How to download the Windows 11 23H2 ISO
Microsoft has now officially launched Windows 11 23H2, and the company is also referring to this latest release as the Windows 11 2023 Update.
This update is due to roll out as an automatic update in the coming months, but it is currently available for those who manually seek it out. If you have multiple computers to update, if you want to install the latest version of Windows 11 in a virtual machine, or you just want to make sure you have the latest installation media, here's how to download the Windows 11 23H2 ISO -- or how to download the Windows 11 2023 Update ISO if you prefer this name.

End of the line: How UK businesses can prepare for the telecoms Big Switch Off [Q&A]
With the UK's national 'Stop Sell' having commenced in September this year and the Public Switched Telephone Network (PSTN) switch off due by December 2025, business owners need to have all the facts and critical information that they need to act fast and confidently to make the right decisions about their digital alternatives.
With the switch off deadline looming how can businesses in the UK ensure that they are prepared for these significant, but exciting changes to communications?

YouTube toughens its stance on blocking ad blockers
Ad blockers tend to make the internet a more palatable place to explore, but in recent times there has been an increase in ad block detection. Coupled with this has been the introduction of nag screens or content being rendered inaccessible until ad blocking is disabled.
YouTube is one of many big-name sites to have ramped up its efforts to discourage -- and ultimately stamp out -- the use of ad blockers. Now the company is expanding its attack on users who try to avoid ads, and is using the effort to simultaneously promote YouTube Premium.

Famed brand RCA returns with new Evolution M Series Flat Gaming QHD monitors
Ah, RCA. A brand that dates back over a century. Known for its ground-breaking ventures in the electronics industry, RCA has now embarked on a new journey, making its way into the competitive world of gaming monitors.
With the unveiling of the RCA Evolution gaming monitor lineup, the company has once again highlighted its commitment to delivering exceptional value. It’s a nostalgic yet forward-thinking move, reminiscent of RCA’s glorious past, blended seamlessly with the demands of modern gaming dynamics.
Windows 11 2023 Update (23H2) begins rolling out now -- here's how to get it
Microsoft has begun rolling out its Windows 11 2023 update (version 23H2), which makes Copilot AI available to more users, and introduces some new enhancements. This is the follow up to the AI preview release which came out last month.
Windows 11 2023 Update (23H2) is a "scoped, cumulative release" and among the changes are that "Chat" is now "Microsoft Teams (free)" and it comes pinned by default to the taskbar. There are also some changes made to the way you manage applications.

Micron launches Crucial T500 PCIe Gen4 NVMe M.2 SSD for PC and PlayStation 5
Today, Micron launches the Crucial T500 Gen4 NVMe solid state drive. At the heart of the T500 SSD is Micron’s advanced 232-layer 3D NAND technology, propelling the drive to industry-leading NAND I/O speeds of 2.4 gigabytes per second (GB/s).
The Crucial T500 SSD comes in two distinct variants catering to different user needs. The heatsink version is tailored for the PlayStation 5 (PS5) and PC gaming rigs, ensuring optimal thermal management, while the non-heatsink version is a snug fit for laptops, desktops, and workstations, offering a balance of performance and portability.

Secure software depends on clean code -- AI-generated or not
Software is immensely pervasive and foundational to innovation and market leadership. You’ve likely heard the popular phrase coined by McKinsey that "all companies are software companies." It’s true that businesses are competing and winning in their markets based on their ability to digitize and innovate. Almost every major enterprise, no matter its industry, relies heavily on software to deliver services, manage operations internally or promote itself.
Software starts with code, which means that secure or insecure code starts in development. As long as we continue to view security as a bolt-on or an after-the-fact fix, we’ll continue to widen the chasm between the pace of digital innovation and security’s ability to keep up. With AI-generated code increasing the volume and speed of software production without an eye toward code quality, this problem will only worsen. The world needs Clean Code. Without it, the performance of software will suffer, negatively impacting the business.

