
Lessons the military can bring to cybersecurity [Q&A]
The ongoing struggle between good and bad actors in the cyber world has often been compared to a battle or warfare. More recently the threat of nation state attacks on critical infrastructure has led to more actual military interest in the cyber arena, as we've seen in Ukraine.
The Israel Defense Force's 8200 unit is often referred to the SEALs or SAS of cyber military units and its veterans are driving many of Israel's tech start ups.

Microsoft won't give you any more security updates if you don't upgrade Windows 10 version 20H2 in the next month
Microsoft is putting the squeeze on anyone who is hanging doggedly on to an old version of Windows.
The company is ending support for Windows 10 version 20H2 in just a few short weeks, meaning that anyone who fails to upgrade will no longer receive security updates. Microsoft would, of course, like users to upgrade to Windows 11, but this is not the only option.

70 percent of organizations use a vulnerability assessment tool
A new study from Netwrix reveals that 70 percent of organizations use a vulnerability assessment tool, but not always for the reasons you might think.
Rather than to ensure compliance, 70 percent say the primary reason for purchasing the tool is the need for proactive security measures. In addition 76 percent of those who don't yet own a vulnerability assessment tool and plan to acquire one in the near future for the same reason.

Windows 11's upcoming Smart App Control security feature has a major issue
At its Windows Powers the Future of Hybrid Work event earlier this week, Microsoft revealed various new features that are coming to Windows 11. As well as additions such as tabs in File Explorer and folders in the Start menu, the company revealed a lot of upcoming security features.
One of the security highlights is Smart App Control, which works like an enhanced version of the SmartScreen filter already found in Windows. It will help to block malicious apps, but there is a serious downside that will put off a lot of people.

Why data-centric security is now a top priority for every business
In today’s business environment, data is one of the most valuable assets any organization owns. Consequently, a great deal of time and money is spent trying to ensure that the most effective data security measures are in place to protect it. But with so many options available, knowing which approach to take is becoming increasingly difficult.
Escalating cybercrime, the adoption of cloud computing, an explosion in mobile device usage, and varying technology and applications means there’s so much to consider. No matter the industry, a data security breach is now an increasingly likely scenario that all businesses could face. Security teams should therefore consider a strategy that is focused on protecting actual data throughout its entire lifecycle, rather than just focusing on the infrastructure around it.

Half of cybersecurity professionals consider quitting due to pressure
New research from Vectra AI shows 94 percent of IT security leaders have felt increased pressure to keep their company safe from cyberattacks in the past year, while half say they feel burned out and ready to quit.
The survey of 200 UK IT security decision-makers finds 51 percent of respondents have experienced negative emotions such as depression, anger, or anxiety due to feeling overwhelmed by work.

Talent shortages leave businesses more exposed to attacks
Whether it's down to the Great Resignation or a lack of the correct skills, security and development teams are struggling to find and retain enough skilled staff.
A new study released today by cybersecurity company Cobalt finds that 45 percent of security respondents say their department is currently experiencing a shortage of employees.

