
Forcepoint SASE solution helps protect enterprise clouds
Secure Access Service Edge (SASE) technology is increasingly being used to enable secure and fast cloud adoption, helping ensure both users and devices have safe cloud access to applications, data and services from anywhere.
Cybersecurity company Forcepoint is entering this market with a new suite of SASE solutions, including a Cloud Security Gateway and zero trust Private Access features.
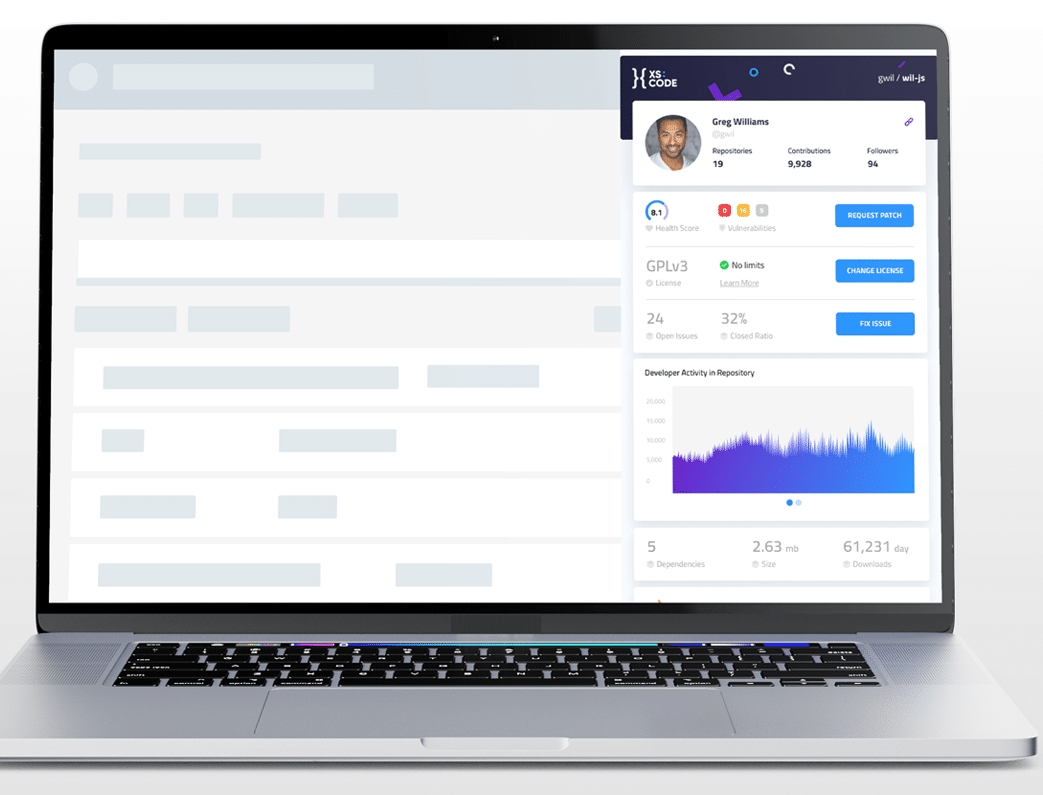
New Chrome extension provides security check on open source code
Developers frequently make use of open source components in order to speed up projects and save them having to reinvent tasks. But this can lead to the introduction of hidden security risks.
Now though open source marketplace xs:code is launching a new, free Chrome extension, xs:code Insights, which provides users with intuitive, in-depth analytics on open source repositories, including repository score, security analysis, maintenance and activity status, reviews, ratings and more.

Gmail to start showing authenticated brand logos to fight phishing scams
The DMARC standard for email verification has been around for several years. Domain-based Message Authentication, Reporting and Conformance has the potential to rebuild trust in email communications plagued by spam and phishing.
Google's announcement this week that it's about to start piloting the display of authenticated brand logos in Gmail could mark the start of the technology's mainstream adoption.

How traffic analysis can help protect business networks [Q&A]
One of the biggest challenges that cybersecurity teams face at the moment is alert noise which can blind them to real threats.
Corporate performance management (CPM) specialist Prophix Software recently chose to adopt a network traffic analysis (NTA) solution to address this issue. We spoke to Kristofer Laxdal, the company's director of information security to discover why it chose invest in NTA technology and what benefits it's seeing.

