
Google is making it easier to find a safe and reliable VPN
Take a browse through an app store and you will find that there is no shortage of VPN tools to choose from. But which can you trust?
One of the reasons for using a VPN in the first place is to help keep data safe -- but some tools leak information in ways that run completely counter to this. So how do you know which one you should be using? Google has come up with a new way to help guide users towards the safest options,
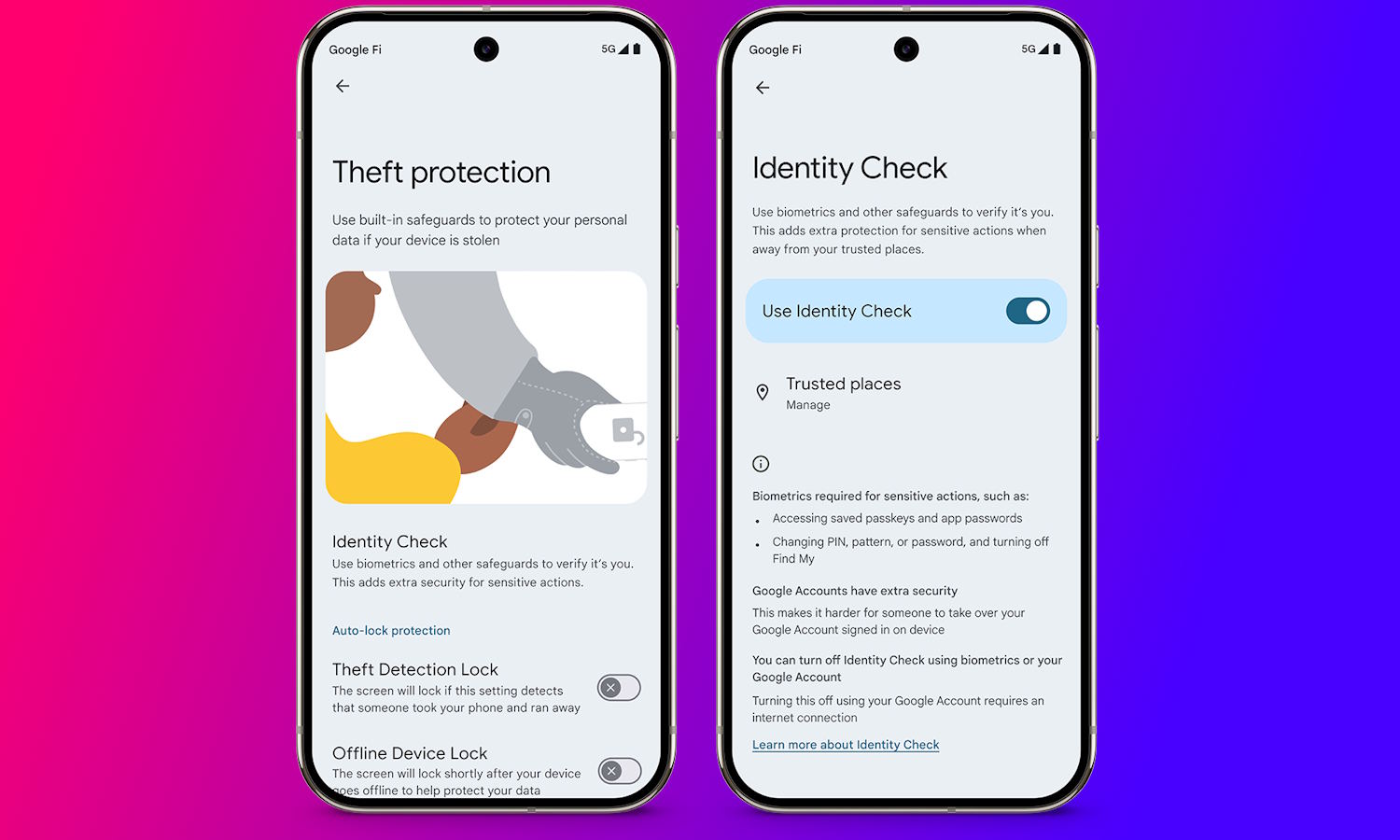
Google launches Identity Check, a new location-based security feature, and completes roll-out of AI-powered theft detection
Theft of mobile devices is a crime that is not going away any time soon. Phones are now completely central to so many aspects of life, and the theft (or loss) is about much more than the monetary value of the device itself. There is great potential for a thief to gain access to a wealth of information via a stolen phone.
This is why the security of mobile devices is so important, and it is why Google is taking steps to limit the impact of theft. A new feature that is starting to roll out is Identity Check, which requires the use of biometric authentication whenever your device is in an unknown or untrusted location. The company is also harnessing the power of artificial intelligence for good, using AI-powered tools to detect thefts.

