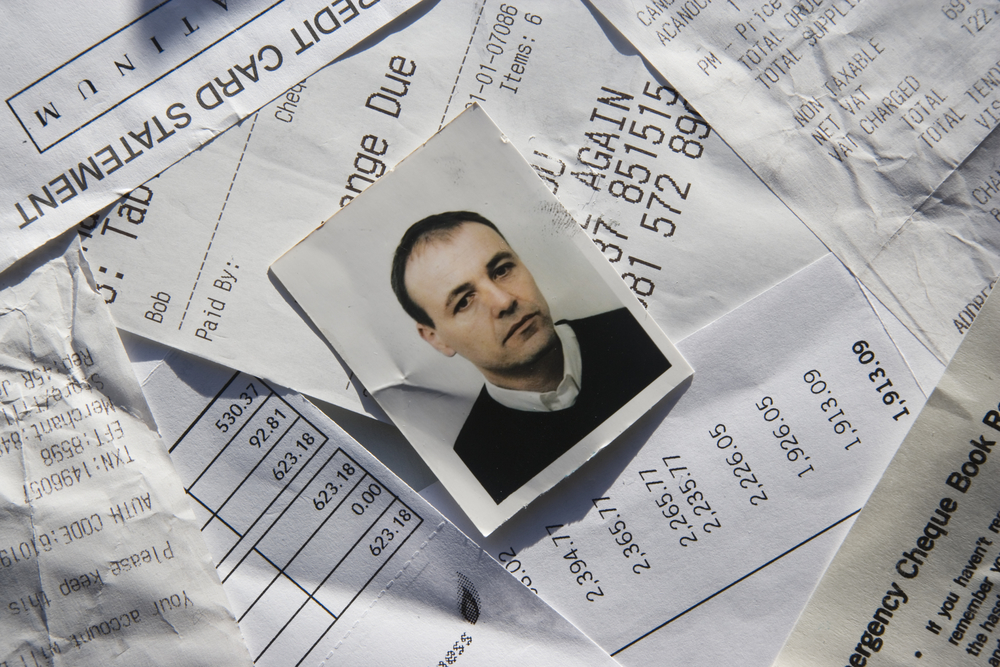
SentiLink's new ID Theft Scores targets stolen identities used to open financial accounts
Security has become slightly more difficult these days given that many people are now working at home and online. That’s just the beginning of the headaches for firms.
SentiLink, a leading security company, is trying to fight back against identity fraud with a new ID Theft Scores program. This is designed to complement its Synthetic Scores that are already in place and used by used by many top financial institutions in the US.

A year on from the home working surge, cybersecurity practices are still inadequate
A new report from cybersecurity firm PC Matic finds that one year on from the start of the COVID-19 pandemic, nearly 35 percent of Americans are still working from home.
However, the study of more than 5,800 people across the US finds less than 10 percent of respondents are provided with an antivirus software solution for the personal device they use for work purposes.

How AI can help prevent 'catastrophic forgetting' of malware data
With large numbers of new samples appearing every day the old signature-based methods of malware detection have become unwieldy.
AI can learn from millions of samples, but if it uses all samples for optimum detection that means slower learning and updates. The alternative is to use only select samples to keep up with the rate of change of malware, but this runs the risk of 'catastrophic forgetting ' of older patterns.

Talent shortage impacts security awareness efforts
Over three-quarters of security awareness professionals are spending less than half their time on security awareness, according to a new report from SANS.
This underlines the fact that awareness training is often a part-time effort, commonly assigned to staff with highly technical backgrounds but who may lack the skills needed to effectively engage their workforce in simple-to-understand terms.

Threat data helps enterprises strengthen security
Threat data feeds can help enterprises strengthen their cybersecurity posture, according to a new report from Ponemon Institute, sponsored by IT services company Neustar.
A majority (79 percent) of the more than 1,000 security professionals taking part in the study say threat data feeds are essential to their organization's ability to achieve a strong cybersecurity posture, and 55 percent rate the quality of their threat feeds' ability to pinpoint cyberthreats as very high.
