Researchers find two Android malware campaigns with over 250 million downloads

Check Point Research has uncovered two massive mobile adware and data stealing campaigns, which have already had a combined total of over 250 million downloads globally.
Both target mobiles using Android, and exploit the mobile app development supply chain to infect devices and perform malicious actions.
New Android malware uses code injection to control devices

Researchers at Kaspersky Lab have released details of a new trojan being distributed via the Google Play store that is able to inject malicious code into the system runtime libraries.
Named Dvmap, the trojan is believed to have been downloaded from Google Play more than 50,000 times since March this year.
Android malware HummingBad is back on Google Play

A common recommendation that Android users get for avoiding malware is to stick with Google Play and not download any apps from other sources. Trouble is, as HummingBad proved early last year by penetrating the search giant's defenses, that advice is not exactly bullet-proof.
The malware generated $300,000 in revenue every month and infected over 85 million devices, which, at the time, ran popular versions of Android, like KitKat and Jelly Bean. It was also one of the most dangerous pieces of malware in 2016, representing 72 percent of attacks on mobile and ranking fourth in Check Point's list of "the most prevalent malware globally" in the first half of the year. But that is not the end of the saga, as a new variant, called HummingWhale, has been found on Google Play.
New Android malware breaches over a million Google accounts

Researchers at cyber security company Check Point have uncovered a new malware variant that has breached more than a million accounts and is infecting over 13,000 Android devices a day.
Called Gooligan, the malware roots Android devices and steals email addresses and authentication tokens stored on them. With this information, attackers are able to access users' sensitive data from Gmail, Google Photos, Google Docs, Google Play, and G Suite.
Android malware HummingBad generates $300,000 in monthly revenue

When we discuss mobile malware we usually look at the technological aspects, specifically how it's designed, how it spreads, what devices it targets, how it affects them after infection, and how it can removed. What we rarely get to talk about is the financial side of things, which in the case of certain types of malware is the primary interest of their creators.
Check Point has published a report on the HummingBad malware campaign, finding that it generates $300,000 a month in fraudulent revenue with a pool of 85 million infected Android devices across the globe at its disposal. In a year attackers are looking at about $3.6 million in revenue, assuming the number of devices does not expand considerably.
Android malware snaps secret pics of porn seekers

A new piece of Android malware appears to offer pornographic images but instead takes pictures of the user via the phone’s front facing camera, then locks up the device and demands a $500 ransom.
Called Adult Player it was discovered by researchers at Zscaler. Having checked that a camera is available and taken a picture, it sends details of the victim's device and operating system to the remote servers before displaying the user’s picture on a personalized ransom screen.
Android malware drops, but there are still nearly 10 million affected devices

Google says that it is keen for Android to be a secure platform for developers and end users alike. It's not a unique claim; Apple would likely say much the same about iOS, and Microsoft about Windows Phone/Windows 10 for Phones.
To demonstrate how fervently it has been working away at improving security and introducing new security-focused features, Google today published a report looking back on Android security in 2014. Dubbed the Android Security State of the Union 2014, it makes for interesting reading. It includes the revelation that nearly 10 million Android devices have potentially harmful apps installed.
Say cheese! -- new Android malware can hijack your camera

Remote access toolkits (RATs) for Android are nothing new, but until now they've mostly targeted the Asia region.
Now researchers at mobile security specialist Lookout have uncovered Dendroid, a custom RAT aimed at users in western countries. Dendroid’s author is selling the toolkit online with payment in virtual currencies like Bitcoin and even offers a warranty promise that it will remain undetected.
Sneaky Android malware calls premium rate numbers when you’re not looking

You might think that dialer malware went out with dial-up modems and that in these days of broadband you don't need to worry about viruses that call premium rate numbers in order to earn criminals money.
But researchers at mobile security specialist Lookout have uncovered a new piece of malware called Mouabad.p that tries to make money by making calls from your Android smartphone. Of course smartphone fraud involving premium SMS messages isn't new but making calls represents a step up in the malware's functionality.
'NotCompatible' Android malware now being spread through spam

