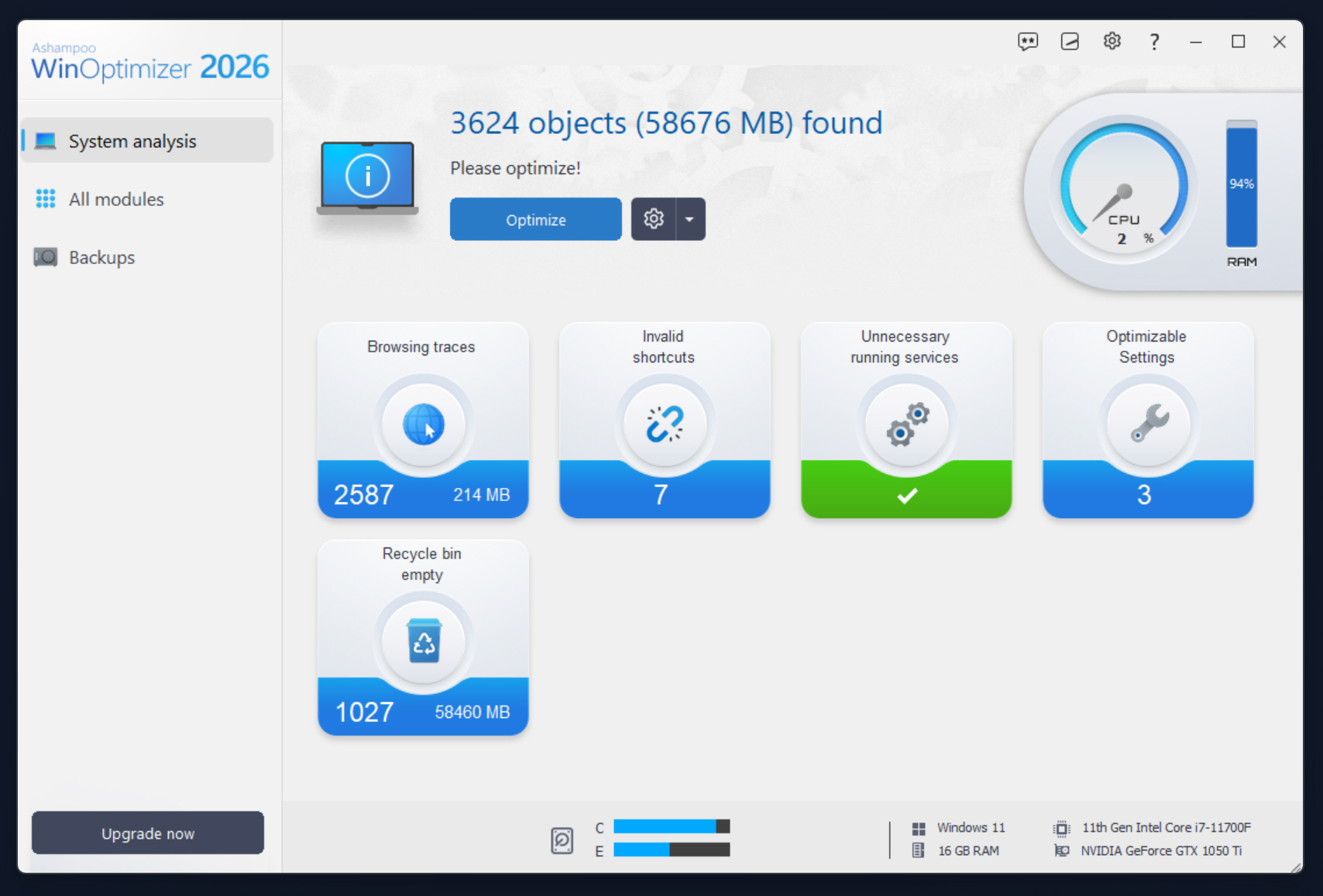
Get WinOptimizer 2026 for free and save $30 on this brand new Windows cleanup and tuning tool
Ashampoo has released WinOptimizer 2026 for managing Windows performance, privacy, and system maintenance. It promises to help boost slow performance, remove leftover junk, and provide easy access to advanced settings.
WinOptimizer 2026 lets users clean, tune, and customize Windows 10/11 without the need for deep technical know-how.
