
From application to zero trust: Identity security fundamentals to stay ahead of the threat landscape
Cybercriminals are not new, and often neither are their tactics. Despite this, phishing attacks, which incorporate social engineering in emails and messages to persuade people to perform an action that puts organizations at risk, continue to be highly successful. New technologies, such as GenAI, are improving these tactics further and companies must implement a strategic approach built on a solid foundation of identity security to minimize risks.
The most glaring vulnerability within an organization stems from human error. Mistakes such as using weak passwords, reusing credentials across multiple platforms, or falling victim to phishing attacks, can provide malicious actors with an easy gateway into secure systems. Social engineering exploits the natural human inclination to trust, deceive employees into divulging sensitive information or unwittingly granting access. Despite widespread awareness campaigns, these tactics continue to succeed, highlighting the gap between knowledge and practice, which presents a major risk to organizations.
DORA: A blueprint for cyber resilience in the U.S.
In today’s post-pandemic world, businesses are looking to shift back into the office while leveraging the learnings from the pandemic. Digital operations are going to be the new normal. With business innovations increasingly helping enterprises provide faster and easier-to-consume services to customers, the digital way of business is continuously creating a much larger digital footprint than ever before.
However, continuously increasing digital footprint also means possible targets of cyberattacks are also increasing equally rapidly. What is interesting to note is while investments in cybersecurity are increasing, so have the cyberattacks. According to CrowdStrike, attackers are moving faster within enterprises after an initial breach, with the average time it takes to hit patient 1 after patient 0 (the typical indicator of lateral movement) falling from 84 minutes to 62 minutes in the last year. Unfortunately, while many enterprises are continuing to invest in cyber security, far few invest in cyber defense, yet everyone wants the assurance of cyber resilience.

Balancing Large Language Model adoption with robust API security
The popularity of Large Language Models (LLMs) has prompted an unprecedented wave of interest and experimentation in AI and machine learning solutions. Far from simply using popular LLMs for sporadic background research and writing assistance, LLMs have now matured to the degree where particular solutions are being used within specific workflows to solve genuine business problems.
Industries such as retail, education, technology, and manufacturing are using LLMs to create innovative business solutions, delivering the required tools to automate complex processes, enhance customer experiences, and obtain actionable insights from large datasets.

Your company needs a BEC policy and five other email security trends
Hardly a week goes by without news of another email-based attack via phishing or Business Email Compromise (BEC) scam. These types of attacks can cause a great deal of damage to infrastructure and an organization’s image, whether it is a large enterprise, a small-medium business (SMB) or even much smaller retailers. The FBI (Federal Bureau of Investigation) reports that the average financial loss per BEC attack is $125,000 and last year estimated the Business Email fraud industry to be valued at a whopping $50 billion.
These attacks are increasingly creative, and typically involve impersonation of someone such as the head of an organization or finance. If someone responds on behalf of the executive, they could unknowingly give away the keys to the kingdom, causing significant losses. With that in mind, let’s review some of the larger email security trends.

Is over-focusing on privacy hampering the push to take full advantage of AI?
In 2006, British mathematician Clive Humby declared that data is the new oil -- and so could be the fuel source for a new, data-driven Industrial Revolution.
Given that he and his wife helped Tesco make £90m from its first attempt at a Clubcard, he should know. And it looks like the “derricks” out there are actually pumping that informational black gold up to the surface: the global big data analytics market is predicted to be more than $745bn by 2030 -- and while it may not be the most dependable metric, Big Tech is throwing billions at AI at a rate described as “some of the largest infusions of cash in a specific technology in Silicon Valley history”.

The double-edged sword of AI in cybersecurity
As artificial intelligence (AI) continues to advance, its impact on cybersecurity grows more significant. AI is an incredibly powerful tool in the hands of both cyber attackers and defenders, playing a pivotal role in the evolving landscape of digital threats and security defense mechanisms. The technology has seen use both by attackers to conduct cyber attacks, and defenders to deter and counter threats.
The incorporation of AI into malicious social engineering campaigns creates a new era where cyber threat actors are more convincingly deceptive. With access to a vast amount of data, cyber threat actors can both increase the success and effectiveness of large-scale phishing campaigns, or use this access to huge amounts of data to spread disinformation online.

Apple commits to at least five years of security updates for iPhones
In order to comply with the Product Security and Telecommunications Infrastructure (PSTI) Act in the UK, Apple says it will provide security updates for iPhones for a minimum of five years.
While Apple has not previously abandoned iPhone users and left them with insecure devices -- in fact, the company has been known to release updates for very old handsets in extraordinary circumstances -- it has never previously committed to any particular period of support.

