Why Apple's shameless fight with the FBI is all about ego, not just cause

After spending the last few days soaking up as much as possible on the Apple-FBI San Bernardino iPhone spat, the evidence -- in my eyes -- has become crystal clear. Apple's planted itself on the wrong side of history here for numerous reasons, and is using nothing less than a finely scripted legalese tango in defending its ulterior motives.
As a part time, somewhat auxiliary member of the tech media at large, I'm a bit embarrassed at how poorly this story has been covered by my very own colleagues. Many of those who should undeniably have a more nuanced, intricate understanding of the technical tenets being argued here have spent the last week pollinating the internet with talking point, knee-jerk reaction.
Inadvertently, this groupthink is steering Apple's misguided arguments forward to a populace that otherwise relies on the tech media's prowess in unearthing the truth in such matters. This is one such case where technical altruism is blinding the real story at play here, which are Apple's design flaws -- in other words, inadvertent insecurity bugs -- found in the older iPhone 5c.
For those that haven't kept up on this story, you can get a great primer on where the Apple vs FBI situation stems from and its surrounding core facets. ZDNet's Zack Whittaker has a great FAQ post that digs into the major topics at hand in an easy to understand manner. No need to retread already covered ground in this post.
Apple's Framed Narrative in Twisted Prism of Encryption
The tech media is writing story upon story that makes mention of supposed backdoors the FBI is requesting, which entail things like "master keys" which could potentially unlock any encrypted iOS device. While there are far too many media stories I could link to which prove such misinformation dissemination, I'll point to posts like this one on Venturebeat and even coverage on the otherwise usually judicious podcast, This Week in Enterprise Tech (episode 177 is where the Apple/FBI case was dissected at length).
While this self-absolving narrative is making its rounds, let's not forget where this all began. It was Apple itself, in its now famous open letter which was published on Apple's website and signed off by no less than Tim Cook himself. And for that, shame on him.

Many in the media have mistaken this to be a case about phone encryption, due to Apple's framing of the discussion in such a light. In reality, the FBI is merely asking Apple to help create a special iOS firmware for a single iPhone 5c which could disable forced-wiping after 10 entries, and altering the timeout delay between entries. Apple's attempt to sway the narrative leads me to believe it is more concerned about corporate image than public safety. (Image Source: Mercury News)
I know very well that as the leader of a massive publicly traded company, Cook has a duty first and foremost to his most critical stakeholders, those being Apple shareholders. But the finer point which Apple forgets in its shameless fight with the FBI is that the very sacred tenets of American democracy and capitalism have allowed his firm to grow to such unprecedented levels. There is very well a balancing act which needs to be distinguished in a free society that stands at the folds between security and privacy.
The FBI is not asking for any kind of encryption "master key" here, let's be very clear. Such a request would be an overreach of the inherent division that is required to ensure the greater security of data for the masses in question here. And such a request would be one that I would, as an IT professional, yet more importantly, a member of this society, be very succinctly be opposed to.
But this is not what has been asked of Apple, and not what's at stake for the company. This move is driven by a PR objective aimed at keeping Apple's ego and image in something it preaches so dearly: security.
FBI's Request Indirectly Forces Apple to Admit iPhone 5c Insecurity
If you're curious as to how I could come to such a conclusion, you can feel free to glean through the same well written, and lengthy, expose on this situation which convinced me on the subject with clear technical validation and reasoning -- not purely emotional knee-jerk reaction. The post is on the blog for a company called Trail of Bits which has noted deep expertise in security research.
Much of my very stance on the subject is also reflected in Mark Wilson's post from a few days ago right here on BetaNews. Even Trevor Pott of The Register penned a rather wordy, but pointedly accurate piece that confirms what the Trail of Bits blog post puts forth as a theory.
"What appears to be involved is a design flaw. Something about the iPhone 5C in question is broken," says Pott in his Register article. That's right, a design flaw which happens to be the complete lacking of the "secure enclave" which is detailed at length in the Trail of Bits blog piece.
If this were a newer A7 or newer powered iPhone, the FBI's chances of getting in without asking for the dreaded pandora's box "master key" (which doesn't exist) would be next to zero. But Apple never included this security facet on its earlier phones, and herein lies the very nuanced tenet of what the FBI truly wants to be able to leverage.
The FBI doesn't want and has never asked Apple for any kind of master key. It's asking for mere assistance in re-engineering its way through a known security flaw in Apple's iPhone 5c device which doesn't tie PIN entry and authentication to the internal data through the use of this secure enclave. While Apple won't admit as much, this is very much so a security flaw that Apple obviously will never be able to fix for iPhone 5c owners, and naturally, has every intention to re-architect the argument on this situation to deflect any potential for this criticism to reach critical mass.
And even more acutely, the FBI and Justice Department aren't asking Apple to make this available to "all" future iPhone 5c devices recovered in the course of policing. The DOJ says Apple has the free will to "keep or destroy" this special firmware after its purpose is rendered for the FBI's requests. So Apple's consumer-focused defense that it is being asked to "hack its own users" is just another attempt to misconstrue the real intentions of law enforcement here.
One important fact which some of the media has glossed over is that the iPhone in question was not even a personal phone of the shooter. The device was actually a work-issued device that was handed out by the San Bernardino County Department of Public Health, and in turn, is considered employer property with all accompanying rights that employers have over the data stored on those devices.