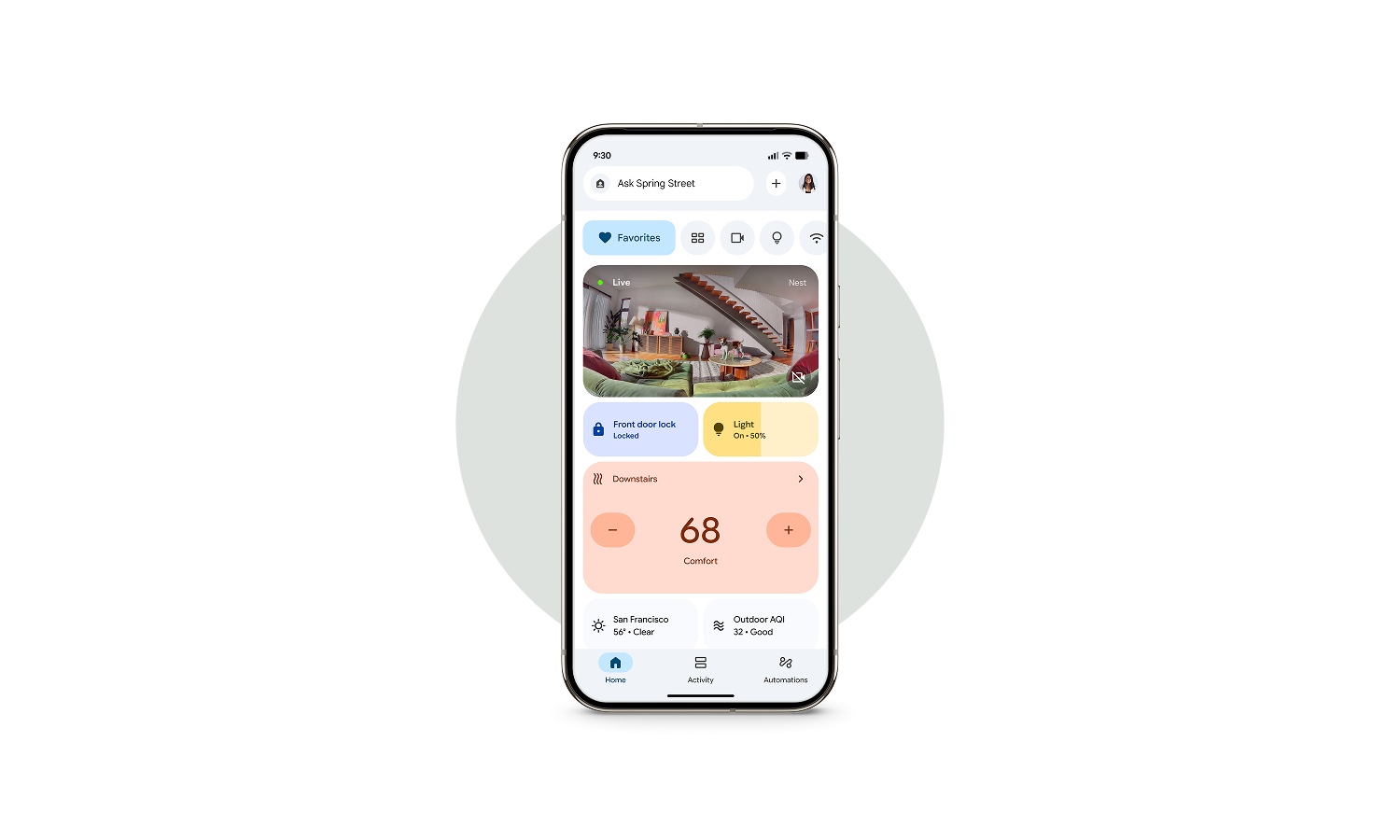
New starters, conditions, and actions are making Google Home more powerful
If you use Google Home to help with automation, there are new options coming your way. Google has announced the addition of new starters, conditions, and actions which it says help to give more granular control.
The various combinations allow for a huge degree of flexibility and personalization. With the Google Home ecosystem continuing to expand to include more products, users are becoming more demanding of what the system can do – and Google seems to be responding.
Google releases the first Pixel update of 2026
Google has started the process of rolling out the first update of 2026 for its range of Pixel devices. There are a large number of bug fixes within this update as well as the usual raft of monthly security patches.
