
Vivaldi introduces scheduled themes and individually sized Web panels
Vivaldi Technologies has unveiled Vivaldi 1.4 FINAL and Vivaldi 1.4 FINAL 64-bit, a major update to its web browser aimed at those wanting maximum control over their browser’s look and functionality. Vivaldi is developed by a team led by Opera co-founder Jon S von Tetzchner, and runs on Windows, Mac and Linux.
Version 1.4’s headline new feature is support for scheduled themes, which builds on the recent introduction of customizable themes. Other notable changes include greater flexibility over Web panels, and a single-click option for reversing an accidentally closed tab.

Apple bumps up the iPad's storage, drops Pro prices
Apple yesterday unveiled new iPhones and the Apple Watch Series 2, but did not announce any changes related to the iPad line. Some folks expected it to unveil new models, but the company had other things in mind for its popular tablets.
One of the main changes that Apple introduced with the iPhone 7 and iPhone 7 Plus is the bump in base storage to 32GB, up from the 16GB that previous models shipped with at the entry level. That is a change that Apple has quietly applied to the iPad line too, along with a drop in price for the Pro models.

Pilot-as-a-Service platform connects enterprises to software vendors
While companies are often keen to have their own custom built applications, the process of coming up with a proof of concept and selecting a developer can be complex and time consuming.
Israel-based prooV wants to make the process easier with the world's first Pilot-as-a-Service platform that seamlessly connects enterprises to independent software vendors.

Few business leaders understand their digital strategy
Despite the pressure modern organizations face to embrace new technologies and adopt digital processes, only four percent of business leaders completely understand their company's digital business strategy.
That's one of the main findings from a new Forrester report looking at "business and technology leadership in a post-digital era", commissioned by Huawei and launched last week at Huawei Connect 2016 in Shanghai.

Dropbox and BitTitan team up to ease cloud migration
Migrating to the cloud can be a complex and time consuming process. In order to help things go more smoothly, services automation provider BitTitan has formed an alliance with Dropbox to simplify and accelerate the process of data migration into Dropbox Business.
The link up provides BitTitan partners to create new services revenue around another leading cloud product. In turn, Dropbox resellers have free access to all of the tools and resources in BitTitan MSPComplete, a comprehensive cloud services enabling platform, including its sales automation capabilities.

Reshade Image Enlarger: a smarter way to resize images?
Resizing digital images is easy, but take the upscaling too far and quality begins to suffer with blurring, jagged edges and more.
Reshade Image Enlarger claims to help by using "state of the art… enlargement algorithms to produce crisp-clear resizes" without the "usual blur, jagged edges, loss of sharpness or detail".
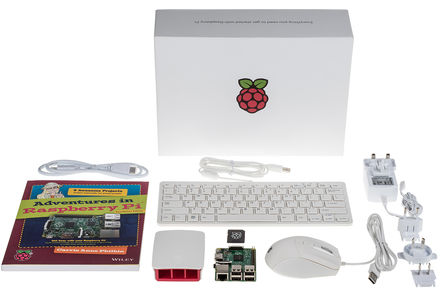
Raspberry Pi celebrates 10 million sales by launching an official Starter Kit
Raspberry Pi has been an incredible success. Originally aimed at schools, the credit card sized bare-bones computer has found an appreciative audience outside of the education system, and in just four and a half years sold a whopping 10 million.
I chatted with Liz Upton, Head of Communications at Raspberry Pi Foundation (and wife of the foundation’s Executive Director Eben), when they’d sold their first million devices, and things have certainly moved on a lot since then with the introduction of new models, and the $5 Pi Zero.

Industry analysts question whether Apple has made mistakes with the iPhone 7
The event is over. The dust has settled. We now know everything there is to know about the iPhone 7 and iPhone 7 Plus. Despite all of the new features and cosmetic changes that Apple implemented in its latest smartphone, the focus after the announcement has been very much on the 'courageous' decision to ditch the headphone socket.
Some view this -- as Apple does -- as a move that took courage; others see it as a cynical marketing move that simply opens up yet another line of revenue. But this is not the only change to the iPhone 7 that has raised eyebrows. Many industry experts are questioning other decisions made by Apple. One such person is Richard Stiennon, Chief Strategy Officer at Blancco Technology Group.

