How do survey scammers 'clipjack' Facebook users?
This analysis is excerpted from AVG Technologies' Q3 "Community Powered Threat Report", which released Oct. 11, 2011.
Facebook is the second most popular site in the world according to Alexa's traffic rankings. The social network had explosive growth from 2008 with 100 million users to 750 million users today. This equates to about 11 percent of the world’s population or 36 percent of global Internet users; Facebook became the largest social network worldwide. The social network's popularity and its fast growth make it a prime target for cybercriminals.
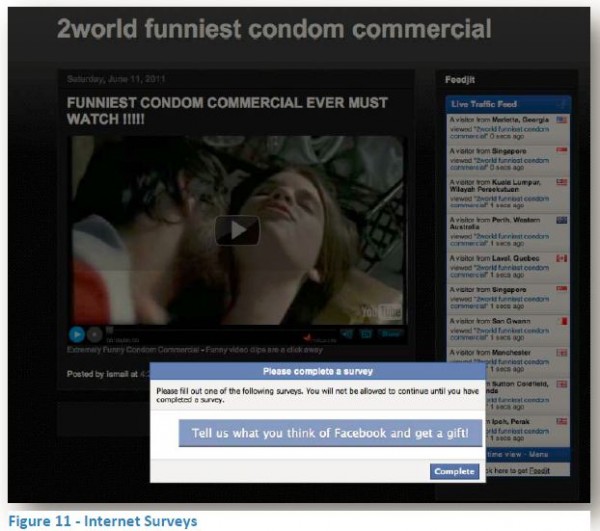
Here, we examine the anatomy of the Clipjacking and Survey Scam. Clipjacking (similar to ClickJacking or LikeJacking) is a method where scammers try to trick Facebook users into clicking on a play button of a video clip. In this specific case it is claimed to be the world's funniest condom commercial. Similar to the earlier LikeJacking scams, the users do not realize that by trying to play the video clip, they are unwittingly saying that they "Like" the video clip, and not just that, they even "share" it with their Facebook friends.
However, the ultimate aim of this attack is to get the victim to agree to an automatic $10 monthly mobile phone charge. Even if victims evade the monthly mobile phone charges, they are likely to be embarrassed at a minimum, as most of the lures involve subjects of an adult or morbid nature. Co-workers, bosses, parents, children and spouses are usually part of each victim's social network.
This attacking method takes advantage of the viral nature of Facebook; every time someone tries to watch the video clip, it is written on his or her Wall and is shared among friends and friend’s friends (via the News Feed) and spreads all over the Facebook nation.
The attack involves placing a transparent image file (GIF) over a video clip; this GIF file and hidden code behind it can go unnoticed by the majority of Facebook users. The user is tricked into believing that he or she is pressing the "play" button when actually clicking on the transparent GIF that executes the code.
It is important to note that even though this is not a computer virus or worm per se, since it relies on the viral nature of Facebook itself to spread, it is viewed by most of the victims like they’ve been hit by a virus.
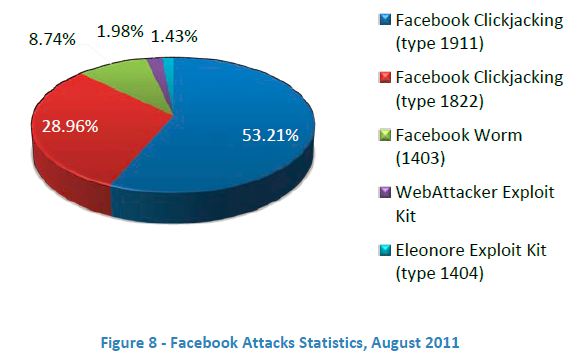
Clickjacking is one of the most common attacks executed against Facebook users. In August 2011 alone, we have witnessed that more than 80 percent of the attacks on Facebook were Clickjacking related.
Anatomy of an Attack
Let’s dive deeper to see a live example of how this attack works:
1. A Facebook user sees on his or her news feed, a viral link recommended by a friend in the network
2. When clicking on the viral link, the following page is presented; all the user needs to do is click on the play button, right? Wrong.

3. As we are often told, read the fine print! Most Facebook users will not be able to see the hidden code underneath the photo (marked with a red border) or wouldn’t understand the implication if they did.
4. In the following screenshot, part of the code is highlighted.

5. Anyone clicking the play button would have this same code executed on the Facebook account; on top of the hidden "Like" process, the user is askedd to fill out an endless list of surveys, generally to "prove that they are not an Internet bot".
6. After a seemingly endless process of surveys, eventually the user gets to the point where he or she "only" needs to supply a cell phone number. While supplying the cell phone number, the user basically agrees to an automatic $10 monthly mobile phone charge.

Credit Card Data is Passé
The Facebook detections are the ones that show Facebook as either the deliverer or the referrer, and it roughly works out to 30,000 detection reports daily in March 2011. AVG’s ‘population’ is 98 million and the Internet’s population is 2 billion people, so we can assume that the real daily detections are approximately 600,000 (30,000 X 20).
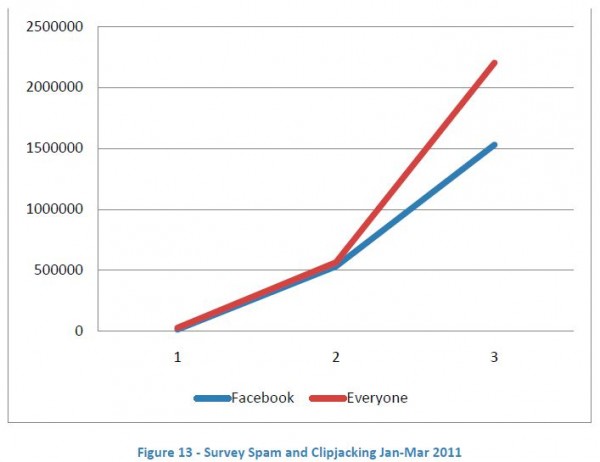
Let’s assume that the success rate (meaning users who did provide their cell phone details to the cyber criminals) is about 1 percent. This translates to 6,000 users who generate $60,000 per day of gross profit, or 1.8M per month. However, we shouldn’t forget this is not a one-time sale. Unless the victim cancels the charge, it will recur each month, easily compounding to over $20,000,000 annually.
Other ClickJacking/LikeJacking scams that we witnessed during the year are:
- "Big baby born – amazing effects"
- "Who is looking at your profile"
- "Girl caught stripping on webcam by her dad"
- "You won’t believe what this teacher did to his student"
- "This guy took a picture of his face every day for eight years"
- "Lily Allen shows her breasts on British television"
The main take away from the story is that stealing credit card data is passé. To steal a victim’s money, all that is needed is his or her mobile phone number. Mobile phone companies make it easy for the scammers since they collect the money for them.
 Yuval Ben-Itzhak is chief technology officer for AVG Technologies. He is responsible for the strategic and technical development of the AVG product line as well as developing key partnerships within the industry and identifying technologies offering potential for acquisition. Ben-Itzhak is a security industry veteran with more than 15 years of global IT security experience.
Yuval Ben-Itzhak is chief technology officer for AVG Technologies. He is responsible for the strategic and technical development of the AVG product line as well as developing key partnerships within the industry and identifying technologies offering potential for acquisition. Ben-Itzhak is a security industry veteran with more than 15 years of global IT security experience.