The rollout is taking place on a global scale over the course of the coming weeks. Among the problems this update addresses is an issue that causes battery drain, and another related to flickering AOD.

Microsoft Lens really is closing down in a matter of weeks
Microsoft Lens – once known as Office Lens – has been hanging on by a thread for some time now. The original plan had been to kill off the document scanning app last year, but it was granted a stay of execution.
But now, just as we ease into 2026, Microsoft has announced a revised schedule for the retirement of the app. For fans of Microsoft Lens, there are mere weeks left until it vanishes.

Apple turns to Google Gemini to power the future of Apple Intelligence and finally make Siri good
Apple and Google have entered into a multi-year collaboration that will see the next generation of Apple Foundation Models built on Google Gemini AI models and cloud technology. The agreement brings together two of the largest technology companies at a time when generative AI is becoming a core part of consumer platforms.
Under the partnership, Google’s Gemini models will form the technical foundation for future Apple Foundation Models, which are used to power Apple Intelligence features across Apple devices. One of the first visible results is expected to be a more personalized version of Siri, scheduled to arrive later this year. The updated assistant will be able to handle requests more naturally and better understand user context across apps and services.

VLC adds native Arm support on Windows, improving playback on Snapdragon devices
VLC, one of the most widely used media players, now runs natively on Windows PCs built around Arm processors, removing the need for x86 emulation on Snapdragon powered systems. This will be good news for anyone who has bought one of the growing numbers of Windows laptops and tablets with Arm chips, where emulated apps often feel slower and less efficient.
After years without proper Arm builds on Windows, VLC now offers native Arm64 support, allowing it to run directly on Snapdragon based hardware. This removes reliance on translation layers, which add overhead and, annoyingly, can chew through battery life during media playback.

Someone built a floppy disk TV remote control for kids and it actually works
A Danish hobbyist developer has built a floppy disk based TV remote designed to let young children control what they watch without having to worry about navigating apps or complex menus. The project replaces modern remotes with physical media, giving kids more independence while limiting autoplay and algorithm driven distractions.
The idea grew out of frustration with how current smart TVs behave in a household with children. Menus are layered, remotes are crowded with buttons, and streaming apps constantly push new content.

Why the cybersecurity industry needs more women
Organizations worldwide are facing new digital threats, often rising faster than security teams can address them. This further compounded by a global shortage of cybersecurity skills, with an estimated 4.8 million extra professionals needed.
Yet despite the urgent need for talent, women remain significantly under-represented in the cybersecurity field, making up only 22 percent of the global workforce, according to a survey by ISC².

Microsoft releases 2026’s first Insider build of Windows 11
The first Insider build of Windows 11 for the new year has hit download servers. The KB5072046 update takes the operating system up to build 26220.7535, and it is available to Insiders signed up to the Dev and Beta channels.
As you would probably expect, there are Copilot-related changes and additions to be found in this latest build – including Microsoft deciding to finally gives sysadmins the option to uninstall the Microsoft Copilot App on managed devices.
