
Why PKI still has a key role in security [Q&A]
The origins of Public Key Infrastructure (PKI) date back to the 1970s and research at UK intelligence agency GCHQ, though it didn't emerge from the secret world and take off commercially until the 1990s.
PKI still underlies a great deal of modern cryptography, so we spoke to Ryan Sanders, senior product marketing manager at Keyfactor, to find out more about it and why it isn’t going away any time soon.

Phishing and stealers dominate dark web forums (but don't mention ransomware)
The malware types and hacking services most discussed over the last year on dark web forums are dominated by phishing, stealers, zero-day attacks, and ransomware.
But the 2021 Year-End Data Breach Report from Risk Based Security finds discussing ransomware has been widely banned on major forums as evidenced by referring to ransomware offerings as 'crypters' or 'lockers' to avoid the post or account getting immediately banned.

Cybersecurity and the art of persuasion [Q&A]
Despite the introduction of systems based on AI and other technologies, cybersecurity remains an ultimately human problem.
It's not just a problem for IT teams either, to keep the enterprise safe security needs to be taken seriously throughout the organisation. It's the role of the CISO to ensure this but it can be a challenge to implement.

Ransomware attack puts the squeeze on KP's nuts
A cyberattack on UK-based food manufacturer KP Snacks could lead to shortages of some of the company's popular products including KP Nuts, Tyrrells Crisps and Hula Hoops.
There are as yet unconfirmed reports that the company's factory at Billingham on Teesside has stopped production and most of its 900 staff have been temporarily stood down.
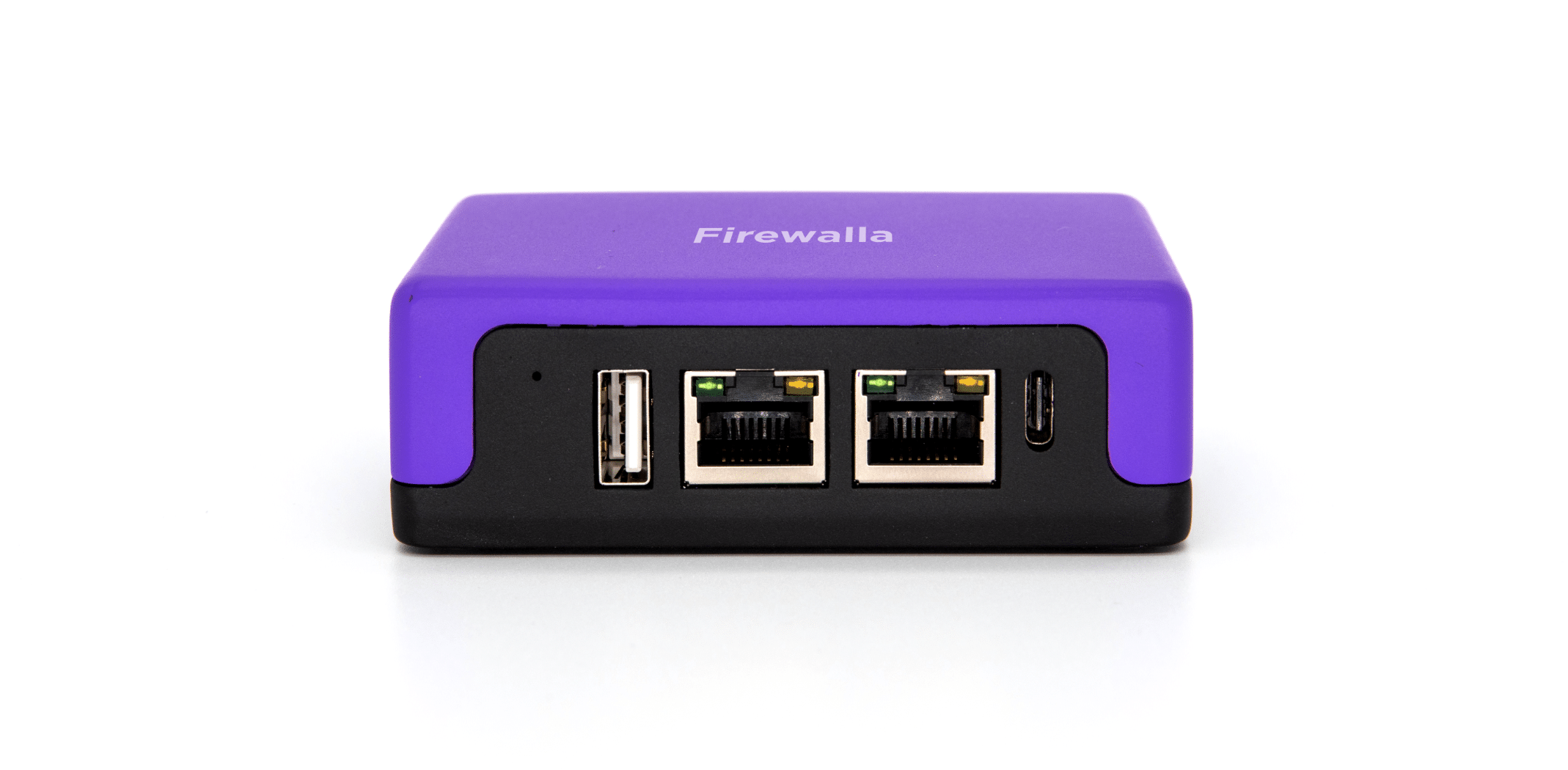
Firewalla Purple brings new levels of protection
Back in July 2021 we reported on the announcement of the Firewalla Purple network protection appliance. It was due for release in December so has been subject to some delays, but from today it's finally available to buy.
Like other Firewalla offerings it's a compact portable device that you can take anywhere to deliver enterprise-grade protection, guarding against cyberattacks and offering advanced insights into your network.

