
Small and medium enterprises more likely to adopt cyber insurance
Smaller and medium sized companies are more likely to spend on cyber insurance than their larger competitors according to a new report.
The study from US cyber insurance specialist Cowbell Cyber finds 65 percent of SMEs are planning to spend more on cyber insurance as part of their resilience plan in the next two years, compared to 58 percent of large companies.

AttackIQ offers free cybersecurity training to boost 'threat-informed defense'
Breach and attack simulation solutions company AttackIQ is offering advanced cybersecurity training with a modularized curriculum and cyber range labs to security practitioners, free of charge.
Learners at the AttackIQ Academy get realistic, hands-on experience via cyber range labs and exercises that are based on scalable, cloud-hosted infrastructure. All Academy participants are eligible for (ISC)2 Continuing Professional Education (CPE) credits.

Open services leave business networks exposed
As cloud environments become more and more common the extra risks are mostly well understood but a new blog from Orca Security shows that businesses could be leaving their networks open via common configuration errors.
The use of external CI/CD (continuous integration/continuous delivery) services means access control lists (ACLs) are often changed but this can inadvertently leave internal services open to the world argues Avi Shua, CEO and co-founder of Orca Security.

Business email compromise attacks spike in March
In yet another sign that cybercriminals are keen to exploit the current world situation, in the second and third weeks of March business email compromise (BEC) attacks increased more than 430 percent according to email security specialist Abnormal Security.
In the early part of the year attacks on C-Suite executives decreased by 37 percent from Q4 2019 to Q1 2020, while the focus shifted to finance employees, attacks targeting them increasing 87 percent in Q1 2020 against Q4 2019.
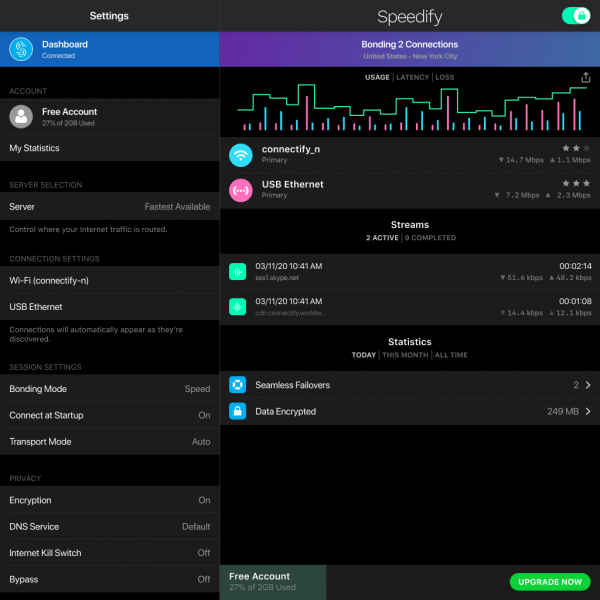
Speedify delivers more reliable VPN connection for remote workers
The increase in remote and home working in recent months has shone a spotlight on the unreliability of many domestic internet connections.
The Speedify VPN service is updating its offering which allows users to link and seamlessly switch between multiple connections including home internet, mobile data and public Wi-Fi networks to provide a more reliable connection.

Half of security professionals had no plan for a pandemic scenario
New research from Bitdefender shows that half of information security professionals didn't have a contingency plan in place -- or didn't know if they did -- for a situation like COVID-19 or similar.
Yet 86 percent admit that attacks in the most common vectors have been rising during this period. Cyberwarfare and IoT as an attack vector were reported to be up by 38 percent, and APTs, cyberespionage IP theft and social media threats/chatbots by 37 percent -- all of which could turn 2020 into a bumper year for breaches.

Dark web tools spotlight dangers of poor password management
Tools like checkers and brute forcers freely available on the dark web are helping unskilled criminals launch automated attacks against organizations' websites.
A new report by Recorded Future also reveals the industries most affected by these tools are software, media and entertainment, eCommerce, finance, and telecommunications.

Security teams overconfident about detecting cyberthreats
A new report shows that 82 percent of security operations centers are confident in their ability to detect cyberthreats.
This is despite just 22 percent of front line workers tracking mean time to detection (MTTD), which helps determine hacker dwell time, and 40 percent of organizations still struggling with SOC staff shortages and finding qualified people.

New identity tool helps combat digital fraud
Spotting potentially fraudulent customers and transactions is difficult. But a new tool from identity verification firm Ekata uses machine learning to help identify good and bad customers.
Network Score uses the Ekata Identity Network, a proprietary global dataset of billions of customer transactions, to reduce the number of false transaction declines and increase the precision of fraud detection.

Over reliance on passwords compromises security
Four out of ten IT security professionals still see usernames and passwords as one of the most effective means to protect access to their IT infrastructure, even though most hacking-related breaches are a result of weak, stolen or reused credentials.
A new report on access management from Thales also reveals that a majority of respondents say their organization plans to expand the use of usernames and passwords, even though the limitations could pose security challenges.

Arlo Essential Spotlight Camera is affordable and chock-full of cool features
If you are a homeowner in 2020, you should have an outdoor smart security camera -- it simply isn't up for debate. Not only are they more affordable than ever, but they are very simple to set up. Many models don't even requires cables or a hub, allowing you to mount it anywhere within your Wi-Fi's range. You can then monitor the outside of your home to detect potential burglars or just keep an eye on your children playing in the yard. There really is no excuse to not have one.
Today, Arlo unveils its latest outdoor smart security camera and it is shockingly affordable. Called "Essential," the 1080p camera is powered by a rechargeable battery and doesn't require a hub, so you can place it anywhere without having to deal with running cables for power. It even has color night-vision and two-way audio. Not to mention, it is sleek and attractive, so it won't look ugly hanging off the side of your house.

Protecting IoT and OT with zero trust and network segmentation [Q&A]
In recent years we've seen a surge in the numbers of IoT and operational technology devices appearing on networks.
But while this technology offers many advantages it also brings new risks, both for the devices themselves and the networks they're attached to. What can businesses do to benefit from the technology but still keep their networks safe?

Security industry responds to FBI warning of increased mobile banking risks
Earlier this week the FBI issued an alert about the risk of mobile banking platforms being targeted by cybercriminals during the current pandemic lockdown.
More than 75 percent of Americans used mobile banking in some form in 2019, but since the start of this year, a 50-percent spike in the usage of banking apps has been observed. Security professionals have been responding to the news.

New platform helps prevent data loss when employees leave
Around a third of employees take data with them when they leave a business according to email security firm Tessian.
In order to help companies understand and tackle the risks it's launching a new Human Layer Security (HLS) Intelligence platform to provide businesses with deeper insights into human layer security threats and the tools required to trend down the risk of accidental data loss, data exfiltration and advanced impersonation phishing attacks.
How hackers are targeting enterprises from the outside
In the past businesses have needed to worry about protecting their networks. But the expansion of internet use, cloud and as-a-service products means there are now more potential threats to worry about.
A new study from attack surface management specialist RiskIQ looks at the digital presence of organizations, where they lack visibility, and the pathways hackers are using to exploit these blind spots.