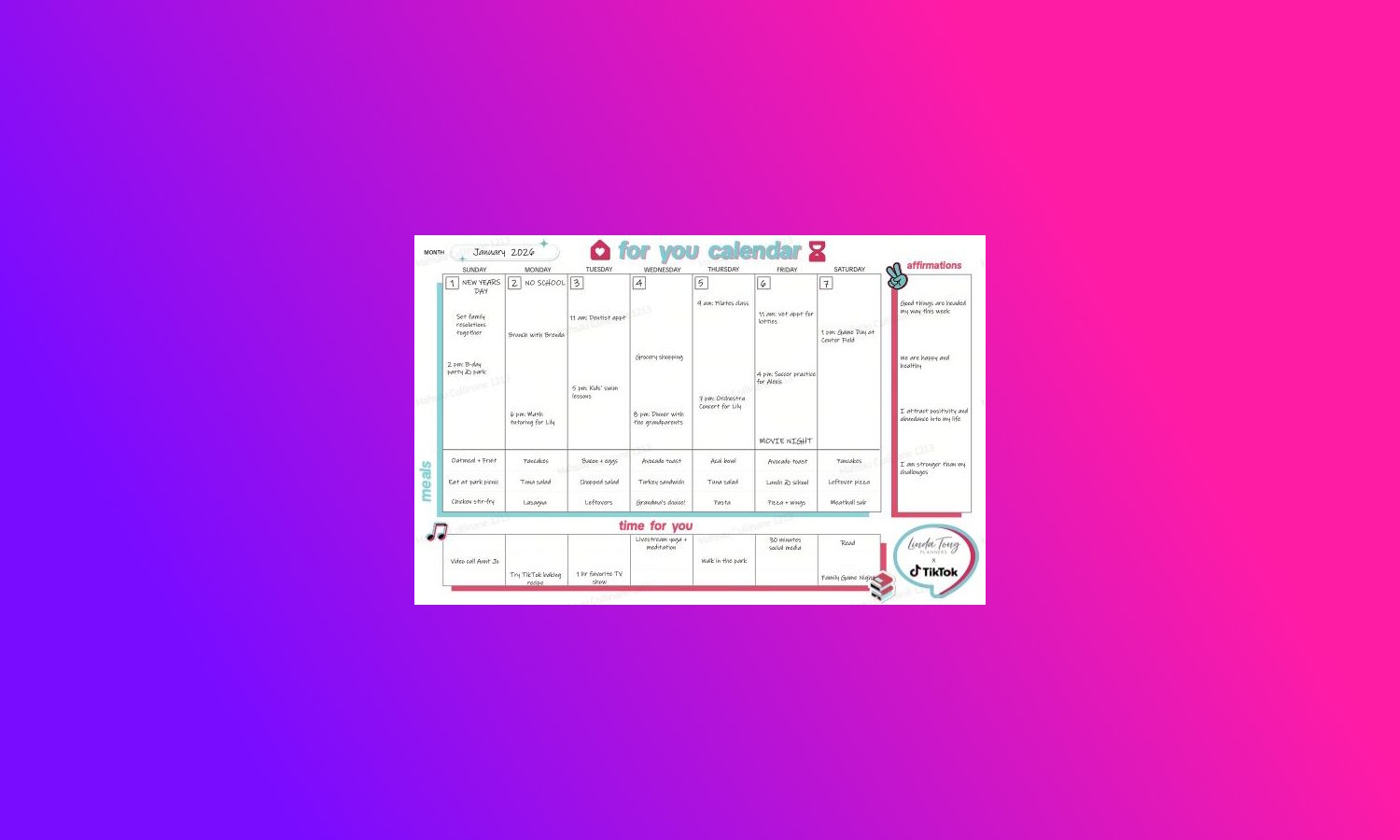
TikTok launches new ‘For You’ Calendar feature
TikTok may not feel like a medium through which to organize anything, but the social media platform is trying to change that. Teaming up with Linda Tong Planner, there is now a new feature called the “For You” Calendar.
Announcing the somewhat unusual addition, TikTok says that the idea is to “help families connect and build positive digital habits”. The start of 2026 is being used as a reason for trying to help people get organized.

Microsoft is killing off Word’s ‘Send to Kindle’ feature
If you are a fan of sending documents from Microsoft Word to your Kindle device, there is some bad news. Microsoft has announced plans to retire the Send documents to Kindle option in Word some time after next month.
As is so often the case when features and options are killed off, Microsoft does not provide much in the way of detail. While the company would probably cite low usage as the reason for retirement, it has not yet provided a specific reason. We also only have a pretty vague timeline for retirement to work with.

Why the next era of enterprise AI needs context engineering [Q&A]
The adoption rate of artificial intelligence in the enterprise shows no signs of slowing down, but while organizations have been focused on which of the many models to use, the playing field is beginning to level out.
We talked to Saket Saurabh, CEO and co-founder of Nexla, to discuss ‘context engineering’ and why he believes it will be key to gaining competitive advantage.