SteelSeries celebrates Halloween with extremely limited Ghost Edition Apex Pro Mini gaming keyboard
SteelSeries, a popular name in the gaming world, has unveiled its new Ghost Edition Apex Pro Mini keyboard today, and it’s something very special. This launch is not just about a new keyboard, it’s a shout-out to Halloween! 👻
This keyboard is a cool blend of sleek design and top-notch performance, just like the scary and powerful Frankenstein monster. It’s got a compact design, super-fast response times, a limited-edition see-through color, and bright, colorful lights making it a real showstopper of a keyboard.
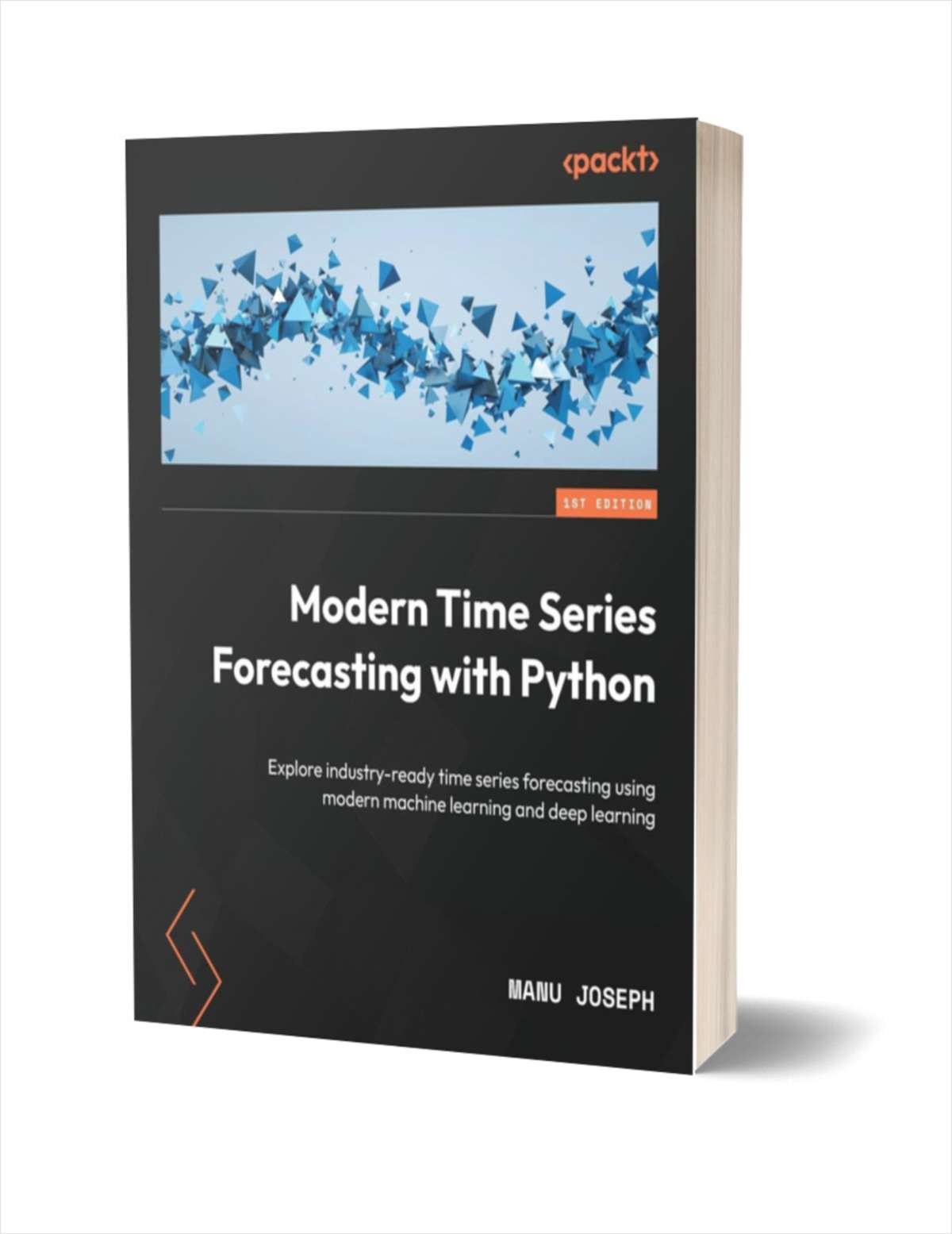
Get 'Modern Time Series Forecasting with Python' (worth $42.99) for FREE
We live in a serendipitous era where the explosion in the quantum of data collected and a renewed interest in data-driven techniques such as machine learning (ML), has changed the landscape of analytics, and with it, time series forecasting.
This book, filled with industryed tips and tricks, takes you beyond commonly used classical statistical methods such as ARIMA and introduces to you the latest techniques from the world of ML. This is a comprehensive guide to analyzing, visualizing, and creating state-of-the-art forecasting systems, complete with common topics such as ML and deep learning (DL) as well as rarely touched-upon topics such as global forecasting models, cross-validation strategies, and forecast metrics.

