Facebook shares more details about its massive security breach -- after blocking people from sharing news about it
The Guardian was among many outlets to write about the huge Facebook vulnerability and attack reported yesterday, and people were understandably keen to share the story on the social network. However, many people found that they were unable to do.
Large numbers of Facebook users who tried to share the Guardian's story -- as well as one published by the Associated Press -- were greeted by a message informing them that the messages was spam and could not be posted. The matter has been addressed, but it led to complaints that Facebook was trying to hush up the story, and renewed calls to #DeleteFacebook. On its blog, Facebook's security team has also given more details about the "security issue" that happened earlier this week,
See also:
- Facebook hack: 50 million users affected by site code flaw
- Instagram co-founders resign from Facebook-owned company to 'explore curiosity and creativity again'
- YouTube alternative Facebook Watch rolls out globally
- Facebook VPN Onavo Protect disappears from App Store for violating Apple's data collection and privacy rules
The problem with sharing the story appears to be related to a problem with Facebook's algorithms. The fact that large numbers of people were trying to share the same story meant that it was flagged by Facebook's systems as spam.
Some of those who encountered the issue took to Twitter to share their experience:
Facebook is preventing users from posting The Guardian's report on the Facebook data breach. Ouch. https://t.co/IGU685PjdK pic.twitter.com/GGGrKqBZEc
— Jed Bracy (@JedBracy) September 28, 2018
On Twitter, having been alerted to the issue, Facebook later indicated that the problem had been resolved:
Following up - people should be able to share both articles now. Sorry for the inconvenience.
— Meta (@Meta) September 28, 2018
Revealing some details of the security issue yesterday, Facebook explained that attackers took advantage of three bugs. Updating the initial post about this, the social network provided more information. Vice president of engineering, security and privacy, Pedro Canahuati, revealed the three problems:
First: View As is a privacy feature that lets people see what their own profile looks like to someone else. View As should be a view-only interface. However, for one type of composer (the box that lets you post content to Facebook) -- specifically the version that enables people to wish their friends happy birthday -- View As incorrectly provided the opportunity to post a video.
Second: A new version of our video uploader (the interface that would be presented as a result of the first bug), introduced in July 2017, incorrectly generated an access token that had the permissions of the Facebook mobile app.
Third: When the video uploader appeared as part of View As, it generated the access token not for you as the viewer, but for the user that you were looking up.
Reiterating what had already been shared, he also wrote:
It was the combination of these three bugs that became a vulnerability: when using the View As feature to view your profile as a friend, the code did not remove the composer that lets people wish you happy birthday; the video uploader would generate an access token when it shouldn’t have; and when the access token was generated, it was not for you but the person being looked up. That access token was then available in the HTML of the page, which the attackers were able to extract and exploit to log in as another user.
The attackers were then able to pivot from that access token to other accounts, performing the same actions and obtaining further access tokens.
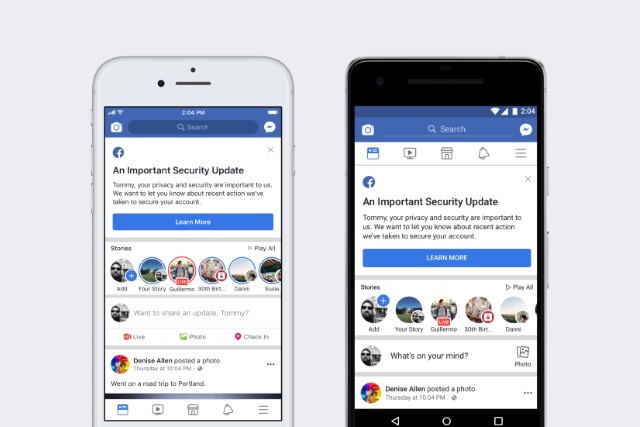
To protect people's accounts, we've fixed the vulnerability. We have also reset the access tokens of the almost 50 million accounts we know were affected and we've also taken the precautionary step of resetting access tokens for another 40 million accounts that have been subject to a View As look-up in the last year. Finally, we've temporarily turned off the View As feature while we conduct a thorough security review.