Microsoft drops password expiration policies from Windows 10 1903 security baseline
In new draft security baseline documentation, Microsoft has scrapped the policy that requires users to change their passwords on a regular basis.
The new security settings apply to Windows 10 version 1903 and Windows Server version 1903, and the change sees Microsoft conceding that its policy of forcing periodic password changes is "an ancient and obsolete mitigation of very low value". The company has a series of suggestions for how to better improve password security.
See also:
- Microsoft will block the Windows 10 May 2019 Update if you have a USB drive or SD card connected
- Microsoft decides to keep Paint in Windows 10... for now
- Microsoft displays warning messages in Windows 7 about the impending end of support
- Microsoft may have abandoned Sets in Windows 10 -- what now for app tabs?
The new proposed security baseline is set out in a post on the Microsoft Security Guidance blog by Aaron Margosis. In the post, he points that by forcing people to change their passwords, they are more likely to either forget them or choose something predictable -- something which runs counter to the idea of password security.
Margosis says:
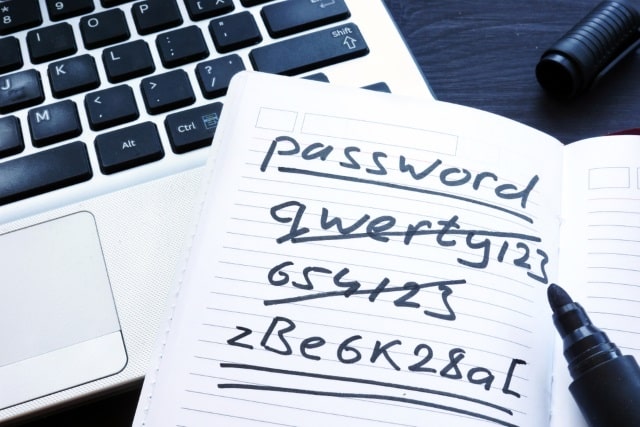
There's no question that the state of password security is problematic and has been for a long time. When humans pick their own passwords, too often they are easy to guess or predict. When humans are assigned or forced to create passwords that are hard to remember, too often they’ll write them down where others can see them. When humans are forced to change their passwords, too often they'll make a small and predictable alteration to their existing passwords, and/or forget their new passwords. When passwords or their corresponding hashes are stolen, it can be difficult at best to detect or restrict their unauthorized use.
He goes on to explain the reason for the change, stressing that Microsoft is not looking to make other changes to password requirements such as the length or complexity.
Periodic password expiration is a defense only against the probability that a password (or hash) will be stolen during its validity interval and will be used by an unauthorized entity. If a password is never stolen, there’s no need to expire it. And if you have evidence that a password has been stolen, you would presumably act immediately rather than wait for expiration to fix the problem.
If it's a given that a password is likely to be stolen, how many days is an acceptable length of time to continue to allow the thief to use that stolen password? The Windows default is 42 days. Doesn't that seem like a ridiculously long time? Well, it is, and yet our current baseline says 60 days -- and used to say 90 days -- because forcing frequent expiration introduces its own problems. And if it's not a given that passwords will be stolen, you acquire those problems for no benefit. Further, if your users are the kind who are willing to answer surveys in the parking lot that exchange a candy bar for their passwords, no password expiration policy will help you.
Our baselines are intended to be usable with minimal if any modification by most well-managed, security-conscious enterprises. They are also intended to serve as guidance for auditors. So, what should the recommended expiration period be? If an organization has successfully implemented banned-password lists, multi-factor authentication, detection of password-guessing attacks, and detection of anomalous logon attempts, do they need any periodic password expiration? And if they haven't implemented modern mitigations, how much protection will they really gain from password expiration?
The results of baseline compliance scans are usually measured by how many settings are out of compliance: "How much red do we have on the chart?" It is not unusual for organizations during audit to treat compliance numbers as more important than real-world security. If a baseline recommends 60 days and an organization with advanced protections opts for 365 days -- or no expiration at all -- they will get dinged in an audit unnecessarily and might be compelled to adhere to the 60-day recommendation.
Periodic password expiration is an ancient and obsolete mitigation of very low value, and we don't believe it's worthwhile for our baseline to enforce any specific value. By removing it from our baseline rather than recommending a particular value or no expiration, organizations can choose whatever best suits their perceived needs without contradicting our guidance. At the same time, we must reiterate that we strongly recommend additional protections even though they cannot be expressed in our baselines.
While the proposed change is not going to affect home users, it may encourage business and enterprise users to look at their security policies more closely.
Image credit: designer491 / Shutterstock