Security firm Lookout reports that it has a seen a staggering increase in the number of NotCompatible detections this week. While not a new threat (it first appeared last May), the remote proxy malware has moved on from infecting Android devices through hacked websites and is now spreading via email spam.
Once installed, NotCompatible turns the infected phone into a proxy which is used to commit online fraud, such as through the purchase of concert tickets.
New Android malware threat: over 100,000 devices infected so far

Malware on Android devices is a real and growing threat, and one that is only likely to worsen. The latest Trojan to be found in the wild is a particularly nasty piece of coding named MMarketPay.A by TrustGo, the mobile security company that discovered it. Believed to have infected more than 100,000 smartphones in China, the Trojan downloads paid apps and videos from Mobile Market (M-Market), China Mobile’s official app store, without the user’s knowledge, resulting in some pretty hefty bills.
The malware is picked up by downloading infected apps from one of nine app stores (nDuoa, GFan, AppChina, LIQU, ANFONE, Soft.3g.cn, TalkPhone, 159.com and AZ4SD) and once installed on a device, it bypasses M-Market’s SMS security step, and begins placing orders and downloading content.
Android malware woes look a lot like Windows'

McAfee says that Android malware is taking a worrisome turn, with cybercriminals mimicking popular strategies used against Windows. The latest attacks tap IRC bots, where the malware gets further operating instructions from an Internet chatroom.
Called Android/Multi.dr, the attack masks itself as the game Madden NFL 12. Multi.dr is comprised of three separate components, including a root exploit, an IRC bot, and SMS Trojan.
Calm down, Android malware makes up a tiny .00024% of the threat landscape
Security researchers and software companies have been warning of the shift to mobile-borne malware for years, and Android seems to be the primary platform of concern.
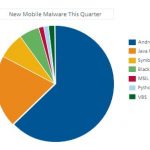
Over the last two years, we've witnessed the arrival of Android anti-malware applications from Symantec, McAfee, AVG, Softwin (BitDefender), ESET, F-Secure, and Lookout Security, and each time a new product is released, a new warning of the potential destruction a mobile virus, trojan, or botnet has is released.
Android malware can record and upload phone conversations

With the focus lately being on the security holes within iOS, media attention on flaws within Android has subsided. That ended Monday as security firm CA revealed a new Trojan, aimed at the mobile OS, that records the details of incoming and outgoing calls as well as the actual audio itself.
There are already Android Trojans in the wild that have the capability to store call information. This Trojan in particular however stores the audio of the phone call in .amr format on the SD card within the device. Worse yet, it appears to store a configuration file in the phone's memory, complete with remote server details.
Google removes Android malware so you don't have to

Android handsets infected with malware are getting a cleaning job from Google. On March 2nd, Google removed 21 apps from the Android Marketplace that contained malicious code (the number of infected apps is now 58). Now Google is "remotely removing the malicious applications from affected devices" and "pushing an Android Market security update to all affected devices that undoes the exploits to prevent the attacker(s) from accessing any more information from affected devices," according to a blog post by Rich Cannings, Android security lead.
Whoa. That's scary reassuring: Knowing Google can reach down to Android handsets to swat malicious code and undo its impact and simply that Google can reach down into devices at all. I mean whoa. "This remote application removal feature is one of many security controls the Android team," Cannings writes. Last year he defended the remote removal feature after Google nixed some applications. "This remote removal functionality -- along with Android's unique Application Sandbox and Permissions model, over-the-air update system, centralized Market, developer registrations, user-submitted ratings, and application flagging --provides a powerful security advantage to help protect Android users in our open environment."
© 1998-2025 BetaNews, Inc. All Rights Reserved. About Us - Privacy Policy - Cookie Policy - Sitemap.