Exploring the psychology of ransomware
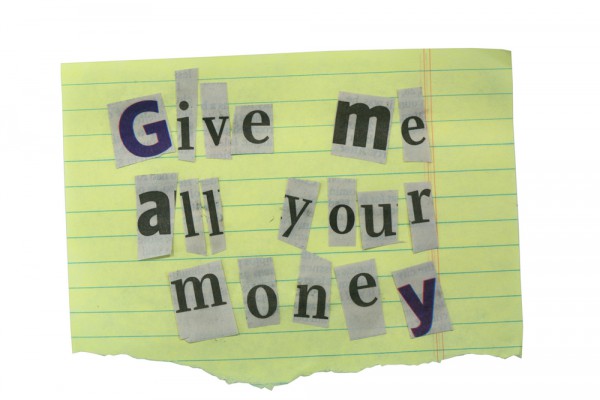
In recent months we've seen high profile ransomware attacks target many businesses, and we've seen cyber criminals making greater efforts to target their victims.
A new study from endpoint protection company SentinelOne and De Montfort University has been looking at how social engineering tactics are used by cyber criminals to manipulate and elicit payments from victims.
"We noticed that there's a wide range of techniques used in the splash screens that we see and we thought it would be interesting to understand the things that went into them, the icons and so on," says Tony Rowan chief security consultant of SentinelOne. "Rather than just guessing we thought that the thing to do was to get someone who knows what they're doing on the psychology front, so we turned to the De Montfort team."
The study looks at the 'splash screens' displayed when a machine is locked by ransomware, and finds varying levels of sophistication among attacks, but it does identify some common trends. These include making payments time critical, stressing consequences such as deleting files, taking a customer service approach, and using official looking imagery.
"There are structural similarities in the patterns of what attackers are using to elicit payment," says Dr Lee Hadlington PhD, senior lecturer in cyberpsychology at De Montfort University. "These are fairly standard but there are tweaks and individual elements that stand out as unusual and different. Whether consciously or not they are using aspects of social engineering by using things such as scarcity, aspects of influence and authority."
In over half the samples (57 percent), a 'ticking clock' device -- in which a specific amount of time is given to pay a ransom -- was used to create a sense of urgency and to persuade the victim to pay quickly. Deadlines given ranged from 10 hours to more than 96 hours.
The most likely consequence given for not paying the demand or missing the deadline was that files would be deleted and the victim wouldn't be able to access them. In other screens, threats were made to publish the locked files online.
51 percent of splash screens included some aspect of customer service, such as instructions on how to buy Bitcoins or presenting frequently asked questions. One example offers victims the chance to 'speak to a member of the team'. "There are attempts to emulate what works in business with things like FAQs, 'contact the team' or 'refer to this website'," adds Dr Hadlington. "We saw one example that listed links to FBI stories -- which may have been spoofed -- advising people to pay the ransom to get their files back."
The research also looks the use of a variety of imagery, including official trademarks or emblems, such as the crest of the FBI, which instil the notion of authority and credibility to the request. One of the most prominent pop cultural images used is 'Jigsaw' -- a character from the Saw horror movie series. "Imagery is being used in two ways," says Dr Hadlington. "The first is the menacing aspect like the Jigsaw character and the V for Vendetta mask. The other imagery we see is the official badges, the FBI and government shields, in order to give an air of authority. There are also the badge and lock type icons that you see on things like antivirus software and cyber security products."
Bitcoin is the preferred mechanism for payment, 75 percent of ransomware splash screens asked for payment in BTC. Over half the sample (55 percent) contained the ransom demand in the initial splash screen. The average amount asked for by attackers was 0.47 BTC ($1,164 USD). "The more organized attackers seem to have more reasonable pricing," says Dr Hadlington. "They tend to go for lower amounts as they're trying to get a wider spread of people to pay up. The more disorganized and badly presented ones just say, 'we want 300 Bitcoins'. A lot of these splash screens will actually give you information on how to buy Bitcoins, we've even seen one with a video tutorial."
You can find out more in the full report which is available from the SentinelOne website.
Image Credit: Robynrg/Shutterstock