Android's September security update patches Quadrooter flaws
Google has released a new Android security fix that deals with the final two flaws in the Quadrooter set of vulnerabilities that was discovered last month.
Quadrooter refers to four undiscovered security vulnerabilities found in Android phones and tablets containing Qualcomm chips. These vulnerabilities are particularly troubling as they were found on every version of Android and affected at least 900 million devices.

Dario Health unveils Lightning connector diabetic glucose meter for iPhone 7
People with diabetes have to check their blood sugar often. Not only do they have to worry about high glucose levels, but low levels too. Having blood glucose outside of normal levels can cause long term health risks, but in the short term, it can cause symptoms like dizziness and confusion too.
Unfortunately, many glucose meters are fairly low-tech -- a far cry from modern devices. Luckily, there are newer meters that can connect to smartphones for improved blood sugar tracking. Dario Health offers an iPhone compatible model that leverages the headphone jack. The problem? Apple killed that port today. If you are upgrading to the iPhone 7, do not panic. Today, Dario Health announces a new meter that utilizes the Lightning connector.

Sony announces PlayStation 4 Pro and slimmer 'standard' PS4
Can you believe it is almost four years since the PlayStation 4 was initially announced? Since then, the video game console landscape has been wild. Nintendo totally dropped the ball with the Wii U, while Microsoft has been giving Sony consistent competition with its Xbox One. Actually, the Windows-maker recently released a more svelte version if its console, making the PlayStation 4 look a bit dated.
Today, Sony sort of follows Microsoft's lead by announcing a slimmer version of its existing PS4. The company refers to this refresh as the 'standard' version of its console. This is important to note, you see, as Sony also announces the PlayStation 4 Pro -- a more powerful version of the console. Even with the added CPU and GPU horsepower, that naming convention seems a bit silly -- how the heck is a video game console professional?

Apple AirPods will forever change the wireless headphone industry
When Apple does something, markets react. The company is not the first to remove a 3.5mm headphone jack from a smartphone, for instance, but it will be the only one to cause the headphone industry to pivot. The decades-old audio port was just begging to die, and today, with the iPhone 7, the jack's death-clock officially starts counting down.
Further burying the 3.5mm jack and wired headphones overall, Apple today introduces its new AirPods to the world. These are no mere wireless headphones, but a total reinvention. Chocked full of ground-breaking technology, they are poised to be wildly popular with iPhone, iPad, Apple Watch and Mac users.

Apple gives and Apple takes away with the iPhone 7 and iPhone 7 Plus
Today Apple unveiled, at long last, the iPhone 7 and iPhone 7 Plus complete with a new quad-core A10 Fusion chip and iOS 10. Rumors have been circulating for some time about just what we could expect to see from the company's latest additions to the iPhone family, and many of them have turned out to be true. While much has been added, this years' model is also about taking away.
When it comes to storage, the 16GB is now a thing of the past -- 32GB, 128GB and 256GB models are your new options. As expected, also consigned to history is the traditional headphone socket, although there is a bundled 3.5mm to Lightning headphone adaptor for those who want to stick with their own earpieces rather than the bundled Lightning EarPods (which use Apple's proprietary Lightning technology). Destined to the technology trashcan as well is the clickable Home button, replaced by a touch-sensitive button with haptic feedback.

Apple unveils Watch Series 2 -- twice as fast and waterproof
The Apple Watch was first announced two years ago and arrived six months later. That's a long time in tech, so a refresh was always on the cards, and today Apple announces the wearable's successor -- Apple Watch Series 2.
It is, as you might expect, much faster, but there’s more to the new wearable than improved speed.

SoftBank completes $31.4 billion ARM acquisition
In July, SoftBank revealed its plan to acquire the British chip designer ARM Holdings for $31.4 billion and now, less than two months later, the company has announced that the acquisition is officially complete.
The Japanese telecom company has been expanding its company lately through a series of acquisitions and investments, including purchasing Sprint for $20 billion and investing $15 billion into the Japanese division of Vodafone.


