WhatsApp launches new tools to stop scammers
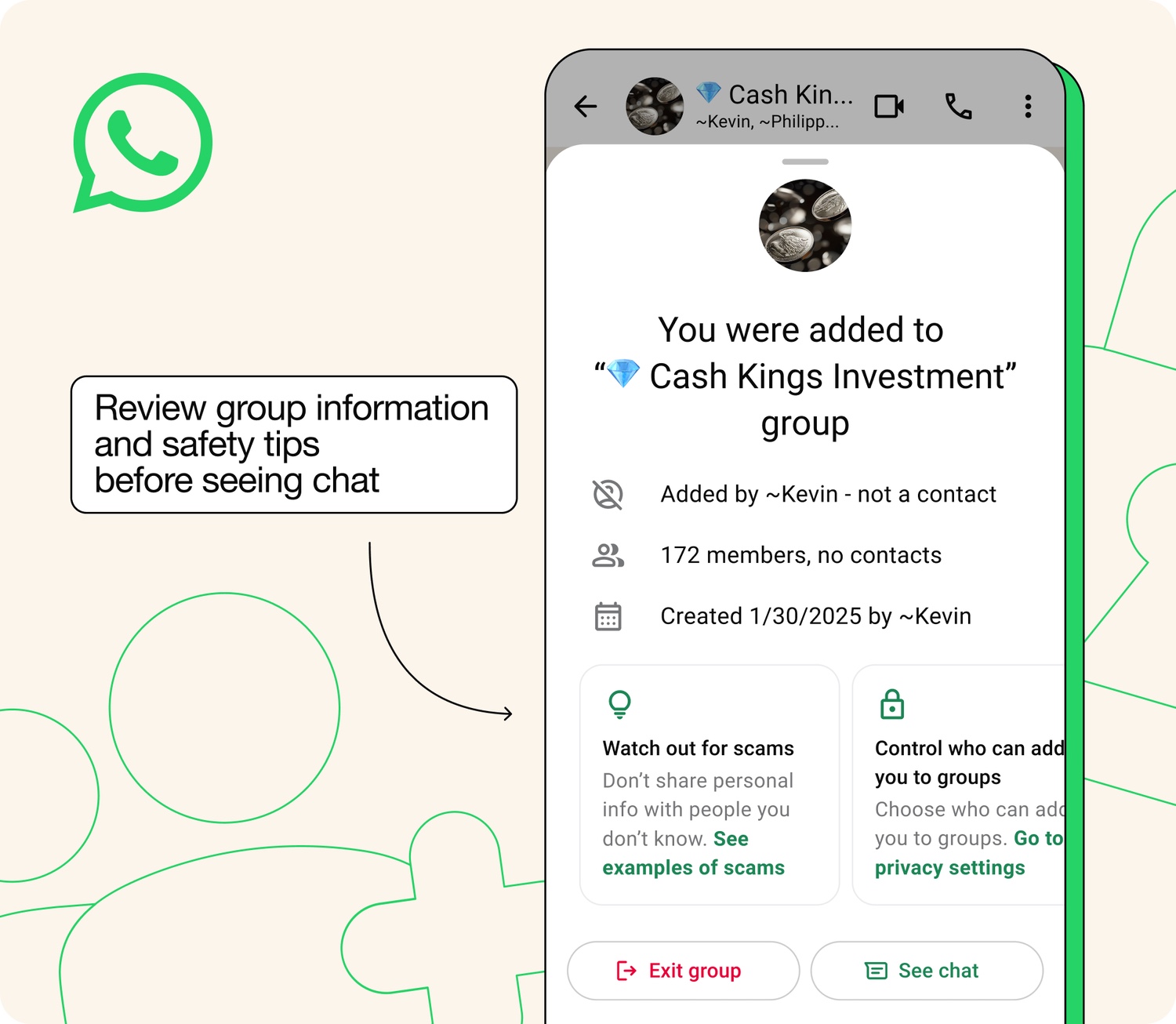
WhatsApp is now an essential communication tool for both personal and business use, and its popularity means that it is also a prime target for scammers. As such, the company has just announced the rollout of a new series of tools designed to help keep users informed and protected.
Among these new tools is a safety warning for group chats that warns about being added to new chat groups by unknown contacts. There are also tools and advice for individual chats, which are also targets for scams.
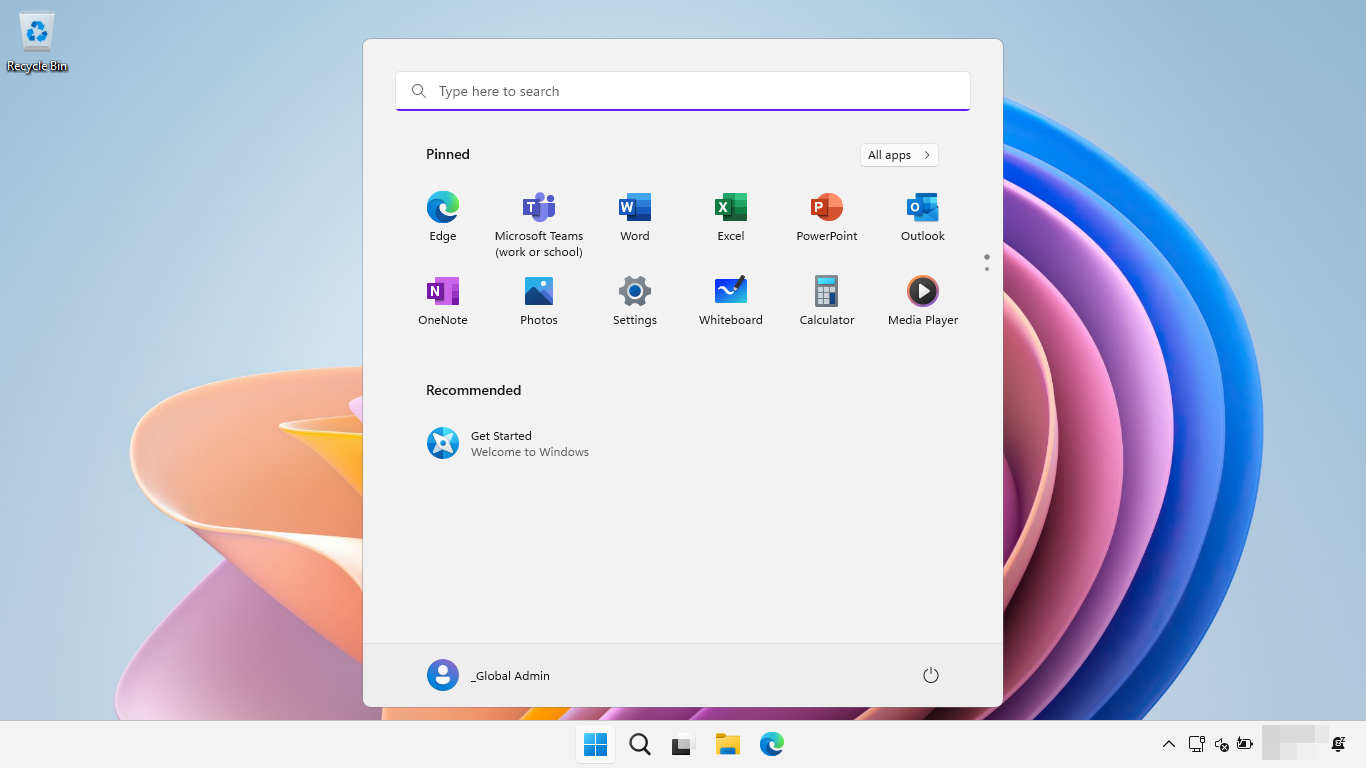
Microsoft Recall is bad at filtering sensitive information
Whenever there are privacy concerns voiced about software, they are almost always downplayed. But fears about Microsoft Recall appear to be well justified.
Announced and previewed last year, Microsoft Recall is a feature of Windows 11 which Microsoft says enables users to retrace their steps. It does this by capturing screenshots of computing activity, which can then be analyzed and searched using AI to home in on data, return to a project, and much more. But there have been lots of vocal protests about the potential for invasions of privacy.
Sudden Dropbox Passwords closure leaves users seeking alternatives
Dropbox has suddenly announced that it plans to discontinue its password manager, Dropbox Passwords. With the discontinuation coming at the end of October, users are left with very little time to find an alternative service.
The company is best known for its cloud storage service, and in announcing the impending shuttering of Dropbox Passwords it says that it wants “to focus on enhancing other features in our core product”. More than just closing down the password management side of things, Dropbox is also bringing dark web monitoring to an end.

