Malwarebytes launches free safe browsing extension for Chrome and Firefox
People are spending more of their time and managing more of their lives on the internet, so it's little wonder that the web is a rich hunting ground for cybercriminals and scammers.
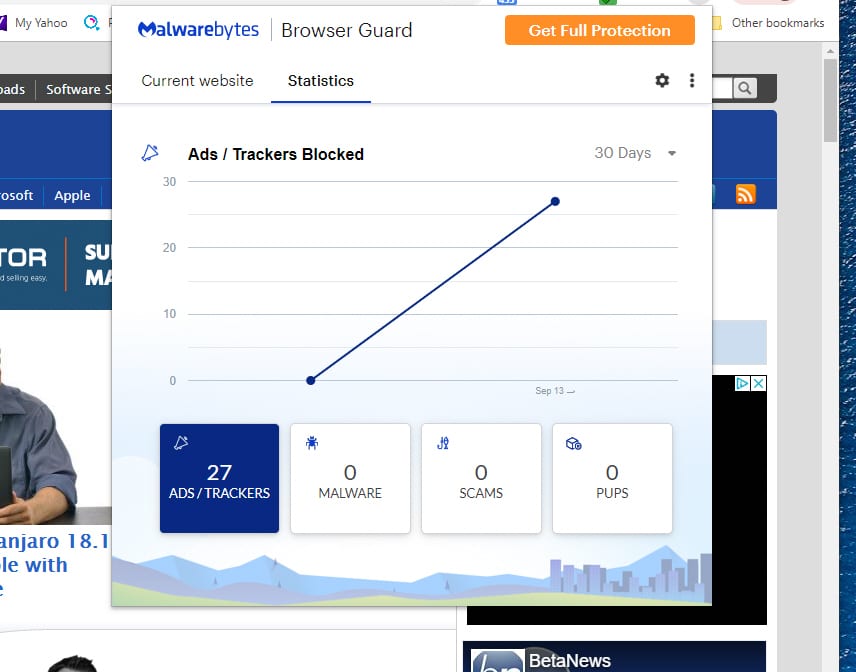
In order to make using the internet safer, Malwarebytes is launching Browser Guard, a free browser extension aimed at safeguarding consumers from scammers, and allowing them to browse up to four times faster.

Software isolation utility Sandboxie is now free; soon it will be open source too
Sandboxie -- the sandboxing tool with the tagline "Trust no program" -- has been made into a free utility. But more than this, Sophos also plans to make the software open source in the near future.
The company says that it was a difficult decision to make, pointing out that Sandboxie has never been a significant component of its business. While simply shutting down the app would have been the easiest and cheapest thing to do, Sophos says: "we love the technology too much to see it fade away".

Attacks using IoT devices escalate in 2019
Cyber criminals have upped the intensity of IoT attacks and those using Windows SMB in the first half of 2019, according to a new F-Secure report.
F-Secure's honeypot servers measured a twelvefold increase in such events compared to the same period a year ago. The increase was driven by traffic targeting the Telnet and UPnP protocols, which are used by IoT devices, as well as the SMB protocol, which is used by the Eternal family of exploits to propagate ransomware and banking Trojans.

Phishing attacks against the Apple brand reach 1.6 million in six months
There have been 1.6 million phishing attacks targeting the Apple brand name in the first half of 2019. This is up nine percent on the total number of attacks seen last year, revealing a growing trend.
These figures come from Kaspersky's Threats to Mac Users Report 2019, released this week, which shows the number of cases where users faced fraudulent web pages utilising the Apple brand as a decoy has increased significantly in the first six months of the year.

D-Link and Comba routers have multiple vulnerabilities, including storing passwords in plain text
A security researcher has revealed details of a series of vulnerabilities in routers made by D-Link and Comba which make it easy to see usernames and passwords.
Simon Kenin from Trustwave SpiderLabs -- an "elite team of ethical hackers, forensic investigators and researchers" -- found a total of five security flaws which involve the insecure storage of credentials. In some instances, passwords are stored in plain text and can be seen by anyone with network or internet access to the routers in question.

