
Three billion spoofed emails sent each day
A new report looking at trends in DMARC adoption shows that while take up of the identity verification technology is increasing, three billion messages per day are still spoofing the sender's identity.
The study from Valimail shows that email remains a favourite attack route, implicated in over 90 percent of all cyberattacks with the pandemic providing a new focus.

Return to offices means new opportunities for phishing
The move to home working provided new opportunities for phisherfolk, but as many people start to return to their offices the attackers are pivoting to exploit that too.
A new report from email phishing protection specialist INKY shows attacks are capitalizing on vulnerability and the desire for accurate information about returning to the office in-person.

Why email is still the favorite way of delivering cyberattacks [Q&A]
Although business IT has seen many changes over the last year, email remains the main vector for carrying out cyberattacks.
In its latest Global Security Report Zix looks at the trends in email attacks over the last year and the impact they have. We spoke to David Wagner, president and CEO of, Zix to find out more.

Cybercriminals keen to cash in on vaccine interest
The past few months have seen plenty of news surrounding COVID-19 vaccines, from the buzz surrounding roll outs to fears of possible side effects.
As always with a major news event cybercriminals seek to exploit the opportunity it presents. Cloud-native email security company GreatHorn has identified a new pattern of techniques being used to exploit the unease of vulnerable email users by spoofing critical vaccine information.

Facebook enables the use of hardware security keys on mobile devices
Facebook is expanding support for physical security keys to mobile devices in order to help users secure their accounts.
The site already offers multi-factor authentication via SMS or authenticator apps, but adding support for hardware keys offers users another means of supplementing their passwords and keeping their accounts more secure.
Phishing campaign uses US tax season to lure victims
Researchers at Cybereason have detected a new campaign targeting US taxpayers with documents that purport to contain tax-related content.
These deliver NetWire and Remcos -- two powerful and popular RATs which can allow attackers to take control of the victims' machines and steal sensitive information. The malicious documents used are roughly 7MB in size, which allows them to evade traditional AV mechanisms and heuristic detection.

71 percent of Office 365 users suffer malicious account takeovers
New research from network detection and response company Vectra AI shows that 88 percent of companies have accelerated their cloud and digital transformation projects due to COVID-19.
But it also finds that 71 percent of Microsoft Office 365 deployments have suffered an account takeover of a legitimate user's account, not just once, but on average seven times in the last year.

Ransomware up 62 percent since 2019
Cybercriminals are using more sophisticated ransomware tactics and more dangerous variants, like Ryuk, to earn an easy payday. This has seen a 62 percent increase globally and a 158 percent spike in North America since 2019.
The latest Cyber Threat Report from SonicWall highlights how COVID-19 has provided threat actors with opportunities for more powerful, aggressive and numerous attacks, thriving on the fear and uncertainty of remote and mobile work forces navigating corporate networks from home.

Free tool helps enterprises assess their Active Directory security
Microsoft Active Directory (AD) is used by 90 percent of enterprises as the primary source of trust for identity and access, but it's also exploited in many cyberattacks.
Since AD is rarely safeguarded effectively, attackers have come to depend on weak configurations to identify attack paths, access privileged credentials and get a foothold in target networks.