Mission data privacy: Empowering consumers in an era of rapid change
Whether browsing online for clothes or catching up on the latest news, we’ve all had that unwanted internet cookie pop-up appear. At face-value they may seem harmless, but cookies are a goldmine of private information, posing a serious risk to your data privacy. Today, consumers face a new predicament surrounding attitudes toward their valuable data. When personal data is stolen by a cybercriminal, that offense is the online equivalent of a physical robbery, but the severity of data theft is being overlooked.
From a regulatory standpoint, concerns over data privacy have prompted stricter actions from governments and organizations globally as they try to grapple with the challenge of striking a balance between data security and user privacy. Now, in response to increasingly sophisticated criminal tactics, there must be a shift from slow, reactive regulation towards adopting more proactive strategies that both anticipate and mitigate against potential risks. This will be key to shaping a secure, privacy-conscious future.

Prolific Puma protects pernicious phishing plotters
We're all familiar with link shortening services, those handy tools that allow you to shrink URLs down to a manageable size to make them easier to share.
Of course in the past these have been used for nefarious purposes too, hiding the true nature of a link to get people to click on phishing or malware messages. Now though researchers at Infoblox have uncovered something even more sinister, the operation of a shady link shortening service made especially for cybercrime.
How to supercharge your productivity with AI: Tips and tools to work smarter, not harder
Productivity has significant importance in the contemporary dynamic work environment. AI has the potential to enhance operational efficiency and optimize operations by eliminating unnecessary tasks. AI has the potential to automate many procedures, provide valuable insights, and enhance workflows, hence enhancing professional productivity and overall cloud data management.
This piece explores the potential of artificial intelligence (AI) to enhance productivity.

What IT teams need to know about Google's privacy changes
It’s no secret the depreciation of third-party cookies has been a popular topic of conversation in the industry. Now, however, Google is making changes that will eventually lead to the demise of third-party cookies. The tech giant is rolling out its Privacy Sandbox initiative in the latest version of Chrome and for Android. With any big privacy change, there is a ton of controversy and impending regulations that may mean the Privacy Sandbox is not the futureproof solution brands hope it is.
So, what can IT teams do to help marketers take back control of their data collection strategies and ethically reach customers during this time of change?
Business is booming on the dark web -- what does this mean for cyber risk?
It's been another profitable year for the cybercriminal underworld. Once again, headlines have been regularly dominated by serious breaches such as the Royal Mail and Capita, whilst behind the scenes, criminal gangs have raked in huge profits.
The shadow economy of the dark web has continued to thrive and develop as a mirror of the legitimate business world. Threat actors are increasingly well-organized, from highly developed ransomware-as-a-service (RaaS) offerings to extremely lucrative vulnerability trading. Here, we'll delve into the most prominent trends driving the bustling dark web economy -- and how organizations can defend themselves against such threats.

UK faces record cybersecurity skills gap
The UK cybersecurity workforce gap has reached a record high, with 73,439 professionals needed to adequately safeguard digital assets, representing a 29.3 percent increase over 2022.
Research by security professionals organization ISC2 shows the UK cybersecurity workforce has reached 367,300 people, an 8.3 percent increase from 2022, representing more than 28,000 new jobs.