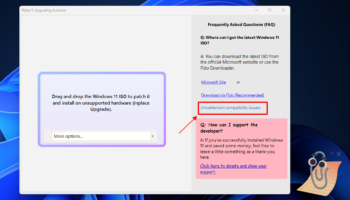
What does Nvidia's palm-sized AI supercomputer, DGX Spark, really mean for the future of AI development at the edge?
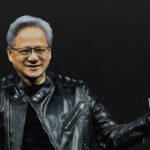
Nvidia CEO Jensen Huang’s now-famous GTC 2025 reveal where he held up a palm-sized AI supercomputer and likened it to the original DGX-1 “with Pym particles” wasn’t just a show of engineering flair.
The DGX Spark, as it’s now officially called, marks a turning point in how we think about AI infrastructure. For the first time, Nvidia’s Grace Blackwell superchip architecture has been distilled into a 1.2kg box that fits on a desktop, priced accessibly for research teams and small-scale deployments.
New AI analytics platform is designed for enterprise frameworks

As data demands across organizations intensify they need to scale productivity and enable business users to explore data independently.
Cube is launching an agentic AI analytics platform built on a universal semantic layer which allows it to operate autonomously within enterprise frameworks, automating work while preserving trust, governance, and transparency.
65 percent of IT professionals have too many security tools

New research from Barracuda Networks finds 65 percent of IT and security professionals say their organizations are juggling too many security tools.
What's more, over half (53 percent) of respondents also say their security tools cannot be integrated -- creating fragmented environments that are difficult to manage and secure.
The practical approach to building a data mesh [Q&A]

As businesses continue to generate and rely on vast amounts of data, the traditional approach to managing that data is no longer sufficient.
Enter the concept of a data mesh -- a decentralized, domain-driven approach to data architecture that promises to transform how organizations handle and leverage their data. But the question remains: should a business create a data mesh? What value does it add, and what challenges does it help solve?
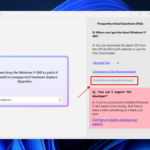
Microsoft says it is ending USB-C confusion with updated Windows 11 WHCP

USB-C was supposed to be the connection that simplified everything -- but it has ended up doing anything but making things simple. With different USB generations, and within those generations different levels of capability, it is no wonder people are confused about just what their USB ports and cables can do, and what level of capability to expect.
This is something Microsoft is looking to change. Pointing to the “inconsistent implementations of USB-C port capabilities across the PC ecosystem”, the company is seeking to end USB-C port confusion by using the Windows Hardware Compatibility Program (WHCP) to help people know precisely what to expect from certified PCs.
Microsoft Security gets a style upgrade that goes beyond the surface to embrace the human

Padlocks, chains, keys, shields: these are all stereotypical images used to represent security. They are also the themes -- tropes, if you will -- that have been avoided in an eye-catching and vibrant rebranding for Microsoft Security.
A team at Koto -- a creative studio also behind design projects for Amazon, Riot Games, FitBit, WhatsApp, and more -- is responsible for a bold new brand identity that sidesteps the obvious. Instead, the new look that is bold yet human, clear and confident.
Linux users, rejoice! CachyOS fixes Nvidia issues and kills buggy browser

CachyOS is back with its latest May 2025 release, and yes, Nvidia users can finally breathe a sigh of relief. After months of headaches caused by the distro switching to the “open” Nvidia module, older GPUs like the 10xx series were left limping along with buggy Nouveau drivers. That mess is now cleaned up. The ISO now automatically detects your GPU and loads the correct driver.
The changes don’t stop there, folks. If you’re into aesthetics, the boot process just got a fresh coat of paint. There’s a new Plymouth boot animation and GRUB theme that help unify the distro’s visual identity. It’s a small touch, but it makes a difference.
Microsoft is ruining Notepad with pointless formatting in Windows 11
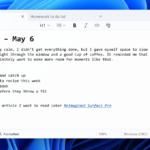
Sigh. Microsoft just can’t leave well enough alone. The company is now injecting formatting features into Notepad, a program that has long been appreciated for one thing -- its simplicity. You see, starting with version 11.2504.50.0, this update is rolling out to Windows Insiders in the Canary and Dev Channels, and it adds bold text, italics, hyperlinks, lists, and even headers.
Sadly, this isn’t a joke. Notepad is actually being turned into a watered-down word processor, complete with a formatting toolbar and Markdown support. Users can even toggle between styled content and raw Markdown syntax. And while Microsoft is giving you the option to disable formatting or strip it all out, it’s clear the direction of the app is changing.
Ditch Windows 11 and try Alpine Linux 3.22 with GNOME 48 and Plasma 6.3