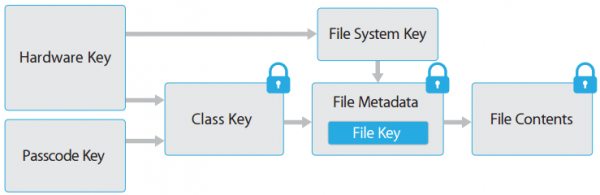
Apple's A7-powered and newer iOS devices all employ an internal lockbox known as the "Secure Encalve" which broker access to encryption keys used to access user data. The iPhone 5c lacks this very item, which makes the FBI's chances at getting into the San Bernardino shooter's iPhone very possible -- and technically proven feasible by security experts. But Apple's ego, partially built on an image of security, naturally forces its arm in trying to trump the FBI's request. (Image Source: Troy Hunt)
I'm not here to use Apple as a pincushion, as the industry at large needs to double down in its attempts to put its actions where its words are about security. But Apple deserves heat here, not only because it's putting shareholders first above national security, but because it has previously been guilty of trumpeting "security through obscurity" as I've covered at length in previous posts.
Any reasonable technology company is going to have bugs and defects in its devices and code. That's the nature of the beast, and understood by IT pros like myself. But Apple has built an empire in part by its clever marketing teams that have flaunted layers of security which supposedly beat and exceed those of any other company's competing products.
Sometimes, it is in the right and marketing matches reality.
But many times, like with the now-dead claims that OS X doesn't get malware which I fought against for years, Apple put greenbacks before fiduciary responsibility to be honest about its software and device capabilities. And while the cessation of the famous "I'm a MAC" advertising campaigns signaled a more subdued competitive standing on the OS X front, Apple's big moneymaker isn't in desktop computers anymore, it's in iPhones that it sells by the millions.
How does this round back to its reluctance to work with the FBI? Very simply, doing so would inadvertently admit that the iPhone 5c indeed has the security flaw which the FBI and the industry has exposed. And the problem for Apple is that it has created an ego bubble for itself which fans have bought into that has security as a notable keystone.
If that keystone falls here, Apple's back to square one with winning back its fans that place i-Devices on a pedestal most other manufacturers only wished they had.
Put in other words, it's Apple's ego at stake here. And it takes that very, very seriously if you haven't noticed.
Apple Has an Undeniable Duty to the Society it Built its Fortunes On
We've clearly established some very agreeable, black and white, facts surrounding this situation based on everything I've linked to above:
- This is not a debate or court-order surrounding any kind of encryption "backdoor" or "master key."
- The FBI is asking for acute access into a single iPhone based on a design flaw which has been exposed.
- Apple has the proven technical ability to render this special firmware locked to the iPhone in question.
- Apple has the court-ordered right to perform the procedures needed in its own facilities, and destroy the software created once complete.
As such, I'm convinced beyond any doubt that the abilities to get into this phone exist, and can be done so in a way to protect the universe of iPhone users at large from massive data grabs by legal overreach. Apple's denial in helping the FBI, as described earlier, is not grounded in technical validity, but rather being driven by a corporate ego that has grown too large for its own good.
Apple's feelgood and impenetrable stances on its device security are at risk of being exposed to the masses. For a company that has built its fortune around peddling a larger-than-life notion about its own security prowess, this would spell downright disaster in the marketplace, especially in the newfound re-emergence it has found in the previously reluctant Enterprise market towards its products.
VOTE NOW: Poll: Should Apple help the FBI unlock the San Bernardino iPhone?
But let's go beyond profitability reports and corporate egos, as the larger extrapolation here is Apple's duty that it owes to the citizens of this very nation. A country that is now in need of a compassionate about face by Apple so we can connect the dots on a terrorist situation that will not only help explain the events leading up to the San Bernardino massacre, but likely expose critical nuggets of information about other future plots or combatants.
Apple's attempt to paint this discussion in a sea of technicalities and promotion of the privacy of its users at large ends up falling on its face when the facts are dissected in sunlight. If that very sunlight means Apple's design flaws must be vaulted into public discussion, so be it. That's the duty it owes its users in being assured that its designs are not merely existing in a lab -- but being tested, sifted, and penetrated to make future generations of hardware better on the whole.
While our democracy has been historically opposed to gross intrusion of privacy, as seen in opposition to ad-hoc phone record dredging, a common sense approach towards nuanced security needs is something we cannot become blind to. Companies and advocates like Apple will try to smokescreen their intentions with public decrees like Tim Cook's in a blanket position on privacy, but even its future has just as much at stake if the terrorists can use an over-extended privacy veil as its own.
The day the Justice Department calls for blanketed encryption"master keys" from Apple is the day I will stand with Apple. But that day is not today, as Apple has not and is not being asked as much.
Do the right thing, Tim Cook. Your company enjoys prosperity through the same democratic society that is pleading with you to put the future of our nation ahead of personal or corporate motives.
If future deaths could have been prevented acutely via that iPhone 5c you refuse to help unlock, what kind of responsibility will fall on Apple's shoulders? Only history will be the judge of that.
Image Credit: klublu/Shutterstock
 Derrick Wlodarz is an IT Specialist who owns Park Ridge, IL (USA) based technology consulting & service company FireLogic, with over eight+ years of IT experience in the private and public sectors. He holds numerous technical credentials from Microsoft, Google, and CompTIA and specializes in consulting customers on growing hot technologies such as Office 365, Google Apps, cloud-hosted VoIP, among others. Derrick is an active member of CompTIA's Subject Matter Expert Technical Advisory Council that shapes the future of CompTIA exams across the world. You can reach him at derrick at wlodarz dot net.
Derrick Wlodarz is an IT Specialist who owns Park Ridge, IL (USA) based technology consulting & service company FireLogic, with over eight+ years of IT experience in the private and public sectors. He holds numerous technical credentials from Microsoft, Google, and CompTIA and specializes in consulting customers on growing hot technologies such as Office 365, Google Apps, cloud-hosted VoIP, among others. Derrick is an active member of CompTIA's Subject Matter Expert Technical Advisory Council that shapes the future of CompTIA exams across the world. You can reach him at derrick at wlodarz dot net.