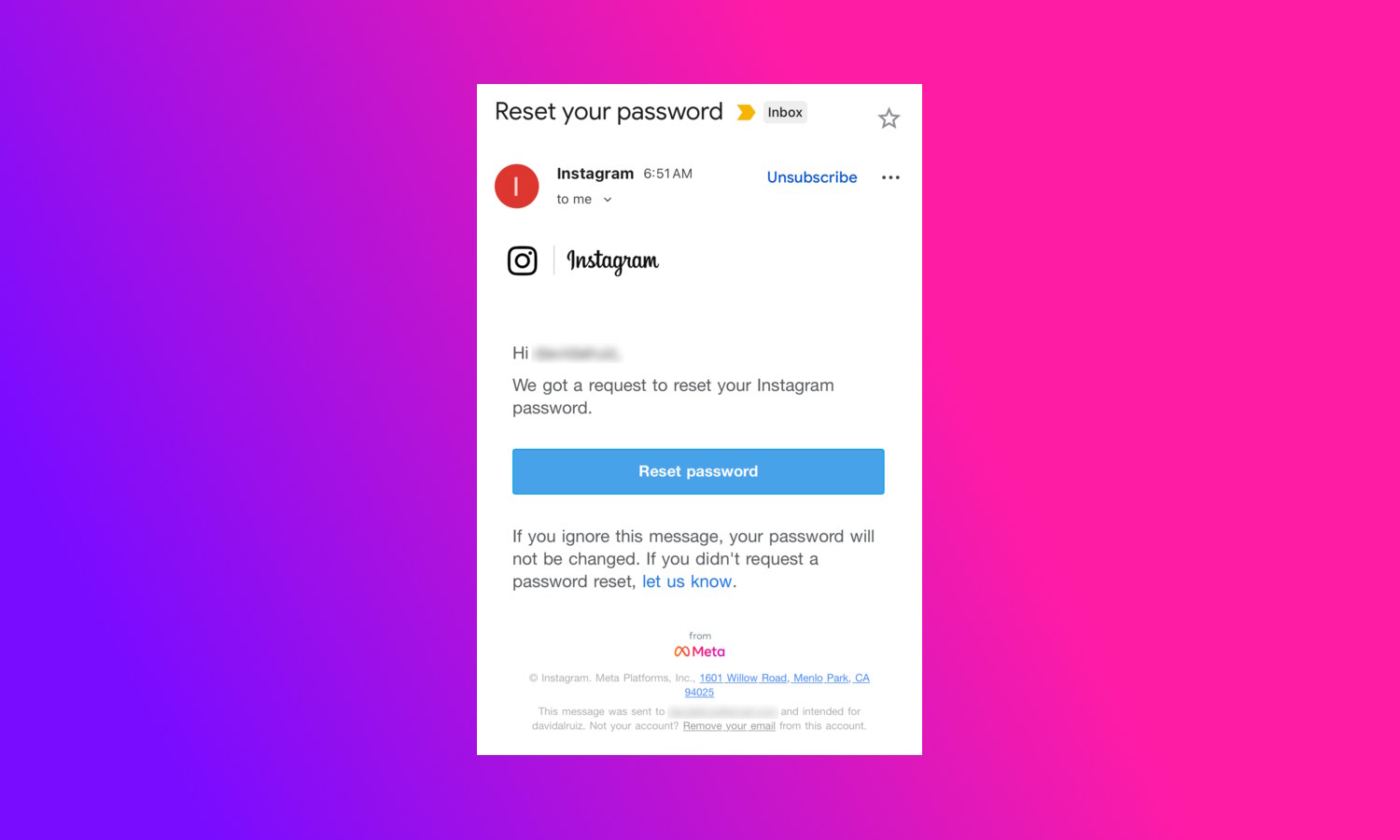
Instagram denies security breach as password reset emails are sent out
If you were concerned about your Instagram account over the weekend, you were certainly not alone. Many Instagram users received an email telling them that they needed to reset their account password, and this was quickly linked to a data breach from 2024 affecting 17.5 million accounts.
While the emails about resetting passwords really did come from Instagram, there was in fact no danger, and no need to boost account security. So far, so unclear. So, what is going on?