Deception is evolving, and security teams need to catch up
Attackers are finding new ways to get inside company systems, and deception is playing a bigger role than ever, according to the latest LevelBlue Threat Trends Report.
Threat actors are leaning on tactics like social engineering and AI tools to move quickly, stay hidden, and then extend their reach once inside. Even experienced users can be tricked into opening the door without realizing until it's too late.

GregAI helps security teams fix real problems faster
Cybersecurity exposure management company Intruder has introduced GregAI, an AI-powered security analyst that, unlike generic AI assistants, has full visibility into each user’s security environment.
Currently in beta, GregAI is available to free trial users and customers on Intruder’s Cloud, Pro, and Enterprise plans. The assistant is named after Intruder’s original mascot, following a design file mix-up involving a designer named Greg.

Microsoft releases emergency fixes for actively exploited SharePoint security flaws
Microsoft has released emergency patches for two remote code execution vulnerabilities in SharePoint. The CVE-2025-53770 and CVE-2025-53771 security flaws are addressed by KB5002768 and KB5002754.
The issue was discovered by security researchers back in May, when it was found that the vulnerability allows for RCE attacks dubbed ToolShell. Microsoft had tried to plug the security holes earlier in the month with the July Security Update, but this only partly addressed the problem – hence the need for the emergency, out-of-band patches.

Matanbuchus 3.0 is a serious malware threat spread via Microsoft Teams
The Matanbuchus malware loader is not new – it has been around for at least 4 years – but it has evolved into something incredibly dangerous.
Matanbuchus 3.0 has been found targeting victims as part of a ransomware attack. Described as being “highly targeted”, the cyberattack campaign uses Microsoft Teams as a delivery method for the latest version of the malware loader. The highly sophisticated attack employs a Microsoft Teams call impersonating an IT helpdesk.

Microsoft to stop adding new features to Office apps for Windows 10 users
As we are being reminded on a near daily basis, Microsoft is ending support for Windows 10 in mid-October. The company has made it clear that the end of support means the end of security updates, but this does not mean that all Windows 10 users will take notice and jump to Windows 11.
However much Microsoft might wish otherwise, Windows 10 will remain in popular usage for some years to come – so the company is tightening the thumbscrews. A quiet announcement reveals that anyone sticking with Windows 10 will no longer receive feature updates for their Microsoft 365 (Office) apps.

In five seconds, this SSD will self-destruct: 5… 4… 3… 2…
When we think about storage, the primary concern is usually reliability – you need to know that the data you save remain safe and accessible. But there are plenty of other things to consider, and new offerings from TEAMGROUP takes a unique approach to security.
With the internal P250Q‑M80 NVMe SSD and the portable T‑Create Expert P35S external, there is not only military-grade AES-256 encryption to ensure data is not going to fall into the wrong hands, but also an uninterruptible self-destruct option. Push a red button on either of the devices and they can be wiped, or completely nuked – and nothing can stop the process.

Microsoft admits Windows Server Update Services sync is failing
Following complaints from users about problems with Windows Server Update Services, Microsoft has spoken out. The company has confirmed that WSUS has suffered issues preventing synchronization and deployment of updates.
This is a serious headache for businesses and organizations that rely on WSUS to manage Windows updates across networks. Reports of errors have been popping up for a couple of days, with scheduled synchronization actions showing to have failed in event logs.

