
Mobile malware incidents increase by 142 percent
According to a new study, 36.5 percent of all organizations have experienced a malware incident on a mobile device in the past year, which represents a 142 percent increase from 2018.
Research from mobile security specialist Wandera finds 57 percent of organizations have experienced a mobile phishing incident, with 60 percent of mobile phishing attacks occurring over HTTPS.

Google may have shared your videos with strangers
If you used Google Takeout to download an archive of your Google Photos content, there's a chance that someone else may have ended up with your videos.
The company has admitted that for a few days in November last year, "some videos in Google Photos were exported to unrelated users' archives". This means that not only could your videos have ended up on a stranger's computer, but also that you may have received random videos belonging to someone else.

Why businesses must be ready for lots more IoT devices [Q&A]
There are expected to be more than 70 billion connected devices by 2025, which means the opportunity for hackers to infiltrate connected devices, and to get onto networks, is going to get much larger.
So how can businesses prepare for this influx, train their staff and get ahead in order to protect their critical data from cybercriminals who are always keen to update their tactics and strategies? We spoke to Jonathan Langer, CEO of healthcare device security specialist Medigate to find out.

Less than a fifth of organizations are effectively stopping cyberattacks
Just 17 percent of organizations worldwide are considered 'leaders' in cyber resilience, meaning under a fifth are effectively stopping cyberattacks and finding and fixing breaches fast enough to lower the impact, according to a new report from Accenture.
Based on a survey of more than 4,600 enterprise security practitioners, Accenture's report looks at how businesses prioritize security, the effectiveness of their current security efforts, and the impact of new security-related investments.

Microsoft Edge has a new 'unwanted apps' download-blocker -- here's how to enable it
Microsoft has introduced a new feature to its Edge browser that blocks "potentially unwanted apps" from being downloaded.
At the moment, the security feature is available in the beta version of Microsoft Edge, but it will also be making its way to the stable version of Chromium-based Edge later this month. Strangely, Microsoft has chosen not to switch on the feature by default.

Microsoft offers up to $20,000 in Xbox bug bounty
Microsoft is no stranger to using bug bounty programs to track down security problems and other issues with its software and services. Now the company has launched an Xbox bug bounty program, offering payouts of up to $20,000 to anyone finding vulnerabilities.
The particular aim of this bounty program is to find issues with the Xbox Live network and services. Microsoft says the amounts it will pay gamers and security researchers who report problems will depend on the severity and impact of the vulnerability, as well as the quality of the submission.

Most antivirus companies will continue to support Windows 7
Microsoft may have dropped Windows 7 like a hot stone, but that doesn't mean everyone is. Recognizing the fact that large numbers of people are going to continue using the aged operating system, most antivirus firms are going to continue to offer support.
Support from the likes of AVG, Avira, Kaspersky and Trend Micro for at least two years is great news for those concerned about the security of sticking with Windows 7. Of course, this doesn't mean that the operating system is entirely safe to use now that it has reached end of life, but with the right software installed, hangers-on can secure their systems somewhat.
New solution allows businesses to find and protect sensitive documents
Modern businesses have large numbers of documents, many of which contain information that is commercially sensitive. But poor file management, incorrect permissions and uncontrolled sharing can put that information at risk.
The unstructured nature of this data makes it notoriously difficult to keep track of. Now though California-based Concentric is launching a new solution to allow enterprises to identify and protect these documents.
How eCommerce fraud is evolving [Q&A]
Online fraud has gained in sophistication in recent years. As consumers have moved to using mobile devices and have come to expect a consistent shopping experience across platforms, so the fraudsters have never been far behind.
We spoke to Michael Reitblat, co-founder and CEO of eCommerce fraud prevention specialist Forter, which recently published its latest Fraud Attack Index, to find out more about the fraud landscape and how businesses can protect themselves.

People are a key element in securing systems
With attackers often targeting individuals and their credentials to gain unauthorized access to accounts, people are increasingly at the center of security.
This is one of the conclusions of a new report from identity solutions provider Okta which finds that when deploying security tools a third of businesses start with a tool focused on protecting their people, as opposed to devices, infrastructure, and networks.
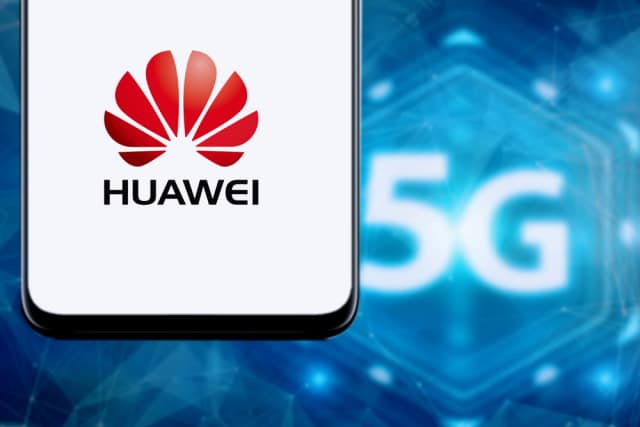
UK ignores US warnings and says Huawei can help build its 5G network
The UK government has announced that -- despite being considered a "high-risk vendor" -- Huawei will be permitted to contribute to the 5G network infrastructure in Britain.
The US recently warned that allowing the Chinese firm to be involved in the rollout of 5G would be "madness", but the UK has chosen to ignore this. Huawei will have limits placed on its contributions, meaning that it will only be able to supply "non-core" elements of the network.

Cisco launches Industrial IoT security architecture
Increasingly the boundaries between operational technology and business networks are breaking down as businesses seek access to the real time data that industrial IoT devices hold.
But that leads to increased risk to critical infrastructure as devices become more exposed. To combat these threats, Cisco is introducing an IoT security architecture that provides enhanced visibility across both IT and OT environments, and helps protect industrial processes.

Hacker demonstrates Remote Code Execution exploit for Windows Remote Desktop Gateway
A self-described "reverser/pwner [and] Windows kernel hacker" has demoed a working exploit for two recently discovered vulnerabilities in Windows Remote Desktop Gateway (RD Gateway).
The exploit takes advantage of the CVE-2020-0609 and CVE-2020-0610 vulnerabilities which have already been shown to make a denial of service attack possible. Now Luca Marcelli has shown how the same vulnerabilities can be exploited in a Remote Code Execution attack.

Avast free antivirus sends browser history to marketers
When you install an antivirus program -- even a free one -- you have a reasonable assumption that it's going to help keep your data safe.
But a joint investigation by Motherboard and PCMag has discovered that Avast's free antivirus is harvesting user data. Although this is supposedly 'de-identified' it is being sold to marketers in a way that can be linked back to an individual.

Breakthrough technology allows voice biometrics to be used at the edge
The use of voice for authentication has been limited in IoT applications and devices because of storage and processing limitations.
But new technology from ID R&D looks set to change that, offering voice biometric optimization with an AI-based SDK of under 1MB, enabling voice biometrics to be implemented at the edge.
