Monitoring and management of backups becomes more challenging

Monitoring of backups has long been a necessary chore for IT professionals, but a report out today shows that new issues are also impacting the category and creating greater challenges.
The study from Bocada, a company which specializes in the automation of backup reporting and monitoring, is based on a survey of over 260 IT professionals. Varied environments and growing data volumes are revealed as a major concern, with securing data across backup applications the most-cited backup management challenge, followed by protecting growing data volume.
Microsoft warns that KB5012170 update may cause 0x800f0922 error

Microsoft has issued a warning about the KB5012170 update, a security update for Secure Boot DBX released a few days ago.
The company says that users of Windows 11, Windows 10 and Windows Server may find that the update installation fails, resulting in a 0x800f0922 error. While there is currently no fix, Microsoft has issued some advice while it investigates the problem.
Microsoft launches Dev Box Preview to make life easier for developers

Microsoft has announced the availability of the public preview of Microsoft Dev Box. The service lets developers create cloud-based workstations whenever they are needed for projects, even when working out of the office.
The company describes the secure Azure-based service as "a managed service that enables developers to create on-demand, high-performance, secure, ready-to-code, project-specific workstations in the cloud".
Cloud hyperscalers get more involved in open source

Amazon, Microsoft, and Google are getting more employees involved in open source than ever before according to new analysis.
A study from Aiven of GitHub, the repository hosting service, finds the total number of active contributors to GitHub from Amazon, Microsoft, and Google has increased by 300 percent in six years -- from 2,654 contributors in May 2016 to 10,549 in May 2022.
The changing role of the CISO [Q&A]

The IT infrastructure of a modern enterprise is made up of a complex architecture of dynamic networks, cloud deployments, software applications, and endpoint devices.
Each of these has its own set of security controls, which form a critical part of the technology ecosystem, but managing these systems can hinder efficient threat detection and response, which in turn compromises visibility, allowing vulnerabilities and gaps to flourish.
Why data security is no longer optional

Security breaches cost more than just money. Investing in data security today prevents long-term negative consequences that cost your business time, money, and reputation. Acquiring threat intelligence data is a primary step in preventing cyberattacks, and web scraping is the method of choice for many modern data-driven businesses.
Business and personal activities are increasingly being digitized. Whether you are simply taking your temperature with a connected thermometer or sending products across complex supply chains, enterprises continuously collect data to improve services and refine operational processes.
Google Cloud and Google Workspace now support multiple SSO IdPs

Google has announced an expansion of its sign-in options. The company is opening up google Workspace, Google Cloud and BeyondCorp Enterprise so users can take advantage of single sign-on (SSO) from multiple third-party identity providers.
Google has long-supported SSO using the SAML protocol from a single identity provider (IdP), but the company recognizes that times are changing. Support for multiple SAML-based identity providers instead of just one is something that will benefit many customers.
Your current cybersecurity approach creates systemic vulnerabilities

Verizon recently released its 2022 Data Breach Investigations Report, giving businesses vital insights into the state of cybersecurity around the world. Containing an analysis of over 23,000 incidents and 5,200 confirmed breaches over 15 years, Verizon attributes the number-one motive of cyberattacks to financial gain. Almost four out of five breaches were attributable to organized crime seeking to extort businesses of hefty ransomware sums, backed by insurance pay-out.
Verizon has also estimated that there has been a 13 percent increase in ransomware breaches -- this is more than in the last 5 years combined. Additionally, 82 percent of cyber breaches involved a human element, namely through stolen credentials, phishing, misuse or simply an error.
Is risk-aversion holding back cloud maturity?

As we all know by now, the "cloud" is not just another "IT thing" that only IT people should care about. This is because every organization that has understood this principle has triumphed. Unfortunately, a significantly higher number have merely paid lip service to this idea. To them, the cloud is just another IT thing. The cloud enables a pace of change that companies of the past could have only ever dreamed of. Instead of waiting 6 months to deploy a new app, you can have the idea in the morning and have it deployed company-wide by the afternoon.
At least that’s the theory. But how many of us have seen this happen in reality? The problem is not a technical one. Most organizations could work at this "cloud pace," but most don’t. They might have the technology, leadership support, budget etc. to operate at this "same day" pace, but they don’t. Why not?
Will Microsoft never learn? The company hits paid-up Office 2021 users with ads for Microsoft 365

There are various business models for software these days, ranging from simple purchases to subscriptions. There are also freemium apps and games that are cost-free but feature advertising. If you have spent money on software, you might rightly expect it to be free from ads, but not in the case of Microsoft Office 2021.
Microsoft is certainly no stranger to using its products -- such as Windows 11 -- as platforms to advertise other products and services. Office 2021 is just the latest example, with Microsoft using the software -- for which users have paid a one-off fee -- to advertise the subscription-based its Microsoft 365 products.
Why security training is key to improving cybersecurity posture

The threat landscape is constantly evolving and the shift to hybrid has only widened the attack surface. Today, organizations continue to be in the firing line as cybercriminals exploit their most used application: emails. The proliferation of phishing and business email attacks have seen hackers targeting the biggest corporate security weakness; employees.
Threat actors target workers because they are seen as the weakest link. Cybercriminals are thriving by targeting and exploiting staff, especially those who haven’t received effective user education and training. As the attack surface expands and threats become more sophisticated, organizations must reinvent the wheel by changing their approach to cybersecurity. Where should they start? With training employees and providing omnipresent tools and technology to prevent, detect, and recover from even the most sophisticated of attacks.
Flying high: Could drones help address the delivery crisis?

The UK has been experiencing a shortage of delivery drivers in recent years. So much so, Amazon enticed part-time workers with up to £3,000 in incentives to ensure this didn’t affect profits during the festive period.
As well as this, according to the Road Haulage Association, the industry was short of more than 100,000 HGV drivers in June 2021. This was due to a number of factors, from barriers to obtaining a license to the introduction of Brexit.
What you need to know about prototype pollution and how it affects JavaScript

No, this is not about solid waste generated with the production of prototypes or models for different products. Prototype pollution here refers to a critical cyber threat rated 10/10 on the CVSS scale of severity.
In a paper published in July this year, entitled "Silent Spring: Prototype Pollution Leads to Remote Code Execution in Node.js," security researchers revealed a serious vulnerability that affects prototype-based languages like JavaScript and the Node.js platform. This threat involves injecting properties into an object's root prototype at runtime and causes the execution of legit code gadgets.
Attacks on healthcare organizations increase 90 percent

There has been a 90 percent increase in the number of healthcare organizations targeted by cyber-attacks, in comparison with the first quarter of 2022.
The latest cyber threat Landscape report from Kroll finds that while phishing continues to be the vector used for initial access, there has been a vast increase in external remote services (such as VPNs and RDP environments) being compromised, up 700 percent.
Microsoft is launching a new PowerToys utility -- Screen Ruler
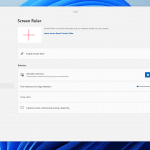
The last few PowerToys updates have been slightly disappointing (but only slightly) in as much as they have been largely bug-fixing releases, and have not included any new toys to play with. This is about to change.
Microsoft has a new utility in the pipeline, and its name gives you a very good idea of what it does: Screen Ruler. Perfect for all sorts of design work, the tool will let you measure the distance between two points on your screen in a number of ways.
Most Commented Stories
© 1998-2024 BetaNews, Inc. All Rights Reserved. Privacy Policy - Cookie Policy.