Back to the office means back to basics on security
The shift to remote work was hastened by the Covid-19 pandemic, pushing companies to quickly adapt to employees working from home. Years later, remote and hybrid work remain common, offering a high degree of flexibility that many workers now take for granted.
Businesses have increasingly begun encouraging employees to return to the office, if only part-time. Leaders point to benefits like easier collaboration, improved team dynamics, and a clearer boundary between work and home life.
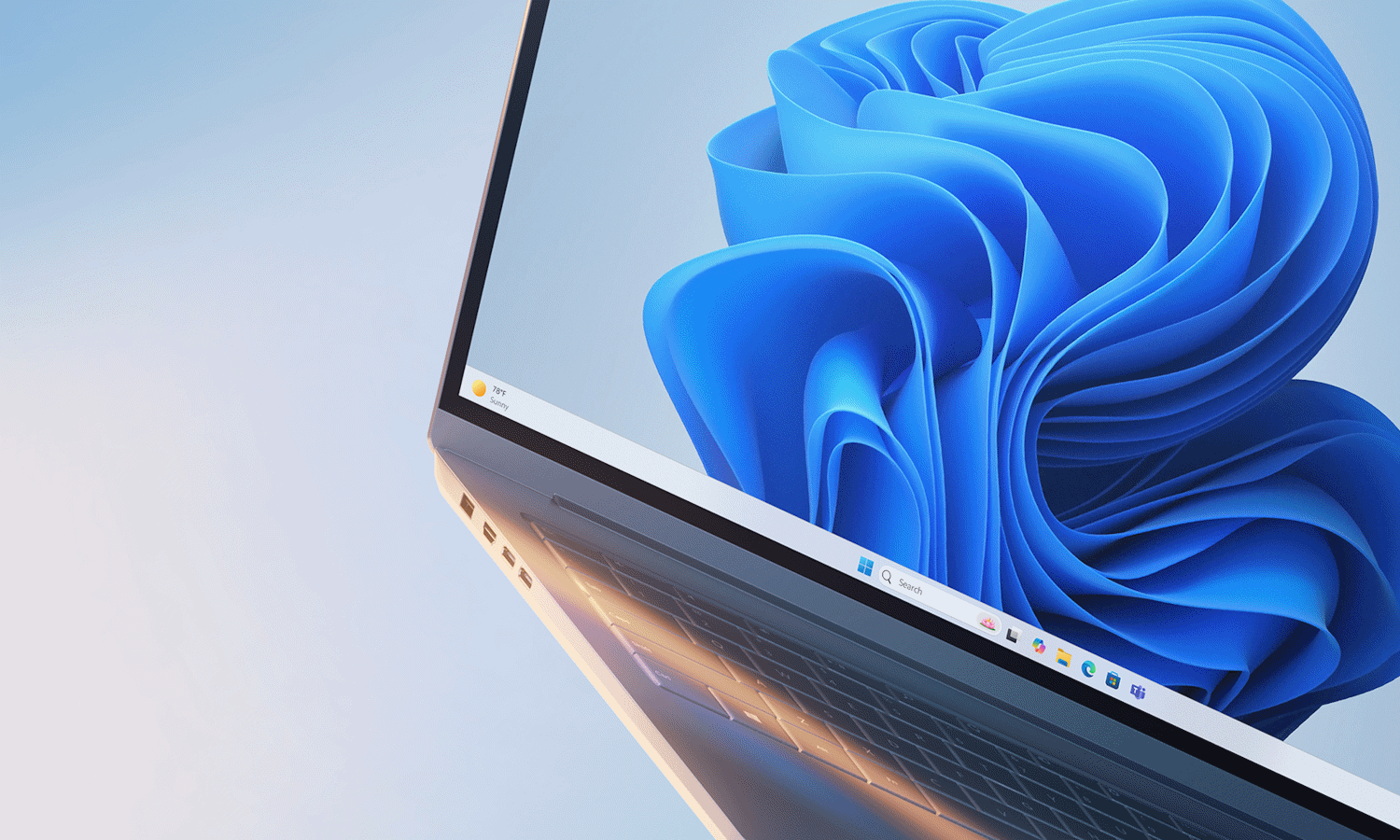
Microsoft adds features and boosts Windows 11 security with KB5062553
Microsoft has released the KB5062553 update for Windows 11 24H2. Billed primarily as a security update for the operating system, it is actually more than that – much more.
As is the case with Microsoft’s monthly security updates, it also includes the non-security improvements, fixes and additions that were previewed last month. One of the key new arrivals here is the new PC-to-PC migration experience which uses the Windows Backup app to ease the process of moving to a new computer.
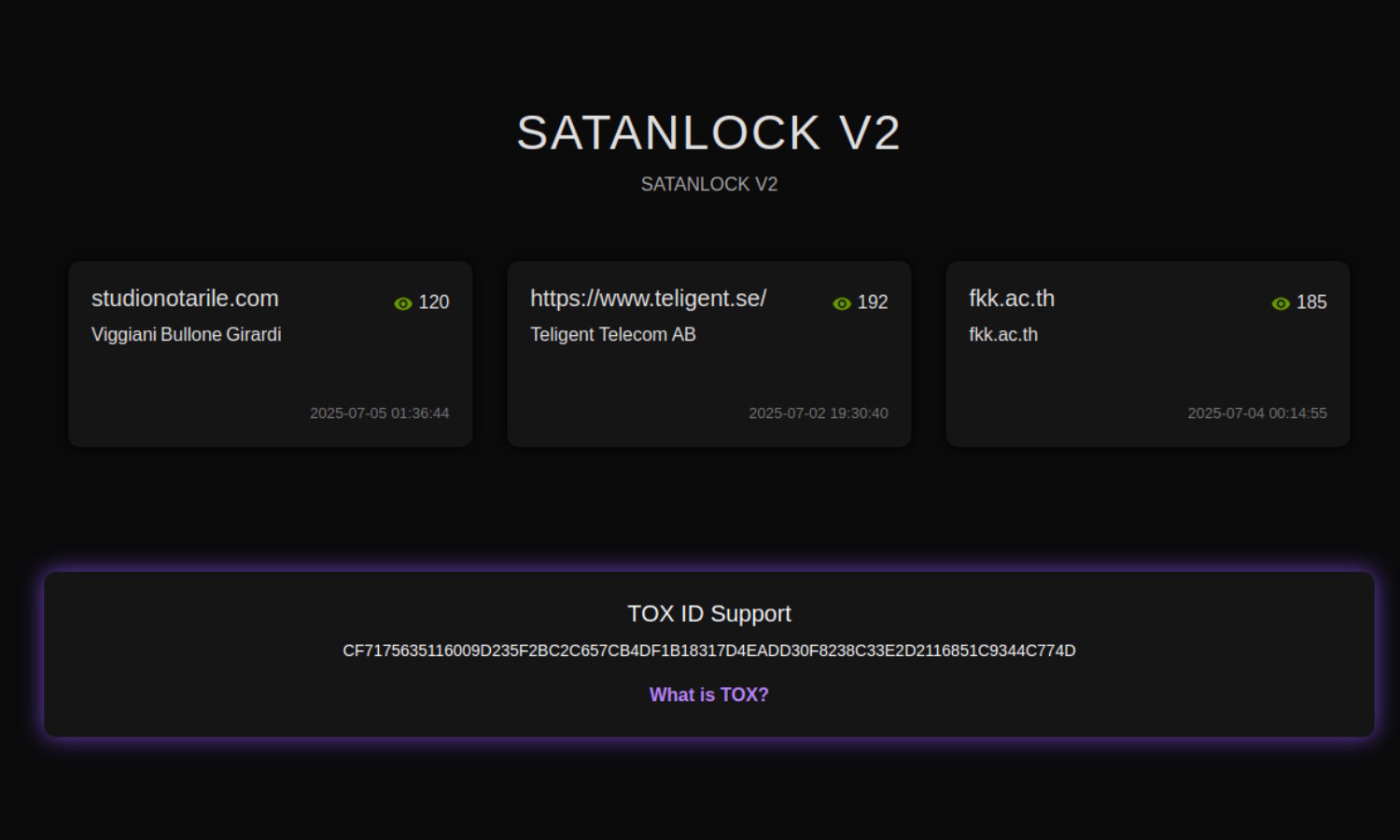
Short-lived ransomware group SatanLock to close down and leak data
There are large numbers of ransomware groups operating around the world, some of which have been conducting their nefarious work for years. There are older which are rather less long in the tooth, such as the recently formed SatanLock.
The group has been in existence for mere months, popping up in April this year. Responsible for a spate of attacks over a number of weeks, the ransomware group has announced that it is already shutting up shop. More than this, it plans to leak any data it has stolen.

Jack Dorsey’s latest project is the Bluetooth mesh network app bitchat
Jack Dorsey – the co-founder of Twitter and Block, and the founder of Bluesky – took to X to share some enticing details about the latest project he is working on.
Called bitchat, this is a messaging app that not only has security at its very core, but does not require internet access to work. A messaging app without internet? Dorsey explains that this is a secure, decentralized, peer-to-peer messaging app that works over Bluetooth mesh networks.

Microsoft confirms KB5060829 update for Windows 11 causes worrying Firewall errors
Microsoft has issued a warning about a recent update for Windows 11. The KB5060829 update was released late last month as a non-security preview update, and it has been found to be causing issues.
Available for Windows 11 24H2, the optional KB5060829 update has been causing Windows Firewall With Advanced Security errors to be logged by the operating system. While error message relating to a security feature are likely to result in concern and fear, Microsoft is at pains to reassure users that there is no need to panic.