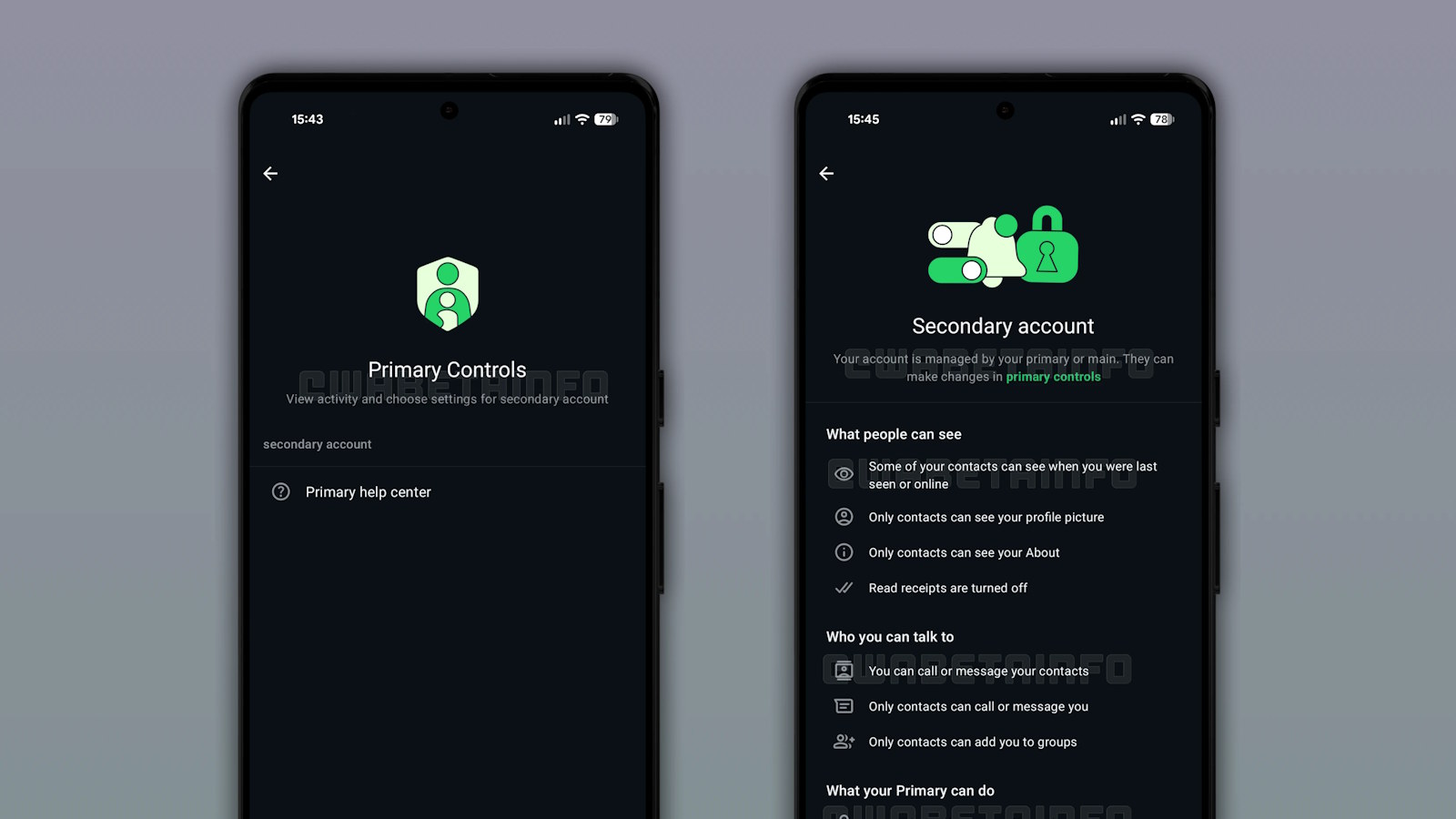
WhatsApp is working on a parental control feature using linked accounts
There are many concerns about how younger people use the internet in general, but certainly in relation to social media. There have been pushes around the world to limit – or even ban – access to the likes of Facebook, but WhatsApp is looking at a different approach.
With a messaging app, it can be difficult to keep an eye on who a child is contacting, so Meta has come up with the idea of introducing parental controls. The system is currently under development, and involves linking two accounts together – one belonging to a child, the other to a parent or guardian.

Attackers target remote work and data storage
New research from internet service provider Beaming shows UK businesses were targeted more than 791,600 times last year and attackers are focused on systems that facilitate remote work and data storage, turning them into high-risk entry points.
Remote desktop and VPN services saw sustained, automated probing throughout 2025. These are the primary targets for ransomware groups who use stolen credentials to infiltrate and encrypt corporate networks to cause total business lockout.