New malware targets AWS Lambda cloud environment
The latest research from Cado Security reveals the first publicly known malware that is specifically designed to execute in the AWS Lambda serverless environment.
Named Denonia, the malware downloads and runs crypto mining software, and demonstrates how attackers are exploiting newer cloud computing use cases to take advantage of their ephemeral nature to evade detection.
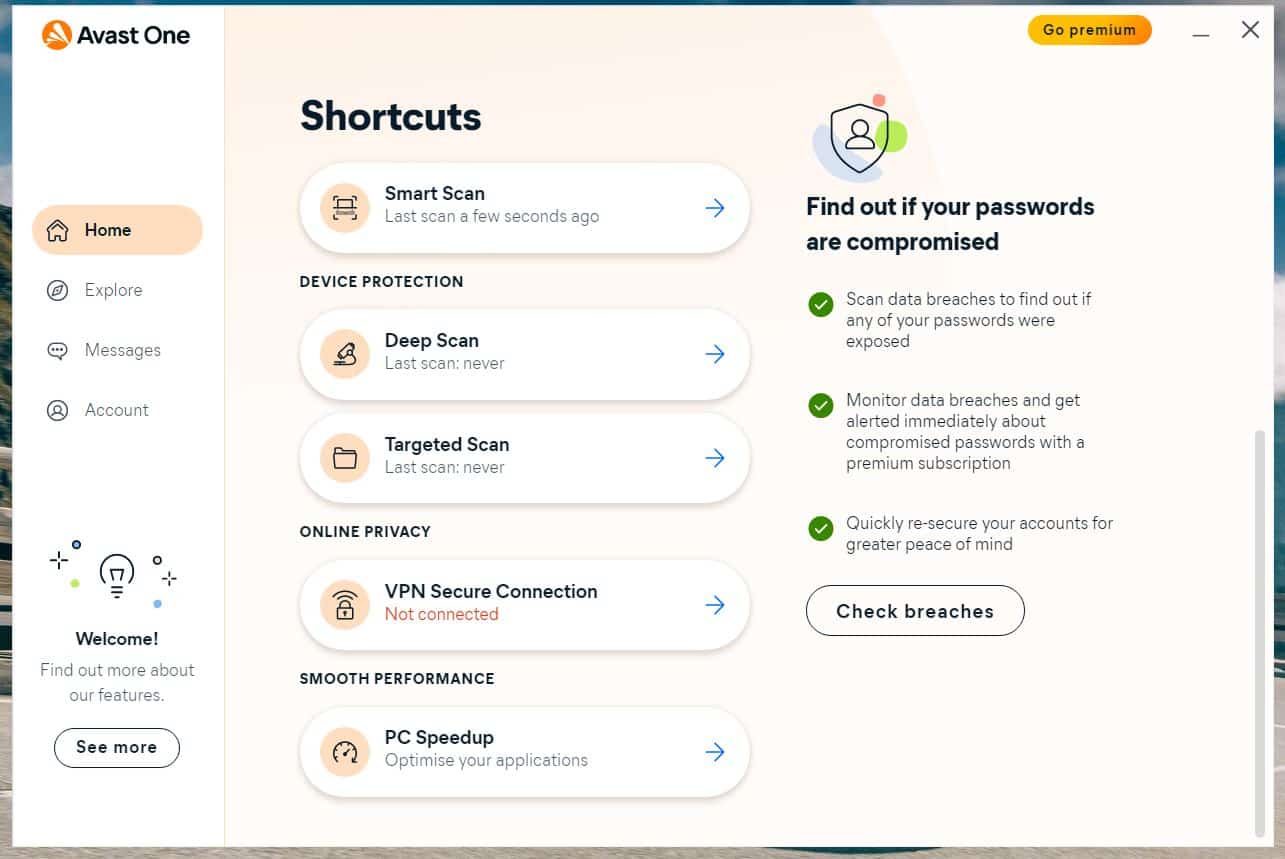
Avast One receives a major makeover to improve protection
Launched last year, Avast One aimed to offer a comprehensive protection suite with both free and paid for editions.
The company has now announced significant enhancements to the product, with new features designed to protect people from online scams, fraud, and other personal privacy threats.

Employees not fully prepared for cyberattacks say IT leaders
Over half (56 percent) of IT security leaders say that their non-technical staff are only 'somewhat' or 'not at all' prepared, for a cyberattack.
A new survey by Egress of 600 IT security leaders also shows that 77 percent of respondents have seen an increase in security compromises since going remote twp years ago, and there's a continued significant risk to organizations.

Financial fraud attempts up over 200 percent in two years
A new study into financial fraud from Feedzai finds that fraud attempts globally are up by 233 percent over the last two years.
Over the same period there has also been a whopping 794 percent increase in fraud on digital entertainment transactions. The effects of the pandemic are evident too with a 65 percent increase in online transactions and a 75 percent drop in US cash withdrawals.

94 percent of critical assets can be compromised within four steps of a breach
A new study from Israel-based XM Cyber, based on findings from nearly two million endpoints, files, folders and cloud resources throughout 2021, shows 94 percent of critical assets can be compromised within just four steps of the initial breach point.
The research team analyzed the methods, attack paths and impacts of attack techniques that imperil critical assets across on-premise, multi-cloud and hybrid environments, and developed tips for thwarting them.

New endpoint solution reduces risk and streamlines patching
A new multi-vector endpoint detection and response (EDR) solution from Qualys aims to reduce the risk of compromise with vulnerability management and patching all from a single agent.
Traditional EDR solutions still focus solely on endpoint activity to detect attacks and incorporate only MITRE ATT&CK techniques -- not tactics. This means security teams are forced to rely on additional tools to strengthen their risk management.

Two-thirds of ransomware victims paid up last year
A record 71 percent of organizations were impacted by successful ransomware attacks last year, according to the 2022 Cyberthreat Defense Report (CDR) from CyberEdge Group, up from 55 percent in 2017.
Of those that fell victim, almost two-thirds (63 percent) paid the requested ransom, up from 39 percent in 2017.

Microsoft boosts the security of Windows Update downloads
It has been a very long time coming, but Microsoft appears to have finally understood the value and importance of HTTPS. For reasons best known to the company, anyone looking to download updates from the Microsoft Update Catalog have had to do so via HTTP links -- but no longer.
In the last few days, Microsoft made a server-side change that means Microsoft Update Catalog downloads now use HTTPS connections. The switch to HTTPS affects everything from Windows 11 to Office, and everything in between.