We're too boring to be hacked say millennials
Research into changing 'digital comfort zones' during the pandemic shows that 37 percent of millennials think they're too boring to be a victim of cybercrime.
The study from Kaspersky finds that millennials are now spending almost two extra hours online every day and almost half say this has made them more aware of their digital security, with 36 percent saying that they should be doing more to strengthen it.

Organizations are not doing enough to improve SOCs
The average security operations center (SOC) has considerable room for improvement according to a new report from automation and response platform SIRP Labs.
Almost a third (29 percent) of respondents believe missed alerts due to high volumes are a significant, even a serious, problem. In companies of 1,000-2,500 employees the figure rises to 46 percent.

Cybercriminals use new techniques to target eCommerce sites
With bricks and mortar stores largely shut down for much of the first half of 2020, it’s no real surprise to find that cybercriminals have been targeting eCommerce sites.
New research from IntSights looks at how there has been a rise in cybercriminals targeting eCommerce sites using a variety of attack methods, such as skimming attacks, account takeovers and ransomware.

Hackers to the rescue! UFO VPN user log database leaks online for a second time
Just a week ago, we covered the news that user log files from the VPN service UFO VPN had been exposed. A database of user data appeared online despite the company's claims of having a "strict no-logs policy".
But while security experts took steps to lock down the data and restrict access to it by the middle of this month, earlier this week it transpired that a second, newer UFO VPN database had appeared online, containing even more data. This time, however, hackers came to the rescue with a coordinated "Meow" attack.

Malware attacks down as ransomware increases
The latest Cyber Threat Report from SonicWall shows a 24 percent drop in malware attacks worldwide, while there’s been a 20 percent jump in ransomware globally and a 109 percent spike in the US.
There's also been a 176 percent increase in malicious Microsoft Office file types and a 50 percent rise in IoT malware attacks as cybercriminals seek to use devices as a backdoor to business networks via home workers.
43 percent of employees make mistakes that have cybersecurity implications
A report released today by email security firm Tessian reveals that 43 percent of US and UK employees have made mistakes resulting in cybersecurity repercussions for themselves or their company.
A quarter of employees confess to clicking on links in a phishing email at work, with distraction cited as a top reason for falling for a phishing scam by 47 percent of employees. This is closely followed by the fact that the email 'looked legitimate' (43 percent), with 41 percent saying the phishing email looked like it came from a senior executive or a well-known brand.

Security professionals lack visibility into top threats
According to a new report, 89 percent of security professionals are most concerned about phishing, web and ransomware attacks, but only 48 percent confirm that they have continuous visibility into these risk areas.
The 2020 Cybersecurity 360 Report from Balbix also shows 64 percent of organizations are only, at best, somewhat confident in their security posture, and that the lack of visibility into security is the primary concern for organizations.

Poor privacy practices increase the chances of a data breach
Companies with the worst privacy practices are 80 percent more likely to experience a data breach according to a new study.
Data privacy platform Osano used its evaluation framework to measure the privacy practices of the top 10,000 websites against 163 different factors to develop an Osano Privacy Score.

The internet is becoming more secure -- but only slowly
New research from security analytics and automation company Rapid7 reveals that the security of the internet overall is improving and the number of insecure services such as SMB, Telnet, rsync, and the core email protocols all decreased from the levels seen in 2019.
However, the National/Industry/Cloud Exposure Report (NICER) shows vulnerabilities and exposures still plague the modern internet even with the increasing adoption of more secure alternatives to insecure protocols, like Secure Shell (SSH) and DNS-over-TLS (DoT).

Cyber crisis simulator aims to improve incident responses
While cyberattacks are played out on technology platforms, it's often the effectiveness -- or otherwise -- of the human response that determines how they impact an organization.
It can be hard to prepare teams to deal with the realities of an attack, but Immersive Labs is looking to change that with the launch of its industry first Cyber Crisis Simulator.

How e-signatures are changing the commercial world [Q&A]
The idea of electronic signatures has been around for a while, but their importance has been highlighted by recent changes brought about by the COVID-19 pandemic, meaning signing documents in person may be difficult.
We spoke to Sameer Hajarnis, practice lead for e-signature at digital fraud prevention specialist OneSpan to find out more about adopting e-signatures in the current business landscape, what businesses need to look for and how these technologies can securely enable efficiencies, improve processes, ensure legal compliance and deliver an improved customer experience.
