Traditional malware falls as mobile malware rises in July
The number of active malware families attacking businesses fell by five percent in July, but mobile malware now accounts for nine percent of the total -- up 50 percent from June.
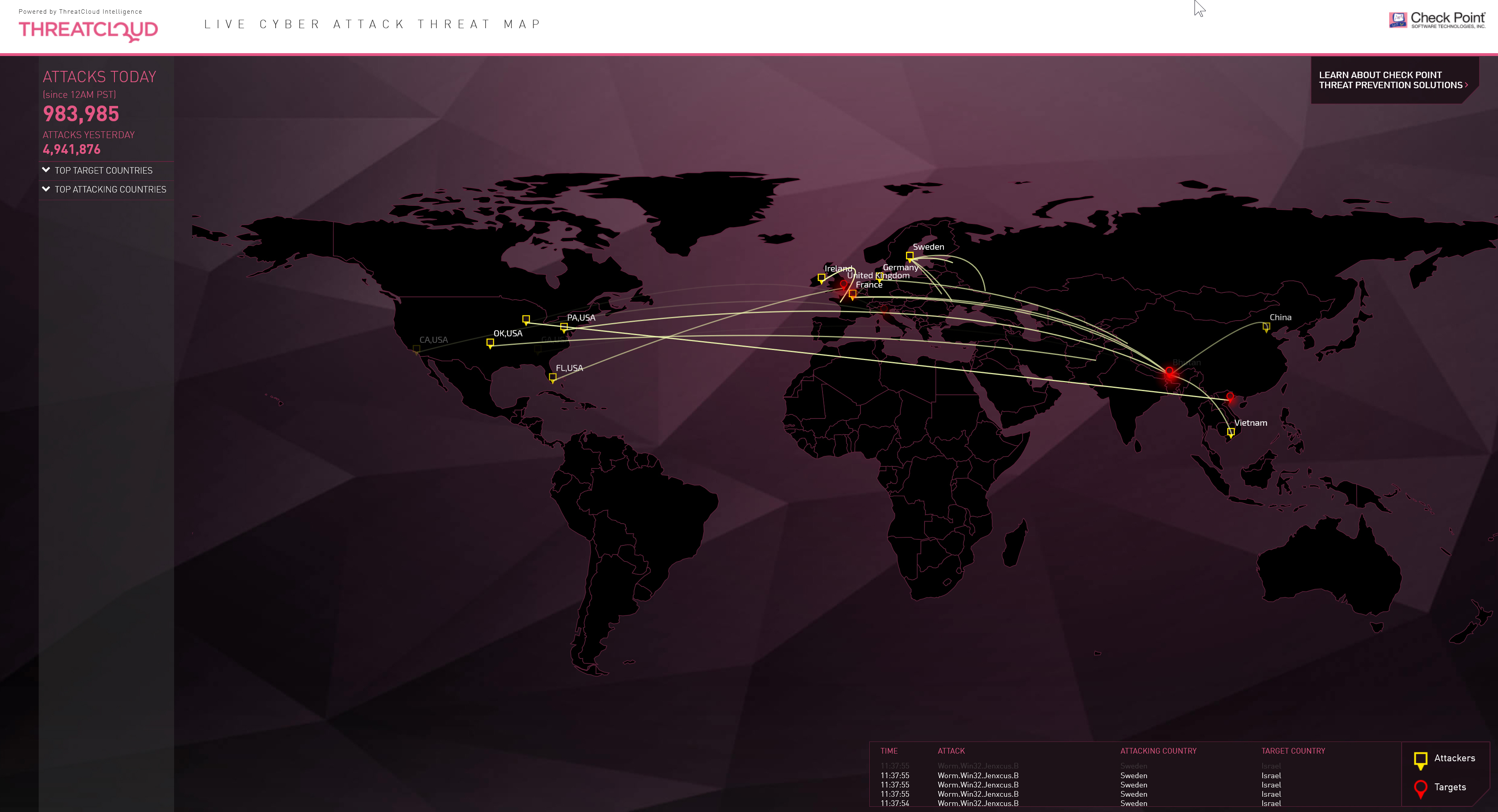
These figures come from threat prevention company Check Point based on intelligence drawn from its ThreatCloud World Cyber Threat Map.
During July, Check Point detected 2,300 unique and active malware families attacking business networks, the first time in four months it has seen a drop in the number of unique malware families. However, the total number seen still matches the second all-time highest number recorded in a calendar month this year.
Conficker was the most prominent family in July accounting for 13 percent of recognized attacks. In second place JBossjmx accounted for 12 percent, and third placed Sality was responsible for eight percent. The top ten families accounted for 60 percent of all recognized attacks.
Mobile malware families had eighteen entries in the top 200 overall. The top three mobile families being HummingBad, Android malware that establishes a persistent rootkit on the device; Ztorg, a Trojan that uses root privileges to download and install applications on the mobile phone without the user's knowledge; and XcodeGhost, a compromised version of the iOS developer platform, Xcode, altered to inject malicious code into any app developed and compiled using it.
"Businesses should not be lulled into a false sense of security by the slight drop in the number of active malware families during July. The number of active families still remains at near record levels, highlighting the scale of the challenges businesses face in securing their network against cyber-criminals. Organizations must continue to secure their networks vigilantly," says Nathan Shuchami, head of threat prevention at Check Point. "Organizations need advanced threat prevention measures on networks, endpoints, and mobile devices to stop malware at the pre-infection stage, such as Check Point's SandBlast and Mobile Threat Prevention solutions, to ensure they are adequately secured against the latest threats".
You can view the live ThreatCloud map displaying cyber attacks in real time on the Check Point website.