Over half of time spent on security issues is wasted
It was department store tycoon John Wanamaker who came up with the famous line, "Half the money I spend on advertising is wasted; the trouble is I don't know which half." A new report from Lacework suggests that IT teams may feel the same way about time spent on security.
A study 700 executives and practitioners, carried out by ClearPath Research to learn more about cloud adoption and the changing security landscape, finds that 55 percent of security and compliance teams globally believe at least half their time spent on security issues is 'not meaningful'

Two-thirds of organizations plan to increase zero trust budgets in 2022
More than more than 75 percent of IT leaders surveyed for a new report cite the importance of zero trust in combating mounting security threats and two-thirds plan to increase their budgets for the technology.
The study, conducted by Forrester Consulting for Illumio, finds teams are still fighting to catch up with critical initiatives with over 60 percent of respondents saying they were unprepared for the rapid pace of cloud transformation and migration.

40 percent of employees take data with them when leaving a job
New research from email security company Tessian finds that 40 percent of US employees have taken data with them when they've left a job.
This potentially exposes the business to a raft of cybersecurity concerns, from data breaches to regulatory fines. When asked why are they taking data 53 percent of employees say they worked on the document so therefore believe that it belongs to them.

Training becomes a priority to bridge skills shortages
Skills shortages in the IT industry are nothing new, but the pandemic has added to the problem to the point where 76 percent of IT decision makers now say they face critical gaps in their departments.
New research released today by digital learning company Skillsoft shows gaps in technical knowledge and skills over the past year and a half have had a major impact on decision makers, 89 percent report a loss in revenue, 76 percent a loss of business to competitors, and 72 percent declining customer satisfaction as a result.

Meta will warn you if someone screengrabs your encrypted Messenger chats
Meta is adding a new warning to encrypted chats in Messenger so that users will know if another participant has taken a screenshot of the conversation.
The company formerly known as Facebook has already implemented this same feature into messages sent when the app's Vanish Mode is activated. While Messenger has not been updated to prevent screenshots from being taken in in E2E encrypted chats or Vanish Mode conversations, the appearance of the warning should serve as a deterrent against secret screen grabbing.

Designing security to mitigate growing ransomware threats
Ransomware has become a top-of-mind security concern for many organizations. High-visibility ransomware attacks have disrupted supply chains and inspired an Executive Order on Cybersecurity in the United States.
This is not surprising given that ransomware is a such a common and costly threat costing organizations millions.

Data Privacy Day aims to raise awareness of how we collect and use data
Today is Data Privacy Day -- or Data Protection Day, depending on who you talk to -- a day dedicated to an international effort to raise awareness about how data is collected, used and stored.
So, what do the luminaries of the IT world have to say about the day and about data privacy/protection in general? We've rounded up some of their thoughts.

How retailers can beat the top four online shopping security threats in 2022
There’s an inevitable spike in online security threats accompanying the surge in online shopping over the past couple of years, mainly driven by the recent pandemic. As more and more retailers embrace and adopt e-commerce sites to expand their customer base, increased cybersecurity levels are a must to ensure a safe and positive customer experience.
As a business owner, the greatest threat that cyberattacks represent is loss of sales and unhappy customers, which can really make or break a business as a whole. Since many cyberattacks are executed in hidden and unsuspecting ways, identifying and battling them can become a challenge. Let’s take a look at the top four online shopping security threats and how to avoid them in 2022.

The top attack trends businesses need to address this year
2021 saw supply chain and ransomware attacks dominate the security landscape. But will this pattern continue this year?
Managed detection and response provider Expel has launched a new report which provides insights on the biggest cybersecurity threats, practical recommendations on how to handle them, and predictions on what to expect in the year ahead.

Three in four mobile apps contain at least one vulnerability
As the internet is increasingly accessed from mobile devices, mobile apps need to be considered as part of a company's security strategy.
A new report from BitSight finds that three out of four mobile applications evaluated contained at least one moderate vulnerability. It also finds material and severe vulnerabilities in some popular apps.