98 percent of top US websites not prepared against attacks
Most websites within the Alexa 1000 ranking in the US are not prepared to face advanced client-side attacks like Magecart according to analysis carried out by Tala Security.
Findings from the Tala 2019 State of the Web Report show the average website relies on 31 third-parties. Nearly two-thirds (63 percent) of the externally loaded JavaScript code executed in the browser is either written by and/or managed by third-parties.

China-based espionage group attacks high level targets
The China-based Thrip group was first exposed in 2018 and has carried out attacks across South East Asia, mainly targeting military organizations and satellite communications operators.
New research from Symantec shows that since June 2018 Thrip has attacked 12 targets located in Hong Kong, Macau, Indonesia, Malaysia, the Philippines, and Vietnam. Analysis of the attacks shows close links to another long-established espionage group called Billbug making it likely the two are the same.

Training program helps find future cybersecurity talent [Q&A]
The shortage of cybersecurity talent is well known and among attempts to address it in the UK is the Cyber Discovery program, backed by the Department for Digital, Culture, Media and Sport (DCMS) and delivered by the SANS institute.
Over 46,000 teenagers have taken part in the last two years, so as the program returns for its third year we spoke to James Lyne, CTO of the SANS institute to find out more about its aims and achievements to date.

Apple criticized for insensitively downplaying Google's iOS vulnerability revelations
Apple has tried to downplay concerns raised by Google about security vulnerabilities in iOS that could be exploited by malicious websites. Google's Project Zero recently revealed details of flaws in iOS that were being used to target and monitor iPhone users.
Other security researchers went on to warn that the vulnerabilities were being used to target Uyghur Muslims, possibly in a campaign run by the Chinese government. Having remained silent for more than a week after the revelations, Apple finally issued a statement responding to the findings, prompting criticism that the company was trying to downplay the issues.

IT security professionals don't trust politicians to produce effective regulations
Trust in politicians is at something of a low at the moment and at the same time we regularly see them calling for cyber measures, like backdoors to encryption, without seemingly understanding the implications.
The results of a new survey therefore shouldn't come as too much of a surprise.

SMBs focused on improving IT security
Improving security remains the top priority for mid-sized businesses, but they need to be more proactive in their approach to managing IT according to a new report.
The 2019 State of IT Operations for Small and Midsize Businesses report from infrastructure management specialist Kaseya shows 32 percent of respondents experienced a security breach in the past five years, down slightly from 35 percent in 2018 with at least 10 percent of respondents reporting that they were hit by a breach in the past year.

Massive Facebook leak exposes 419 million users' phone numbers
In its latest privacy lapse, Facebook has exposed the phone numbers of hundreds of millions of users on an unsecured server.
Databases on the server were not password-protected, and included details of 133 million US users, 50 million in Vietnam, and 18 million in the UK. In all 419 million records could be accessed by anyone looking in the right place.

Integration with MITRE ATT&CK framework delivers improved security skills training
Traditional cyber security training is often based on out-of-date attack methodologies which means the skills learned quickly becoming outdated. While cybercriminals are continuously innovating, training for security professionals is lagging behind.
Skills development platform Immersive Labs has announced an integration that allows organizations to base cyber skills training on MITRE ATT&CK, meaning organizations can map and manage specific people’s skills, to actual risks.

Security professionals now think cloud is safer than on-premise
New research from internet infrastructure company Nominet finds that 61 percent of security professionals believe the risk of a security breach is the same or lower in cloud environments compared to on-premise.
The study of nearly 300 UK and US C-level security professionals, marks a major shift in the perception of security of the cloud. However, it doesn't mean the cloud is viewed as entirely safe.

Phishing attacks target UK SMBs
According to a new study 43 percent of UK SMBs have suffered phishing attacks involving attempts to impersonate staff in the last year.
More concerning is that of those attacks 66 percent were successful in compromising data. The study from security and data anlaytics company CybSafe also finds only 47 percent of those surveyed say they have already got a cyber security training and awareness program in place.