Generative AI: Productivity dream or security nightmare?
The field of AI has been around for decades, but its current surge is rewriting the rules at an accelerated rate. Fueled by increased computational power and data availability, this AI boom brings with it opportunities and challenges.
AI tools fuel innovation and growth by enabling businesses to analyze data, improve customer experiences, automate processes, and innovate products -- at speed. Yet, as AI becomes more commonplace, concerns about misinformation and misuse arise. With businesses relying more on AI, the risk of unintentional data leaks by employees also goes up. For many though, the benefits outweigh any risks. So, how can companies empower employees to harness the power of AI without risking data security?
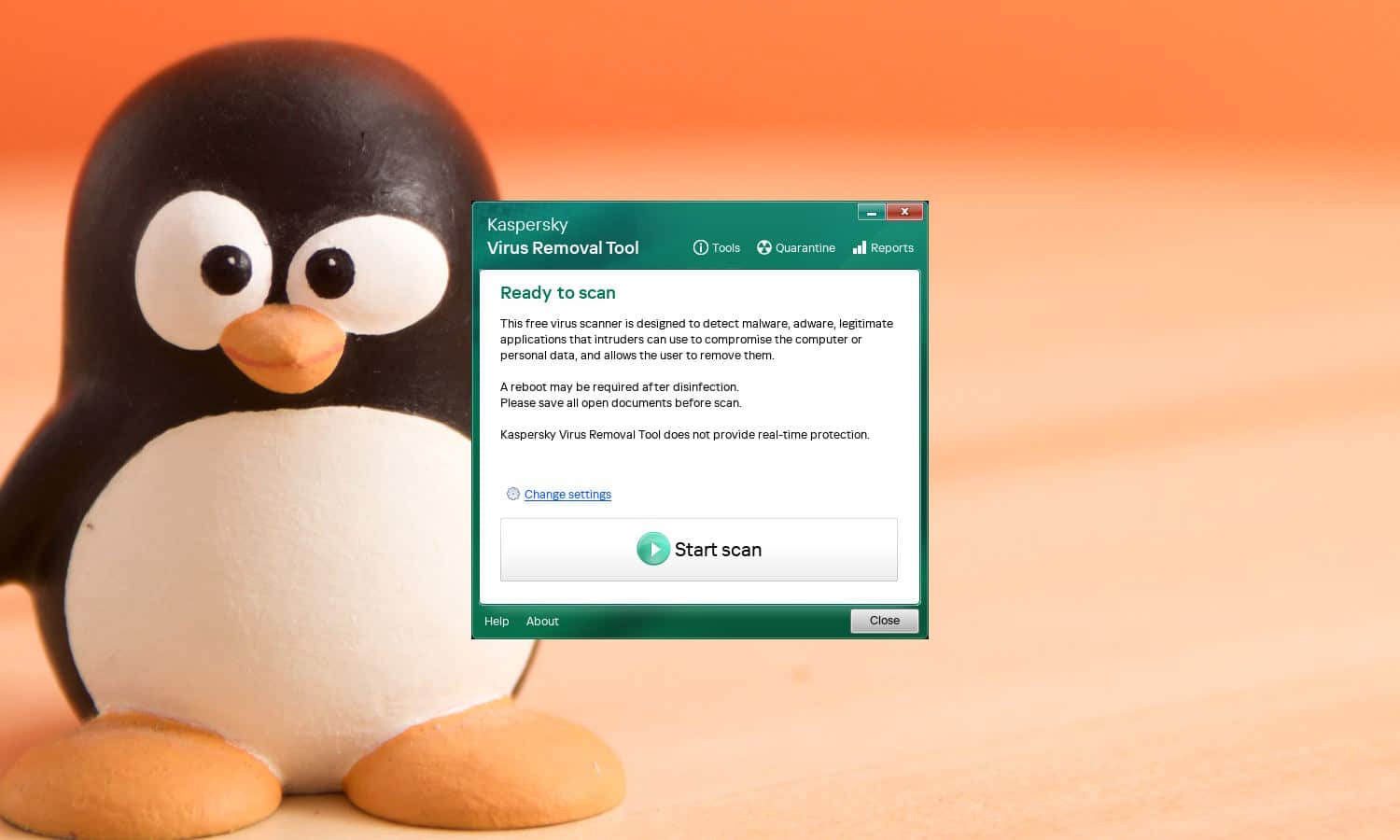
Kaspersky releases a free virus removal tool for Linux-based systems, KVRT
An urban myth used to suggest that Linux was immune to viruses and malware, and is totally secure. This is, of course, nonsense, even if the comparatively low usage makes Linux-based system less likely to be attacked than Windows or macOS.
Highlighting the fact that there is no such thing as a completely secure operating system, Kaspersky has released a new malware scanner for Linux systems. Kaspersky Virus Removal Tool (KVRT) for Linux is a free tool that, although it fails to offer real-time protection, can be used to scan for and remove various forms of malware... albeit with a slight caveat.