29 percent of threats previously unknown as hackers update tactics
The latest Quarterly Threat Insights Report from HP shows that 29 percent of malware captured between October and December 2020 was previously unknown, due to the widespread use of packers and obfuscation techniques by attackers seeking to evade detection.
In addition 88 percent of malware was delivered by email into users' inboxes, in many cases having bypassed gateway filters. It took 8.8 days, on average, for threats to become known by hash to antivirus engines, giving hackers over a week’s head-start on their campaigns.
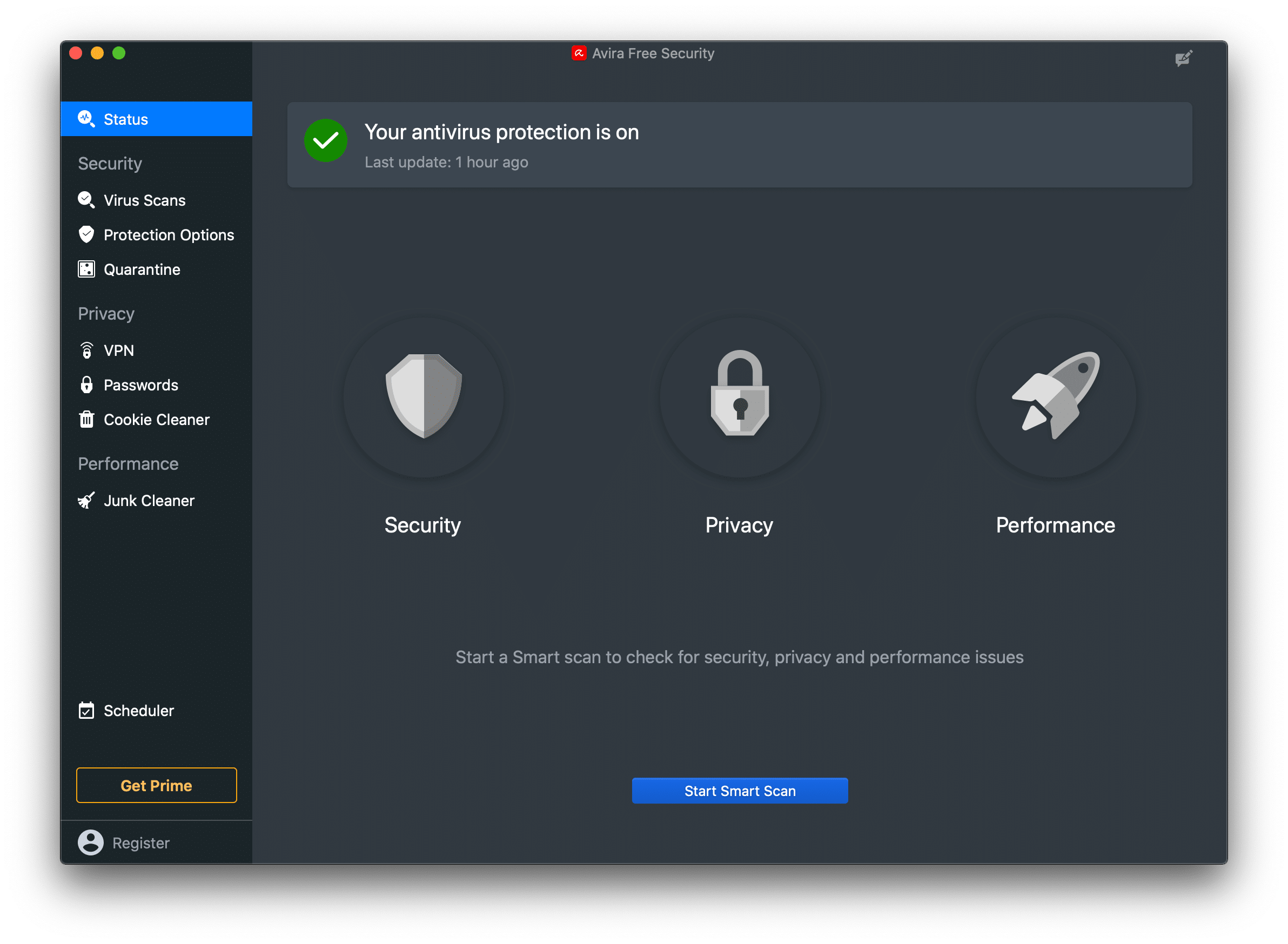
Avira launches new security product for Mac systems
German cybersecurity company Avira is launching a new security for Mac product with free as well as premium versions, developed from the ground up on Apple’s latest tech stack.
The all-in-one solution blocks and removes threats, enables worry-free browsing, shopping and payment through real-time protection, and protects data with VPN encryption.

Public key infrastructure and digital certificates essential to zero trust
Public key infrastructure (PKI) and digital certificates are essential to achieving zero trust architecture according to 96 percent of North American enterprises.
However, only 39 percent use PKI as part of their zero trust security strategy today according to a survey from Pulse Research and PKI as-a-Service (PKIaaS) company Keyfactor.

Businesses more likely to buy from companies offering ongoing security
Technology providers that are transparent and proactive in helping organizations manage their cybersecurity risk are more likely to win business according to a new study from Intel.
The results show 73 percent of respondents say their organization is more likely to purchase technologies and services from technology providers that are proactive about finding, mitigating and communicating security vulnerabilities, while 48 percent say their technology providers don’t offer this capability.

Why security and observability are key to software development [Q&A]
Developers are under increasing pressure to create real-time products that make the most of a wide range of digital resources.
This means that DevOps teams have to cope with information drawn from all sorts of different sources. But how can they ensure they are getting an accurate picture?
Linux kernel found to have a trio of 15-year-old vulnerabilities that could allow root access
Linux-based operating systems are generally recognized as being far more secure than the likes of Windows and macOS -- but that's not to say they're without their flaws. Illustrating precisely this is the discovery of no fewer than three vulnerabilities in the Linux kernel that could be exploited to gain root access to a system.
That researchers from cybersecurity firm GRIMM managed to find so many vulnerabilities in the Linux kernel is one thing, the fact that they have lain there undetected for 15 years is quite another.
