
Fintech firm Curve launches numberless cards for investors in Europe
Curve, the UK-based fintech company, has announced that European investors from its crowdfunding round will be among the first to received more secure numberless payment cards.
The cards do not feature primary account numbers (PAN) on their face to improve security. The cards' chips have the data stored on them so they can be used for contactless payments, chip and PIN transactions or in machines, and card details can only be accessed from within the Curve mobile app.
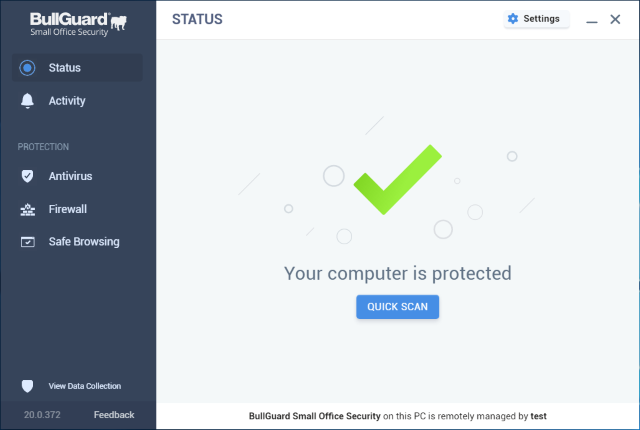
BullGuard supports small businesses with three months free Small Office Security
To help small businesses that need assistance managing their cybersecurity in the wake of the disruption caused by the coronavirus pandemic, BullGuard is offering a free, three-month license of BullGuard Small Office Security.
The offer comes with no financial obligations whatsoever and small businesses don't need to submit any form of credit card payment information to obtain their three-month cybersecurity software license.

New solution brings SD-WAN capabilities to securing endpoints
Business workloads are increasingly moving to multi-cloud and SaaS environments and at the same time the endpoint estate is diversifying to include increasing numbers of mobile and IoT devices.
As a result, CIOs and IT teams are struggling to orchestrate and enforce uniform security and compliance policies across distributed workloads and fixed, mobile and IoT devices. Enterprise mobility and connectivity specialist Asavie though has a solution.

Microsoft seeks to elevate Teams above Zoom with commitments to privacy and security
Video conferencing tools like Zoom, Microsoft Teams and Skype have been the center of attention in recent weeks because of companies' increased reliance on them during coronavirus lockdowns. Zoom has been in the headlines for many of the wrong reasons, however, and Microsoft is keen to ensure it doesn't get tarred with the same brush.
The company had made a series of commitments about its Teams software, promising users that their virtual conversations are private and secure.

American schools are banning Zoom and switching to Microsoft Teams
After many schools adopted Zoom to conduct online lessons during the coronavirus lockdown, concerns about security and privacy have led to a ban on the video conferencing software across the US.
The chancellor of New York City's Department of Education Richard A Carranza sent an email to school principals telling them to "cease using Zoom as soon as possible". And he is not alone; schools in other parts of the country have taken similar action, and educators are now being trained to use Microsoft Teams as this has been suggested as a suitable alternative, partly because it is compliant with FERPA (Family Educational Rights and Privacy Act).
Zoom enables meeting passwords and virtual waiting rooms by default as it attempts to beef up security
Zoom's skyrocketing popularity in recent weeks has been both a blessing and a curse for the company. Clearly it welcomes the additional users and, presumably, the income generated, but the company has also found itself under the spotlight resulting in startling revelations about security and privacy.
Having already apologized for a series of issues, Zoom is not taking steps to improve security. In an email sent out to users, the company explains how the virtual waiting room feature will be enabled by default, and meeting participants will now be required to use passwords to join.

Zoom admits to routing some US calls through China
As if the various privacy and security concerns that have plagued Zoom recently had not been enough, now it has been revealed that the company has been routing some calls made in North America through China.
Asking whether Zoom is a "US company with a Chinese heart", security researchers at Citizen Lab reported their discovery that during test meetings, encryption and decryption keys were routed through a server in Bejing. This raised eyebrows, and the company has now tried to explain what happened and issued its second apology this week.

