'Hunter-killer' malware able to neutralize advanced defenses
A new report from Picus Security looks at real-world malware samples and identifies the most common techniques leveraged by attackers.
It identifies a surge in 'hunter-killer' demonstrating a shift in adversaries' ability to identify and neutralize advanced enterprise defenses such as next-gen firewalls, antivirus, and EDR. According to the report, there has been a 333 percent increase in malware that can actively target defensive systems in an attempt to disable them.
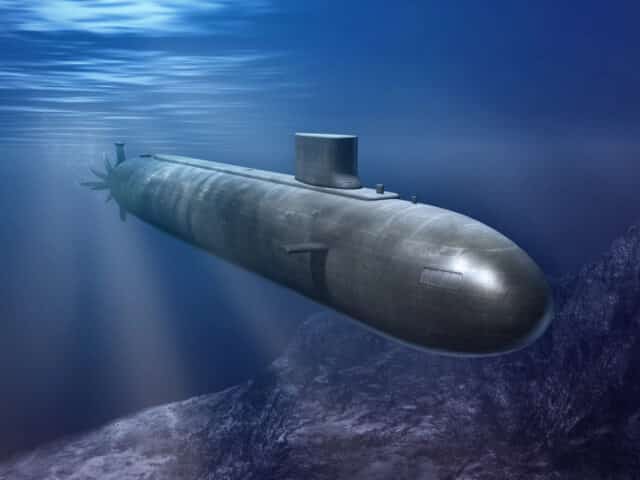
"We are witnessing a surge in ultra-evasive, highly aggressive malware which shares the characteristics of hunter-killer submarines," says Dr Suleyman Ozarslan, Picus Security co-founder and VP of Picus Labs. "Just as these subs move silently through deep waters and launch devastating attacks to defeat their targets' defenses, new malware is designed to not only evade security tools but actively bring them down. We believe cybercriminals are changing tack in response to the security of average businesses being much-improved, and widely used tools offering far more advanced capabilities to detect threats. A year ago, it was relatively rare for adversaries to disable security controls. Now, this behavior is seen in a quarter of malware samples and is used by virtually every ransomware group, APT, and nation-state."
Among other findings of the report, 70 percent of malware samples analyzed now employ stealth-oriented techniques by attackers, particularly those that facilitate evading security measures and maintaining persistence in networks.
There has been a 150 percent increase in the use of T1027 Obfuscated Files or Information. This highlights a trend toward hindering the effectiveness of security solutions and obfuscating malicious activities to complicate the detection of attacks, forensic analysis, and incident response efforts.
The report also notes a 176 percent increase in the use of T1071 Application Layer Protocol, which are being strategically deployed for data exfiltration as part of double extortion schemes.
The full report is available from the Picus site.
Image credit: Andreus/depositphotos.com