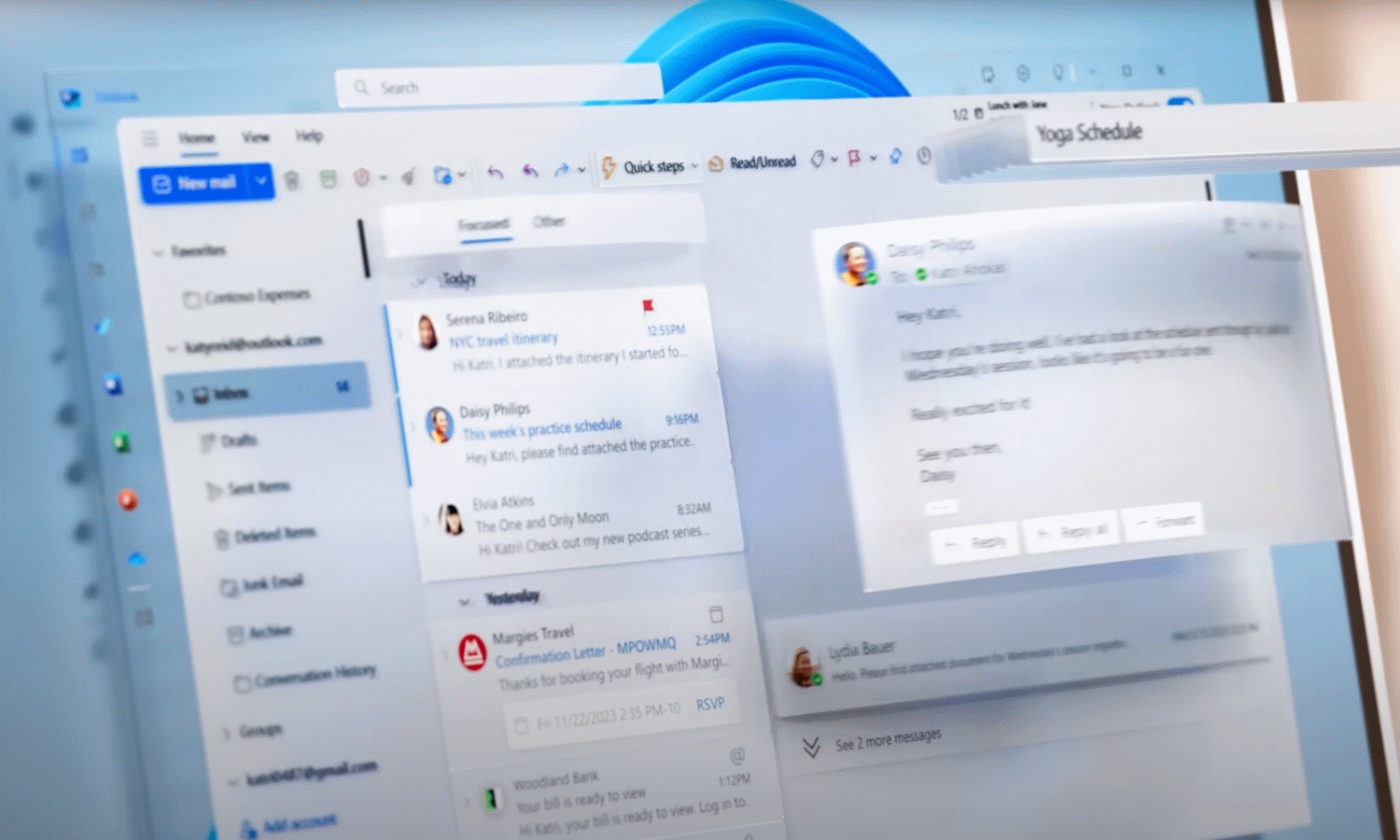
If you sign into your Microsoft account on a public or shared computer, you need to know this
Microsoft has quietly announced a significant change to the sign in/out process for Microsoft accounts. The change could have massive security implications for many people.
As of next month, when you sign into your Microsoft account, you will remain signed in until you opt to sign out manually. At the moment the (arguably more secure) approach sees users signed out automatically after a period of inactivity, helping to protect anyone using a public computer.

7-Zip users need to take action right now to address a serious security flaw
If you are a 7-Zip user, you need to be aware of a serious Mark-of-the-Web bypass vulnerability. The security hole is not new, having been reported way back in October 2024, but details have only just been released about it, and a fix has only just been produced.
Unlike many security fixes, however, 7-Zip users will need to be proactive in securing their software. Here’s what you need to know.
Microsoft’s latest Windows security fixes may not install alongside Citrix software -- but there is a workaround
The recently released security updates for Windows 10 and Windows 11 are proving problematic for some people. Microsoft has acknowledged issues with the KB5049981 and KB5050009 updates on systems with “certain Citrix components installed”.
With Windows 10 breathing its last, users will be keen to grab all available security updates before Microsoft abandons it later in the year, so it is good that while there is not yet a proper fix for the problem, a workaround is available.

Data privacy in 2025: The resurgence of biometric security, a fleeting forecast for federal data privacy regulations, and the return of the wild west of AI
The transition from 2024 to 2025 brings a lot of uncertainty, speculation, and hopefully some optimism for the world of data privacy.
As technology continued to innovate, securing data grew more complex and consumers grew more concerned over how their information was being used. Regulatory changes are coming soon, with several states providing their own data privacy standards in anticipation of a shifting focus within the U.S. federal government, creating an important inflection point to set the tone for the future of data privacy and security.

