
New platform helps enterprises prevent breaches on SaaS apps
As more and more data moves outside the network perimeter into SaaS applications, this can become a blind spot for security teams trying to control access.
To address the issue DoControl is launching a fully automated SaaS data access platform, providing data access monitoring, orchestration, and remediation across major SaaS apps, including Google Drive, Box, Microsoft OneDrive, Salesforce, and others.

New Target Temptation Engine aims to predict where attackers will strike
Traditional cybersecurity solutions throw up lots of information, making it hard for businesses to identify the threats that they should be prioritizing.
To help security teams focus on the issues that matter most, Randori is launching a 'Target Temptation Engine' that aims to offer defenders the attacker's perspective.

Tackling the social engineering bonanza caused by the Microsoft Exchange hack [Q&A]
In early March, Microsoft disclosed that Chinese hackers had exploited software vulnerabilities in Microsoft Exchange on-premises servers to gain access to the email accounts of thousands of Microsoft customers.
While these companies are now laser-focused on deploying patches and other security measures to remediate the vulnerabilities in their email software, Josh Douglas, VP of product management -- threat intelligence at Mimecast, believes these technical fixes will only go so far.

Remote working creates new security issues
A new survey of more than 400 IT security practitioners across North America and Europe reveals that 60 percent think COVID-induced remote work conditions have created data security issues within their organizations.
In addition the study, from encrypted USB drive company Apricorn, shows 38 percent say that data control during the pandemic has been very hard to manage. Surprisingly 20 percent of these security professionals admit that their work devices have been used by other members of their household.

Attacks on MSPs may lead to greater regulation
Managed service providers (MSPs) are a prime target for cybercriminals as they offer a gateway to the networks of the organizations that they manage, allowing attackers to go after many businesses from one place.
A new report from Perch Security looks at major MSP-related security events and trends from 2020 and makes predictions for 2021 with contributions from MSPs, partners, and security experts.

Businesses need greater understanding of cloud data security responsibility
There's been a major increase in cloud adoption because of COVID-19, but there's also widespread misconception surrounding responsibility for backup and recovery of data in the cloud and a lack of confidence in the security of data held by public cloud service providers.
A new report from Arcserve company StorageCraft shows 47 percent of respondents accelerated adoption of cloud services for data management, 59 percent confirmed increased use of cloud backup services, 56 percent increased the use of the cloud for IT infrastructure (IaaS), and 39 percent increasingly rely on cloud services for data recovery.

Nation state attacks increase 100 percent in three years
A new report shows that nation state cyberattacks are becoming more frequent, varied and open, moving us closer to a point of 'advanced cyberconflict' than at any time since the inception of the internet.
The report, sponsored by HP, is based on research conducted by Dr Mike McGuire, senior lecturer in criminology at the University of Surrey and finds that there's been a 100 percent rise in 'significant' nation state incidents between 2017 and 2020.
Guardicore microsegmentation extends zero trust to legacy platforms
Protecting legacy systems usually means segmenting them from points of compromise in the network. But the traditional approach using a legacy firewall for each machine is ineffective and costly.
Microsegmentation specialist Guardicore is announcing new capabilities for its Guardicore Centra product extending zero trust policies and granular microsegmentation to legacy systems including IBM iSeries AS/400 servers.

New AI-powered solution helps firms spot risky security behavior
Human error and poor security decisions are among the leading causes of data breaches, but it can be hard for security teams to know where to invest resources to address these risks and provide help to employees who need it most.
Tessian is introducing what it calls the Human Layer Risk Hub -- a solution that offers organizations full visibility into employees' risk levels and drivers on email, enabling security and risk management leaders to take a more tailored approach to employee security.
More than half of US employees write passwords on sticky notes
According to a new study, 57 percent of American employees are currently writing down work-related passwords on sticky notes, leading to significant cybersecurity risk.
In addition, the report from Keeper Security shows 66 percent have lost these sticky notes in the past, making it difficult to know who ultimately has access to sensitive company information.

Ransomware attacks and threats to IoT devices soar in 2020
Ransomware attacks grew by 485 percent in 2020 compared to 2019. Attacks in the first and second quarters accounting for 64 percent of all attacks or 19 percent higher than the first two quarters of 2019.
This is one of the findings of the latest Consumer Threat Landscape report from Bitdefender. which also shows that IoT devices with proprietary operating systems were responsible for 96 percent of vulnerabilities even though they account for only 34 percent of consumer devices.

When phishing phails to phool
Phishing attacks are getting more sophisticated and therefore harder to spot. However, there are still times when the phisherfolk don't do themselves any favors, making their attempts at deception amusingly obvious.
Email security company GreatHorn has launched a new blog series called Phishing Phails which looks at some of the less successful examples of phishing bait.
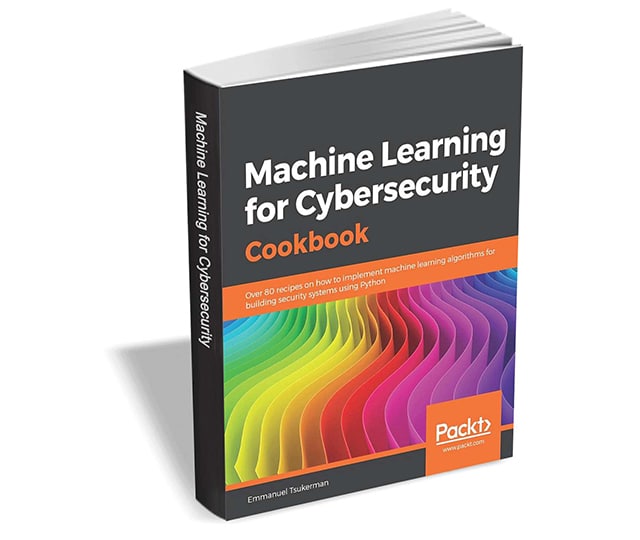
Get 'Machine Learning for Cybersecurity Cookbook' ($31.99 value) FREE for a limited time
Organizations today face a major threat in terms of cybersecurity, from malicious URLs to credential reuse, and having robust security systems can make all the difference.
With Machine Learning for Cybersecurity Cookbook you'll learn how to use Python libraries such as TensorFlow and scikit-learn to implement the latest artificial intelligence (AI) techniques and handle challenges faced by cybersecurity researchers.

Credential phishing on the rise with Office 365 a top target
New research from Menlo Security reveals that numbers of fake login pages and forms looking to steal credential are on the increase.
The majority of attacks are serving Outlook and Office 365 logins, reflecting the widespread use of these services across corporate environments.

Securing insurance's new attack surface with crowdsourced cybersecurity [Q&A]
All industries have been affected by the COVID-19 pandemic and the need to shift to new ways of working. This change has also led to an expanded attack surface for cyber criminals.
The insurance sector has been particularly hit in the past year and we spoke to Ashish Gupta, CEO of crowdsourced security company Bugcrowd to find out how businesses have been affected and how they're responding to the challenge.
