
How to address cloud-native security risks in 2025
Gartner predicts that public cloud end-user spending will surpass $675 billion by the end of 2024. In 2025, as AI systems proliferate and organizations increasingly store sensitive data in public cloud infrastructure, many stakeholders will begin demanding more robust cloud security measures.
Additionally, cybercriminals are becoming more inventive than ever. They now rely on AI and machine learning (ML) to improve and iterate on their methods, just as we all do. Interestingly, despite advances in cloud security, research suggests that common vulnerabilities like unenforced multi-factor authentication (MFA) and long-lived credentials continue to expose many companies to risk. Patching these known vulnerabilities will be crucial next year.

More than half of organizations think their cloud security is inadequate
A new survey, from infrastructure management provider Pulumi, reveals that 58 percent of organizations feel their cloud security is inadequate, underscoring the critical need for enhanced security measures in cloud environments.
This echoes research from other sources which show a 75 percent increase in cloud intrusions from 2022 to 2023, and 44 percent of organizations having faced a cloud data breach -- 14 percent reporting one in the past year.

AI redefines priorities for IT leaders
A new survey from Flexera shows that 42 percent of IT leaders say they believe if they could integrate AI, it would make the most difference to their organizations.
The study surveyed 800 IT leaders from the US, UK, Germany and Australia to determine how IT decision makers' priorities have evolved over the past 12 months and outline their focus for next year.

Navigating the future: Cloud migration journeys and data security
For years, businesses have been chasing innovation with cloud platforms, moving beyond the limitations of legacy technology for greater speed and agility, and sharpening their competitive edge. However, all businesses often face challenges that complicate cloud migration, driving up costs and timelines while exposing the business to data security risks. Ultimately, these challenges block businesses from experiencing the true benefits of cloud integration, and in some cases, lead to significant breaches and regulatory fines.
The speed of cloud migration is most commonly hindered by data security concerns, budget overruns, fragmented implementations, and operational friction. These challenges -- affecting the three key stakeholders within the cloud migration strategy of Data and Analytics Leaders, Security Leaders, and IT Leaders -- often cause projects to run well beyond their planned timelines and budgets. In many cases, these migrations fail to deliver value because data utilization is restricted by inadequate security, and extended timelines erode the business’s first-mover advantage.

Majority of SaaS applications and AI tools are unmanaged
A new report reveals that 90 percent of SaaS applications and 91 percent of AI tools within enterprises remain unmanaged, suggesting a widespread vulnerability that continues to grow.
The study from Grip Security highlights the limitations of traditional security strategies in combating 'SaaS risk creep' the number of SaaS applications used in an enterprise increased by 40 percent over the last two years.

Cloud attacks grow in cost and scale
A new report from Sysdig highlights the growing cost and scale of cloud attacks and the evolution of tactics being used by attackers.
Among the findings are that over $100,000 is lost per day to AI resource jacking. It hasn't taken long for threat actors to leverage stolen cloud access to exploit large language models (LLMs), as illustrated by an LLMjacking attack that left one victim on the hook for $30,000 in just three hours. Left unchecked, an LLMjacking operation can cost more than $100,000 per day.
Old credentials never die they just present a cloud security risk
Long-lived credentials on major cloud platforms continue to be a huge risk for organizations, according to a new report from Datadog.
Long-lived cloud credentials never expire and frequently get leaked in source code, container images, build logs and application artifacts, making them a major security risk. The report finds that 46 percent of organizations are still using unmanaged users with long-lived credentials.

IT decision-makers under pressure to demonstrate public cloud adoption cost savings
Unless you’re an Olympic athlete, you probably don’t want a stopwatch tracking your performance -- pushing you to work harder and move faster. But, according to Six Degrees’ newly published independent research, one in five IT decision-makers at SMEs feel that the clock is on them when implementing public cloud migration projects.
Six Degrees’ UK SME Cloud Intelligence Report 2024 found that the extent to which IT decision-makers feel rushed varies considerably between sectors. Finance and insurance (57 percent), blue light (55 percent) and education (42 percent) are impacted the most compared to those working in government (33 percent), healthcare (32 percent) and manufacturing (29 percent).

