
Why organizations need to increase their focus on zero-day threats
Zero-day exploits are some of the most critical cybersecurity threats facing businesses today, but also one of the most difficult to address. Cybercriminals that exploit zero-day vulnerabilities take advantage of flaws within an organization's software and security systems before the victim itself discovers it. This can lead to potentially devastating consequences when bad actors are successful in accessing critical data and networks undetected.
It is also much harder to defend against these attacks when the victim is fighting in the dark - how can an organization fix a vulnerability when they don’t know it is there? For this reason, there are thousands of organizations across the world operating with unknown gaps in their cybersecurity defenses that are vulnerable to zero-day threats

F-Secure launches free online tool to generate secure passwords
With almost depressing regularity we see lists of commonly used and easily cracked passwords. The problem is that although we all know we should use strong passwords creating them is hard.
If you're struggling to come up with strong passwords don't worry, cybersecurity company F-Secure is riding to your rescue with the launch of a new, free online Strong Password Generator tool.

Organizations vulnerable to emerging threats as they struggle with malware analysis
Almost every organization is struggling with malware analysis according to a new report from infrastructure protection company OPSWAT.
The study finds 94 percent of organizations are finding it challenging to recruit, train, and retain malware analysis staff. In addition 93 percent of organizations are challenged by malware analysis tools that lack automation, integration, and accuracy. This leads to over 20 percent of organizations reporting they are unable to investigate and resolve a majority of their malicious files or alerts.

85 percent of organizations have suffered ransomware attacks
In the past five years 85 percent of organizations have suffered a ransomware incident, while 74 percent have had more than one.
A new report from ExtraHop based on a survey conducted by Wakefield Research shows that 77 percent of IT decision makers are very or completely confident in their company's ability to prevent or mitigate cybersecurity threats.

How enterprises can boost security with vulnerability management [Q&A]
Cyberattacks come in many different forms and it’s important for businesses to understand where they're vulnerable in order to mount an effective defense.
We spoke to Ed Williams, cybersecurity specialist at Trustwave, to find out more about vulnerability management, why it's important and how it fits into an organization's overall security strategy.

In the Russia-Ukraine conflict, Anonymous is working quicker than government red-tape [Updated]
While the US and other NATO nations continue to plan and implement sanctions and possible other means of making Vladimir Putin and his Oligarchs feel some pain over what they are currently doing, Hacktivist group Anonymous has already made its choices and has quickly started implementing its own set of consequences upon those responsible for alleged war crimes.
As of Saturday morning, the group had taken down websites of the Kremlin, the Russian Department of Defense and Russian DUMA (the lower house of the federal assembly). The sites were taken down rather quickly once Anonymous targeted them but periodically popped back to life, only to have that life snuffed backed out again by renewed efforts.

Electron Bot malware is running rampant in the Microsoft Store, opening backdoors on victims' computers
Fake versions of popular games such as Temple Run and Subway Surfers are being used to distribute dangerous malware through the Microsoft Store to users of Windows 10 and Windows 11.
Security firm Check Point Research found that malicious versions of the titles were riddled with Electron Bot malware and have already infected thousands of computers in countries incuding Sweden, Bulgaria and Russia. The malware gives an attacker a backdoor into a victim's computer allowing for complete system control, as well as control of social media accounts.
While the Government talks possible cyber repercussions on Russia, Anonymous is beyond that stage
As you know, Russia has begun an invasion of its neighboring country of Ukraine. It was long expected, despite the denials that continued to pour out of Russian president, Vladimir Putin. All of the planning was picked up by intelligence gatherers, the images of massing troops by both satellites and naked eye cameras. Helen Keller would have known this was coming.
US President Joe Biden has met with cyber security advisors to see what can be offered in the way of cyber-attacks to go along with sanctions being imposed on Putin and his circle. None can be done without having an effect on citizens, but hopefully those issues can be minimized.

2021 holiday season saw a sharp increase in eCommerce bot attacks
The past holiday season saw an unusually high level of malicious bot activity in the retail and commerce industries according to new data from Akamai and RH-ISAC (Retail and Hospitality Information Sharing and Analysis Center).
Attacks included credential stuffing and account takeover (ATO) attacks unleashed by malicious bot operators, as well as Log4j exploitation attempts and web application firewall (WAF) assaults, all of which have been about bad actors setting their sights and pointing their tools at eCommerce players.

One in six endpoints has identity risks
Many data breaches have unmanaged, misconfigured or exposed identity details at their core. Yet despite this, businesses continue to lack visibility into their identity risk.
A new study from Illusive reveals as many as one in six enterprise endpoints it analyzed had some form of identity risk.

Microsoft Defender for Cloud now protects Google Cloud Platform
Windows users are familiar with Microsoft Defender running on their computers offering local protection, but there is also a cloud-based version of the security tool. Microsoft Defender for Cloud is the result of the unification of Azure Security Center and Azure Defender.
Having already added support for Amazon Web Services (AWS), Microsoft has now added protection for Google Cloud Platform. The latest addition comes as Microsoft recognizes the fact that 92 percent of organizations now embrace a multi-cloud strategy.

Sophisticated new phishing attack impersonates DocuSign
The use of electronic signatures has become commonplace for many business transactions, cutting out the need for face-to-face meetings and couriering documents.
This though makes the signing process an attractive target for cybercriminals. Researchers at Armorblox have uncovered a sophisticated credential phishing attack impersonating e-signature leader DocuSign.

Ransomware is not enough -- 83 percent of attacks now feature other extortion tactics
Ransomware itself is bad enough, but 83 percent of successful ransomware attacks now include alternative extortion methods according to a survey by machine identity company Venafi.
Popular techniques include using the stolen data to extort customers (38 percent), exposing data on the dark web (35 percent), and informing customers that their data has been stolen (32 percent).

Ransomware impacts 80 percent of enterprises
A new survey reveals that 80 percent of companies have experienced a ransomware attack, despite spending an average of $6 million annually on ransomware mitigation.
The study, from cyber advisory and solutions firm CBI, based on research by the Ponemon Institute and co-sponsored by Check Point, finds Companies are spending $170,000 per ransomware incident on staffing alone, with an average of 14 staff members each spending 190 hours on containment and remediation activities.
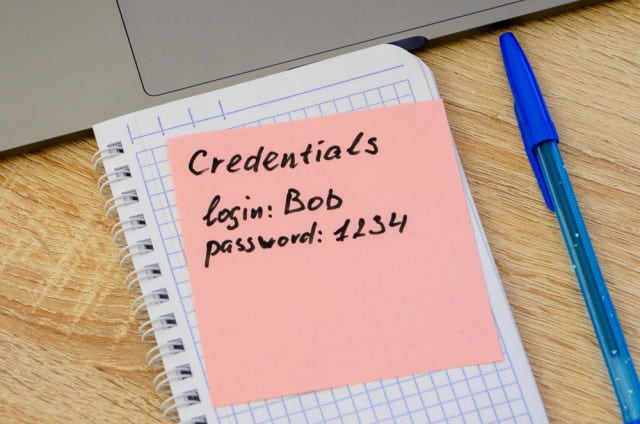
Data leaks from exposed credentials rise 50 percent
The number of major data leak incidents as a result of exposed credentials rose by 50 percent in 2021 according to a new report.
The 2021 industry report from CybelAngel finds data leaks are the most common digital risk faced by enterprise customers, with leaks overall showing a 63 percent year-on-year growth.