Compliance and cybersecurity in the age of AI [Q&A]
Artificial Intelligence is dramatically transforming the business landscape. It streamlines operations, provides critical insights, and empowers businesses to make data-driven decisions efficiently. Through machine learning, predictive analytics, and automation, AI assists in identifying trends, forecasting sales, and streamlining supply chains, leading to increased productivity and improved business outcomes. It isn't, unfortunately, without problems.
We talked to Matt Hillary, Vice President of Security and CISO at Drata, about the issues surrounding AI when it comes to critical security and compliance.

Unlocking cybersecurity success: The need for board and CISO alignment
The C-Suite’s perception of cybersecurity has evolved dramatically over the past decade. It’s gone from being an afterthought for technology departments to worry about, to a cornerstone for business survival and operational strategy. The heightened awareness of cybersecurity stems from a deeper grasp of the legal, reputational and financial implications of data breaches. This, combined with regulatory pressures such as the original NIS directive, has forced leaders to enhance their organizations’ cybersecurity measures.
The result is that 75 percent of organizations now report that cybersecurity is a high priority for their senior management team. While on the surface this should be celebrated, when digging deeper, conversations between CISOs and the wider C-Suite often just revolve around high-profile or user-centric security risks. More technical and advanced threats such as those related to application security are overlooked. The race to embrace AI and increasingly complicated cloud infrastructures have also made communicating cybersecurity priorities even more difficult for CISOs.

Balancing security and autonomy: Strategies for CISOs in the cloud era
Maintaining a secure cloud environment is one of the most important responsibilities of any CISO today, given that over 50 percent of all cyberattacks now originate in the cloud. However, this is a daunting task, as security must now be balanced against other priorities such as maintaining agile operations and the need to innovate.
Organizations today are racing to accelerate their cloud adoption due to the need for greater scalability and cost-efficiency. It has, therefore, become a critical business strategy to ensure efficiency, accessibility, and sustainability in operations. As a result, cloud investments are soaring across the board. Gartner predicts that end-user spending on public cloud services will reach $679 billion by the end of this year and exceed $1 trillion by 2027.

Six steps to safeguarding your digital identity
We lose a bit of our digital privacy with every data breach that occurs. A breach like the one at AT&T -- which exposed Social Security numbers and other personal information needed for identity theft -- is particularly serious in the landscape of data breaches. The percentage of users with Social Security numbers exposed in our data bases following the AT&T breach increased from less than 1 percent to almost 15 percent. Sensitive personal information getting out -- especially when it's easily accessible on the public internet, not just the dark web, which requires special software to be accessed -- opens you up to a huge risk of abuse.
The most notable threat users face is the potential for identity theft, where malicious actors access email, bank, and credit card accounts to impersonate victims. This can also include gaining unauthorized access to accounts by resetting passwords and even taking control of your phone number to bypass text message confirmations. What’s more, if a thief has access to your personal details, they might go as far as taking out loans or credit cards in your name -- a tactic that remains one of the most common types of identity theft.

Artificial Intelligence: What are 4 major cyber threats for 2024?
AI is one of the most powerful innovations of the decade, if not the most powerful. Yet with that power also comes the risk of abuse.
Whenever any new, disruptive technology is introduced to society, if there is a way for it to be abused for the nefarious gain of others, wrongdoers will find it. Thus, the threat of AI is not inherent to the technology itself, but rather an unintended consequence of bad actors using it for purposes that wreak havoc and cause harm. If we do not do something about these cyber threats posed by the misuse of AI, the legitimate, beneficial uses of the technology will be undermined.

Seven crucial dos and don'ts for cyber-attack survival
Think you’ve been hit by a cyber-attack? You need to move fast, but what immediate actions should you take, or should you not take? Here’s a Cyber Incident Responder’s guide to steer you through the turmoil. The actions your team takes -- or doesn’t take -- can greatly impact the overall duration of recovery, cost, and the potential to uncover vital evidence left by threat actors within your infrastructure.
Identifying a cyber security incident can be challenging. Many threat actors have mastered the art of quietly infiltrating IT systems and hiding their digital footprints. Not all cyber-attacks are as overt as encryption-based ransomware or mandate fraud. The rise of encryption-less ransomware and corporate and state-level espionage is concerning. These silent intruders can lead to data and intellectual property (IP) loss, diminished competitive edge or market share, potential regulatory fines, and reputational damage. All of which can be just as devastating, if not more so, to an organization, its employees, and investors, than a single ransomware incident.
