Shadow AI a major concern for enterprise IT
A new report reveals that nearly 80 percent of IT leaders say their organization has experienced negative outcomes from employee use of generative AI, including false or inaccurate results from queries (46 percent) and leaking of sensitive data into AI (44 percent).
Notably the survey of 200 US IT directors and executives from Komprise shows that 13 percent say that these poor outcomes have also resulted in financial, customer or reputational damage.
84 percent of attacks now use legitimate tools

New research from Bitdefender shows that 84 percent of high severity attacks are using Living off the Land (LOTL) techniques, exploiting legitimate tools used by administrators.
One of the findings is that the netsh.exe tool -- used for network configuration -- management is the most frequently abused tool, appearing in a third of major attacks. While checking firewall configurations is a logical initial step for attackers, this clearly demonstrates how data analysis can spotlight trends that human operators might instinctively disregard.
Elon Musk confirms everyone is getting the 'all new' XChat this week, complete with 'Bitcoin style encryption'

Looking to compete with the likes of Signal, Elon Musk is ready to rollout XChat to all users of his X social platform. Rather than being a separate app for chatting, however, XChat is essentially just direct messaging within X -- so who is it for, and what does it have to offer?
Taking inspiration from numerous sources, Musk says that in addition to text-based messaging, there is also video and audio calling. Other features include vanishing messages, the option to “send any kind of file”, and an undetailed encryption system.
Microsoft is making huge changes to Windows 10 and 11, cutting out nagging to use Edge... for some

There can be few Windows users who have not been frustrated by notifications suggesting that they use Microsoft Edge as their browser. Microsoft’s heavy-handed promotion of its own web browser has been the source of annoyance, frustration and lawsuits for some time.
Now the company is relenting, making sweeping changes across Windows 10 and Windows 11 that will stop some of the pestering to use Edge, and also make it easier to change default browsers. More than this, it is making changes to Windows Search, the Microsoft Store and many other apps... but not for everyone, and not because it wants to.
Vendor email compromise attacks get more effective in large enterprises

A new report from Abnormal AI shows that employees in large enterprises engage with malicious vendor messages 72 percent of the time.
Drawing on behavioral data from over 1,400 organizations worldwide, the report reveals the extent to which employees are actively engaging with advanced text-based threats like vendor email compromise (VEC) and explores the blind spots attackers are exploiting with highly targeted, socially engineered attacks.
Meeting the challenges of running a modern service desk [Q&A]

In today's interconnected world, the IT service desk often serves as the invisible backbone of any successful organization, from troubleshooting minor glitches to resolving critical system outages.
But beneath this seemingly straightforward function lies a complex web of challenges that can significantly impact efficiency, user satisfaction, and ultimately, an organization's bottom line.
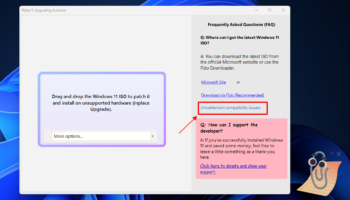
Microsoft releases emergency fix for Windows 11 startup problems

Following the release of the KB5058405 update last month, Microsoft acknowledged that it was causing problems for some users. Affected users were left with startup issues and a warning of a 0xc0000098 error in the ACPI.sys file.
Now the company has released an out-of-band fix for the issue in the form of the KB5062170 update. Such is the impact of the original problem that Microsoft recommends installing this update in place of the May 2025 security update for Windows 11.
Free AI video tool from Microsoft lets you create wild videos in seconds with Bing
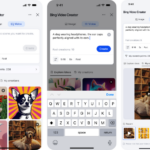
If you’ve ever wanted to make your own video without picking up a camera, editing anything, or paying a dime, Microsoft just dropped something you absolutely must check out. It’s called Bing Video Creator, and yes, folks, it’s completely free.
This new tool, powered by OpenAI’s Sora model, turns simple text prompts into five-second videos. Just type what you want to see and boom, a video appears. No editing software, no experience, and absolutely no money required.
Microsoft and CrowdStrike finally fix the stupidest problem in cybersecurity

In cybersecurity, every second counts. But when the same hacking group goes by half a dozen different names depending on which company you ask, defenders are left wasting time instead of stopping attacks. Now, Microsoft and CrowdStrike are teaming up to clean up the mess they helped create.
The two companies just announced a joint effort to map their threat actor naming systems to each other. Basically, it’s a cheat sheet for decoding the confusing and conflicting names used across the industry. Midnight Blizzard? That’s Microsoft’s name for what CrowdStrike calls Cozy Bear. Others call it APT29 or UNC2452.
Fences 6.0 is the essential desktop upgrade for Windows 10 and 11 users -- get it today!

Stardock has released Fences 6.0, a major new release of its desktop organization tool for Windows users. The app, which allows users to create windowed 'fences' to keep desktop icons under control, adds two major new features in this latest release.
The biggest update by far is the support for tabbed fences. Like web browsers, each window can now support multiple tabs to provide an additional level of organization for both desktop shortcuts and Folder Portals, which make it possible for users to mirror any folder to the desktop for ease of access.
What does Nvidia's palm-sized AI supercomputer, DGX Spark, really mean for the future of AI development at the edge?
Nvidia CEO Jensen Huang’s now-famous GTC 2025 reveal where he held up a palm-sized AI supercomputer and likened it to the original DGX-1 “with Pym particles” wasn’t just a show of engineering flair.
The DGX Spark, as it’s now officially called, marks a turning point in how we think about AI infrastructure. For the first time, Nvidia’s Grace Blackwell superchip architecture has been distilled into a 1.2kg box that fits on a desktop, priced accessibly for research teams and small-scale deployments.
New AI analytics platform is designed for enterprise frameworks

As data demands across organizations intensify they need to scale productivity and enable business users to explore data independently.
Cube is launching an agentic AI analytics platform built on a universal semantic layer which allows it to operate autonomously within enterprise frameworks, automating work while preserving trust, governance, and transparency.
65 percent of IT professionals have too many security tools

New research from Barracuda Networks finds 65 percent of IT and security professionals say their organizations are juggling too many security tools.
What's more, over half (53 percent) of respondents also say their security tools cannot be integrated -- creating fragmented environments that are difficult to manage and secure.
The practical approach to building a data mesh [Q&A]

As businesses continue to generate and rely on vast amounts of data, the traditional approach to managing that data is no longer sufficient.
Enter the concept of a data mesh -- a decentralized, domain-driven approach to data architecture that promises to transform how organizations handle and leverage their data. But the question remains: should a business create a data mesh? What value does it add, and what challenges does it help solve?
Microsoft says it is ending USB-C confusion with updated Windows 11 WHCP

USB-C was supposed to be the connection that simplified everything -- but it has ended up doing anything but making things simple. With different USB generations, and within those generations different levels of capability, it is no wonder people are confused about just what their USB ports and cables can do, and what level of capability to expect.
This is something Microsoft is looking to change. Pointing to the “inconsistent implementations of USB-C port capabilities across the PC ecosystem”, the company is seeking to end USB-C port confusion by using the Windows Hardware Compatibility Program (WHCP) to help people know precisely what to expect from certified PCs.
Most Commented Stories
© 1998-2025 BetaNews, Inc. All Rights Reserved. About Us - Privacy Policy - Cookie Policy - Sitemap.