Alpine Linux 3.22 is finally here (download), and if you’re tired of bloated operating systems like Windows 11, this release might be the breath of fresh air you’ve been waiting for. While Alpine is still a niche distribution, it’s slowly becoming a viable option for power users who want speed, control, and simplicity.
Despite being known as a lightweight distro often used in containers and servers, Alpine 3.22 brings some serious desktop upgrades. It now includes GNOME 48, KDE Plasma 6.3, and LXQt 2.2. Even the XFCE desktop got some love, with updated packages like xfce4-panel 4.20.4, thunar 4.20.3, and more. It’s clear Alpine is not just for the command-line crowd anymore.
UK tech leaders want the government to stop buying US cloud

New research reveals a surge in interest in data sovereignty among UK IT leaders since the implementation of the United States government's historic raft of tariffs in April.
The study from Civo, of over 1,000 UK-based IT leaders, shows more than 60 percent now feel that the UK government’s use of US cloud services exposes the country's digital economy to significant risks, damages its domestic industry, and threatens data security.
Best Windows apps this week
Six-hundred-forty-nine in a series. Welcome to this week's overview of the best apps, games and extensions released for Windows 10 and 11 on the Microsoft Store and elsewhere in the past seven days.
Microsoft released Windows Backup for Organizations to ease the transition from Windows 10 to Windows 11. Microsoft launched a private preview of a native update orchestration platform for Windows. Put simply, it enables app developers to push app updates via Windows Update.
Why data privacy is a fundamental human right

In an age where every click, swipe, and search can be tracked, stored and analyzed, data privacy is no longer a luxury but a necessity. From social media profiles to medical records and financial transactions, personal information is constantly collected and processed, often without understanding or consent.
Recognizing data privacy as a fundamental human right isn't just a legal or technical issue, but vital for individual dignity, autonomy, and freedom of expression.
Safeguarding your marketing channels: how AI-powered automation is fueling new threats and how to defend against them

Scammers are already using AI-powered automation to manipulate marketing channels. We don't want to hand out a playbook for bad actors, but it's important to recognize the growing number of scams that have been enhanced by AI and automation tools. Most scams are still about money, either directly or by collecting personal data that can be used to access financial information. If there is no money, there is typically little motive.
In a space like eCommerce, for example, we've seen scammers clone legitimate websites to trick customers into handing over their payment information. These spoof sites look identical to the real thing.
The top priorities and biggest worries for cyber leaders [Q&A]

The technology world is a fast moving one and keeping up with the latest trends can be difficult. Yet it's also essential if you're not to lose competitive edge or get caught out by new risks.
We spoke to Myke Lyons, CISO of data infrastructure company Cribl, to discuss what the priorities for cyber leaders should be and what things are likely to keep them awake at night.
Instagram announces support for the most commonly used photo aspect ratio

Post an image to Instagram and it will almost certainly be automatically cropped. The reason for this is that, until now, the platform has supported 4:5 aspect ratio images, as well as the Instagram staple -- the square format.
But this is not in line with how most people shoot photographs, and the platform is finally taking this into account. There is now support for a new (new to Instagram, at least), aspect ratio.
Most Commented Stories
© 1998-2025 BetaNews, Inc. All Rights Reserved. About Us - Privacy Policy - Cookie Policy - Sitemap.