Qualys launches cloud-based risk operations center
Organizations are facing an ever-growing volume of risk alerts spread across multiple, disconnected top-10 dashboards. This fragmented view can result in conflicting analyses, duplicate work, missed threats, and strategies that fail to fully protect the organization.
Cloud-based security firm Qualys is addressing this with the launch of a new Risk Operations Center (ROC) with Enterprise TruRisk Management (ETM) that enables CISOs and business leaders to manage cybersecurity risks in real time, transforming fragmented, siloed data into actionable insights that align cyber risk operations with business priorities.

'Toxic cloud triad' puts four in 10 organizations at risk
It might sound like a Chinese secret society, but a new report warns that a 'toxic cloud triad' of publicly exposed, critically vulnerable and highly privileged cloud workloads is putting almost four in 10 organizations at risk.
Security gaps caused by misconfigurations, risky entitlements and vulnerabilities combine to dramatically increase cloud risk according to the Tenable Cloud Risk Report.

Do you know where your sensitive data is?
Around a quarter of businesses don't know where their sensitive data is according to a new report from Normalyze and the Enterprise Strategy Group (ESG).
As enterprises move more operations to the cloud, the volume and exposure of sensitive data stored in public cloud services is also rapidly increasing. Despite efforts by security teams to manage data risks, many organizations lack clarity on where data is located, how sensitive it is, and who has access to it.

The top enterprise cloud threats of 2024
A new report from IBM X-Force looks at the biggest risks enterprises are facing and highlights how attackers know that credentials are the keys to cloud environments, making them highly sought-after on dark web marketplaces.
Attackers are using phishing, keylogging, watering hole and brute force attacks to harvest credentials. Also dark web research highlights the popularity of infostealers, used to steal cloud platform and service-specific credentials.

New AI-driven platform simplifies enterprise access management
Traditional processes for ensuring employees have the right levels of access to systems have come under strain and become harder to manage because of the spread of cloud-based software.
A new AI-powered identity governance and administration (IGA) platform from Zilla Security aims to tackle the long-standing challenge of managing hundreds of roles or group membership rules to ensure organizations give users job-appropriate access.
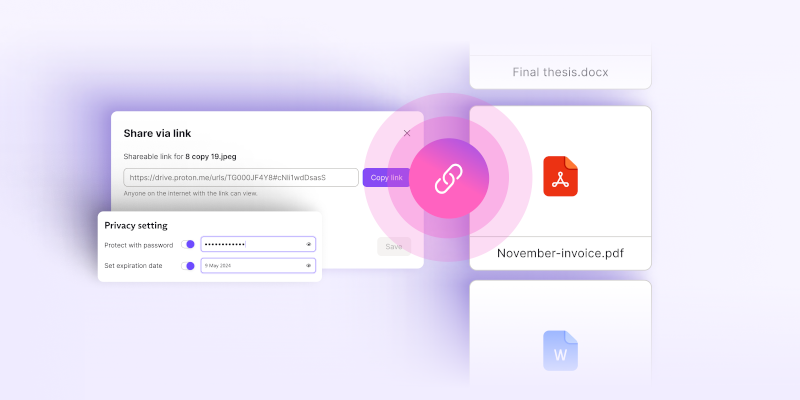
Proton launches secure cloud storage for businesses
Swiss company Proton is known for its privacy focused solutions including secure mail, VPN and password manager. Today the company launches a new service, Proton Drive for Business.
This is a comprehensive solution designed to provide secure and private cloud storage, file sharing, and real-time document collaboration for organizations. In an era where data breaches and unauthorized use of company documents are common, this new service offers security and privacy to businesses of all sizes, with end-to-end encryption.

Business security: Advancements in on-premise and online tech solutions
Biometric access control, video surveillance, and intrusion alarms enhance on-site protection by promptly addressing unauthorized access -- these advanced systems monitor who enters your facilities and allow for real-time responses to incidents.
Meanwhile, cybersecurity remains a key aspect of business demanding great attention. The emergence of generative AI and automation technologies can evaluate threats and make decisions significantly faster, heightening the effect of your defense mechanisms.
