
Taxpayers worry about online fraud but offline habits could be putting them at risk
As we approach the tax return season, a survey from document destruction and information security company Shred-It reveals that 38 percent of US taxpayers say they are worried they will become a victim of tax fraud or tax identity theft.
Yet according to the study 45 percent admit to storing tax paperwork in a box, desk drawer or unlocked cabinet at home or work. What's more, 19 percent admit they don't shred tax paperwork or physical documents containing sensitive information before throwing them away.

85 percent of organizations don't meet basic levels of PAM security
While 78 percent of organizations now include privileged credential protection as part of their cyber security policies, their privileged access management (PAM) security practices are still lacking.
According to a new study by PAM specialist Thycotic, 85 percent of respondents are still struggling to get beyond the initial phase of PAM maturity.

Cloudflare announces free VPN service, Warp, to complement its 1.1.1.1 DNS resolver
Online privacy has become such a concern that VPN tools -- once used only by technology experts -- have now started to become far more mainstream. Android users can take advantage of Opera's built-in VPN, and there are many other services to choose from.
Adding to this list, Cloudflare has announced a new free VPN service called Warp. It will become part of the company's existing privacy-focused 1.1.1.1 DNS resolver, and just as 1.1.1.1 was designed to simplify using a DNS tool, so Warp is being billed as a "VPN for people who don't know what V.P.N. stands for".

Attackers target supply chains using 'island hopping'
Around half of recent cyberattacks use 'island hopping' techniques, seeking to target not just one network but those along the supply chain too.
This is one of the findings of the latest Global Incident Response Threat Report from Carbon Black. It also finds that 70 percent of attacks now attempt to move laterally around the network.
Vulnerabilities leave financial mobile apps open to attack
A new report reveals widespread security inadequacies and protection failures among consumer financial applications.
The research for Arxan Technologies, carried out by Aite Group, says these vulnerabilities can lead to the exposure of source code, sensitive data stored in apps, access to back-end servers via APIs, and more.

IoT attacks increase but rely on the same old weaknesses
Internet of Things devices have proved to be problematic in their vulnerability to cyber attacks. This is underlined by a new report from F-Secure which finds that threats and the number of attacks continue to increase, but still depend on well-known security weaknesses, such as unpatched software and weak passwords.
The number of IoT threats observed by F-Secure Labs doubled in 2018, growing from 19 to 38 in the space of a single year.
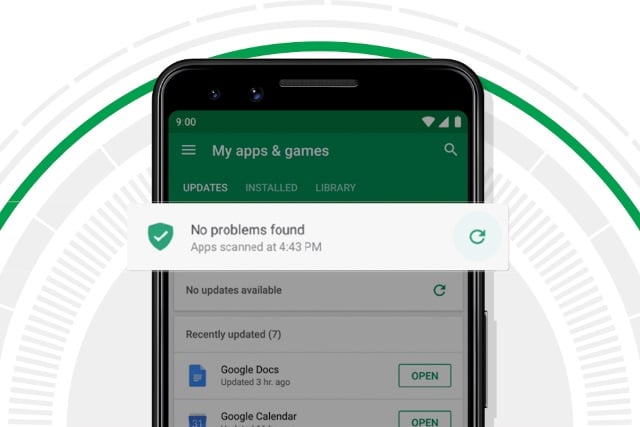
Google publishes its Android Security & Privacy 2018 Year in Review
Google has published its fifth Android Security & Privacy Year in Review, this time looking back at 2018. While the report draws attention to some of the security and privacy improvements the company has made, it is not just about Google blowing its own trumpet.
The report shows that payouts made through Google rewards programs -- payments made to outside researchers and individuals for bringing security issues to the company's attention -- reached $3 million in 2018. Google also says that in the fourth quarter of the year, 84 percent more devices received a security update than in the same quarter in 2017.

Continuous response needed to combat cyber attacks
As the threat landscape continues to rapidly evolve, businesses need to be able to react quickly and have an effective strategy to deal with attacks.
Security specialist F-Secure is calling for greater emphasis on both preparing for a breach as well as fast and effective containment that has the correct balance of people, process and technology.

90 percent of tech companies are vulnerable to email spoofing
Phishing is a major problem for large organizations, but while there are standards to authenticate email and prevent phishers from spoofing domains with fake emails, a majority of companies have not made full use of them.
The tech sector has moved faster than some but while they are beginning to implement protection many companies in this sector are still at an early stage with the result that 90 percent are still vulnerable to impersonation.

Russia orders NordVPN, ExpressVPN, HideMyAss and other VPNs to block numerous sites
VPNs are frequently used by people to increase security, improve privacy, to browse the internet as if in another country, and to bypass restrictions put in place by ISPs and governments. Aware of this, authorities in Russia have ordered ten big-name VPNs to block access to various sites banned in the country.
Among those to have been contacted by the authorities are NordVPN, ExpressVPN, IPVanish, HideMyAss and TorGuard. At least one of these VPN providers has decided to pull out of Russia.

UK watchdog says Huawei poses a national security risk
In its fifth annual report, the UK's Huawei oversight board says that the Chinese firm poses a threat to national security. It reached the conclusion after discovering that the company has made "no material progress" in addressing the security flaws highlighted in last year's report.
But while the report was damning of Huawei, saying it found additional "significant technical issues in Huawei’s engineering processes leading to new risks in the UK telecommunications networks", the board stopped short of calling for a ban on Huawei's involvement in 5G in the UK.

Large enterprises face problems with unsecured applications
A new survey of more than 200 CISOs in the US and Canada finds that large enterprises typically operate 1,300 or more complex applications but only protect 60 percent of them, leaving more than 500 applications unprotected at a time where adversarial attacks are increasing.
The study from crowdsourced security company Bugcrowd along with the Enterprise Strategy Group (ESG), also shows strong interest in using DevOps to automate security.

Encryption backdoors raise the likelihood of attack
Countries with government-mandated encryption backdoors are more susceptible to nation-state attacks according to 73 percent of security professionals.
A survey from machine identity protection company Venafi also finds 69 percent believe countries with encryption backdoors suffer economic disadvantages in the global marketplace as a result.

Data breaches more common than rain in the UK
The UK has something of a reputation for its wet climate, and its citizens for constantly talking about the weather. So it may come as a surprise to find that in the UK the chance of experiencing a data breach is higher than that of encountering a rainy day.
A survey by technology services company Probrand shows 43 percent of UK businesses having suffered a cyber breach or attack in the last 12 months as against just 36.4 percent chance on average of encountering a wet day.

Almost half of industrial computers hit by malicious cyber activity in 2018
Kaspersky has released the results of an astonishing study that found that almost half of world's Industrial Control System (ICS) computers was subjected to malicious cyber activity last year.
While malware and cyber attacks have been a problem for some time, there is particular concern about the rising numbers of ICS computers being affected. In the case of downtime for such systems, there is the risk of material losses and production downtime at industrial facilities.