Microsoft confirms strange ‘some settings are managed by your administrator’ BitLocker error
If you’ve got BitLocker enabled on your computer and you’re seeing unexpected error messages, you can take some comfort in knowing that you are not alone -- and also that Microsoft is aware of the issue.
The problem affects some systems with TPMs (Trusted Platform Module), and it results in a message being displayed that reads: “For your security, some settings are managed by your administrator”.
Microsoft will forcibly install the new Outlook app on Windows 10 in February
While making much of the end of support for Windows 10, practically begging users to move on to Windows 11, Microsoft is sending out some confusing signals. The company has announced that the new Outlook for Windows will be forcibly installed on the aging operating system.
Somewhat unusually, the app will be pushed out as part of February’s security updates. This is likely to lead to mixed reactions; some people will be unhappy at having software installed against their will, while others will be pleased to get something new and more secure.
Apple defends Siri, saying the data it collects is never used for advertising, never sold, and never used for profiling
Having agreed to pay out $95 million to settle a lawsuit alleging Siri recorded private conversations without consent, Apple has doubled down on its assertion that it has done nothing wrong.
In a statement entitled “Our longstanding privacy commitment with Siri”, the company stresses it is committed to protecting user privacy. Referring specifically to Siri as “the most private digital assistant”, Apple insists that it “has never used Siri data to build marketing profiles, never made it available for advertising, and never sold it to anyone for any purpose”.
How to unlock innovation safely in the AI revolution
Organizations are caught up in a whirlwind of AI adoption, whilst struggling to ensure their security standards can match up. And as the rush to integrate AI into business processes continues into 2025, the time to safeguard its deployment is now.
To-date much of the security discussion around AI has focused on protecting against AI-powered threats. However, an overlooked aspect of AI security lies in the internal workings of AI systems, notably the hidden layers in machine learning models. Understanding the evolving threats to these internal structures is crucial to ensuring the safety and integrity of organizations seeking a security foothold in the current storm of AI adoption.

Microsoft warns of Windows 11 24H2 installation issue that blocks all future security updates
Microsoft is vocal about the importance of ensuring that Windows users have all of the latest security updates installed, and rightly so. Now the company has warned that using certain installation media to install Windows 11 24H2 could result in not being able to receive any further security updates.
The root cause of the problem has not been revealed as Microsoft is still investigating, but the issue can occur when using media such as CDs or USB drives to install the latest version of Windows 11. While the cause is not known, and there is no specific fix, there is a workaround.

Savvy security needs SASE: Addressing the security challenges organizations are grappling with
With the threat landscape becoming increasingly sophisticated, companies need agile approaches to improve their defenses and mitigate risks. After all, hackers are adapting their strategies and introducing new tools and technologies to improve their success rates. The resulting rise in cyber-attacks is evident in Xalient’s latest research report ‘Why SASE is the Blueprint for Future-proofing Your Network in 2025 and Beyond’, where a staggering 99 percent of respondents say they have experienced an attack in the last 12 months.
It is no surprise that cyber security is gaining attention from across the C-suite, with 58 percent of CEOs considering cyber-attacks a very big threat to business operations, as PwC's 25th CEO Survey finds. With security moving further up the boardroom agenda, security teams are under greater scrutiny as they work to safeguard the company, its data and its employees. But what are the biggest security challenges and how can security teams improve the security posture of their organisations?

Report: Apple is working on a Face ID powered smart doorbell and lock
Apple looks ready to continue its foray into the smart home market with a new doorbell to rival Amazon’s Ring. Driven by Face ID, Apple’s upcoming device is set to be more than just a doorbell -- facial recognition will be used to unlock the door as well.
But if you are looking for a smart doorbell right now, Apple may not be the choice for you. The company’s work is said to be in the preliminary stages, with products unlikely to emerge until at least the tail end of 2025, but likely some time in 2026.

What will attackers target in 2025? CNI, CNI, and more CNI!
Critical national infrastructure (CNI) has had a rough 2024 in the UK when it comes to cybercrime. From the chaos caused by a teenager who hacked into TfL to the dangerous impact on the NHS after the Synnovis breach. And let us not forget the ongoing fallout from the Sellafield breach in December 2023.
These are just a few of the notable cases of a much wider problem, with Bridewell finding that 60 percent of UK CNI organizations experiencing at least one ransomware attack over the past 12 months.

Experts call for proactivity to combat state-sponsored cyber threats in 2025
In 2024, opposing nation-states have utilized cyberattacks to project power and disruption from within their own borders. This shift has been epitomized by the rise of the “Axis of Upheaval,” dominated by the CRINKs nations -- China, Russia, Iran, North Korea -- who share a common reliance on using cyberattacks to wreak havoc in an affordable manner.
Whether it’s North Korea using ransomware to generate revenue for its isolated regime, or Russia focusing on disrupting and eroding public trust in democratic institutions, each state is finding its niche to cause harm. Despite these varied goals and techniques, it’s the same sectors again and again in the crosshairs. Whether it’s CNI, healthcare, or finance, these organizations now must protect against a wide range of attack styles and techniques.