Security researcher discovers vulnerabilities in iOS and macOS that could be exploited to hack webcams
After discovering a no fewer than seven security vulnerabilities in Safari for iOS and macOS, a researcher has received a $75,000 bug bounty pay out from Apple.
Ryan Pickren, a former Amazon Web Services (AWS) security engineer, found a series of security flaws in Apple's web browser, some of which could be exploited to hijack the camera of a Mac or iPhone to spy on users. The webcam hacking technique combined a total of three zero-day bugs.

How to lock down Zoom to improve your privacy and security
Zoom has received a lot of attention because of the increased number of people working from home, some good, some bad. There have been various security and privacy issues with the video conferencing app, but there are steps you can take to lock things down a little.
Following numerous controversies, Zoom has not only issued an apology but also put a stop on the development of new features while it gets itself in order. In the meantime, there are a various things you can do to increase your privacy and security when you're using Zoom.

Events tracking tool helps track and guard against phishing and spam campaigns
It's not unusual for phishing attacks to focus their efforts on major events. The end of the tax year is always popular as are major sporting occasions. The latest lure of course is the current COVID-19 pandemic.
The problem for IT admins is how to protect against a sudden deluge of threats and spam messages while ensuring that important legitimate communications aren't accidentally blocked.
Zoom issues an apology for privacy and security issues, will enact a feature freeze to focus on fixes
Zoom has been in the headlines a lot recently -- and not always for the reasons the company might have wanted. Thrust into the spotlight due to massively increased usage during the coronavirus pandemic, Zoom has been plagued with numerous security and privacy issues.
Now company CEO Eric S Yuan has issued a lengthy statement to Zoom users, apologizing for "unforeseen issues" and promising to improve things. For now, Zoom will get no new features as the company is focusing on fixing what is wrong, and regaining customer trust.

Cloudflare launches DNS-based parental control service 1.1.1.1 for Families
Cloudflare's 1.1.1.1 DNS resolver has been around for a couple of years now, helping to cater for those looking for a more private and secure internet connection. Now the company has announced a new version of the product, this time with extra protective layers.
1.1.1.1 for Families is essentially a parental control filter, automatically blocking access to "bad sites". This means not only sites that deliver malware, but also adult sites that might not be suitable for younger internet users. But while parents may welcome this automated filtering, 1.1.1.1 for Families has already come in for criticism for incorrectly blocking sites.

Cloudflare announces free VPN tool WARP for Windows and macOS, with Linux to follow
If you're in the market for a free VPN for your desktop PC or laptop, Cloudflare will soon have a new offering.
Following on from the success of its free VPN for mobile devices, the company that's also behind the 1.1.1.1 DNS resolver is now bringing WARP to Windows and macOS -- and there is a Linux version in the works. Cloudflare's WARP is currently available in beta, but not everyone will be able to get access to it straight away.

How Malicious Azure apps can be used to target Office 365
Infected mail attachments and malicious links are common ways for hackers to try to infiltrate organizations.
Researchers at cybersecurity company Varonis have uncovered at new attack route in the form of malicious Azure apps. Azure apps don't require approval from Microsoft and, more importantly, they don't require code execution on the user's machine, making it easy to evade endpoint detection and antivirus systems.

Zoom claims to offer end-to-end encryption -- even though that's not strictly true
Security is a serious concern for anyone using the internet, but it most certainly is for businesses. In seeking a video conferencing tool to see them through the home-working coronavirus has forced many people into, Zoom has proved to be an incredibly popular choice, and its proclamation of offering end-to-end encryption very probably swayed a few decisions.
An investigation carried out by the Intercept found that, despite Zoom's claims, the service does not really support end-to-end encryption for video and audio content. In reality, all it offers is TLS, but Zoom has chosen to refer to this as being end-to-end encryption.
