One in every 17 mobile devices is used to conduct bad bot attacks
Cybercriminals are using mobile devices to avoid detection and execute a number of nefarious acts, according to a new report.
The study from bot mitigation specialist Distil Networks finds 5.8 percent -- around one in 17 -- of all mobile devices across six major cellular networks are used in such automated attacks and represent eight percent of all bad bot traffic.

70 percent would leave a job if their digital activity was secretly monitored
A new Harris Poll commissioned by insider threat detection company Dtex Systems looks at employee attitudes towards the monitoring of their digital activities.
Carried out in the wake of data collection, monitoring and privacy scandals at Facebook and elsewhere, it shows that 45 percent of Americans believe it is at least sometimes acceptable for employers to monitor employees' digital activities to protect against security threats and data breaches.

Dashlane launches scanning tool to help you protect online accounts
We all sign up to online accounts for various things but over time it can become hard to remember which address you used for each site, what password you used or indeed whether you’ve previously signed up to a site at all.
Password management specialist Dashlane is launching a new feature for mobile users of its password manager called Inbox Security Scan, to give people an insight into the current state of their online accounts.

Coin mining malware grows by over 600 percent as criminals 'infect and collect'
A new report from McAfee Labs has seen coin mining malware grow by 629 percent in the first quarter 2018 as criminals seek to cash in on cryptocurrency trends.
On average the company has seen five new threat samples every second, including growth in cryptojacking and other cryptocurrency mining malware, and notable campaigns demonstrating a deliberate drive to technically improve on the most sophisticated, established attacks of 2017.

Boards focus on security awareness post WannaCry
Awareness of cybersecurity at board level is growing as last year's WannaCry attack has highlighted the need to guard against attacks.
The research, conducted by Vanson Bourne, as part of an international survey of 500 businesses in the UK, France, Germany and the USA, was commissioned by endpoint protection specialist SentinelOne.

Cisco Talos releases free decryptor for Thanatos ransomware -- ThanatosDecryptor
Getting hit by a ransomware attack is bad enough; it means that your files have been encrypted and you'll be asked to pay a fee in a cryptocurrency such as Bitcoin or Ethereum to unlock them. The problem is that paying the ransom is in no way a guarantee that your files will be decrypted -- the ransomware was created by criminals, after all.
If you've been struck by the Thanatos ransomware, however, there's good news from Cisco Talos. The company has analyzed the malware and developed a free decryption tool that will enable you to get your files back without having to part with any money.

New portal offers greater visibility into security gaps
It can be difficult for security teams to identify the weak spots in their organization's controls that put the security of the business at risk.
Managed security services provider Proficio is addressing this by launching a new version of its ProView Plus consumer portal that includes ThreatInsight risk scoring.

SMBs are underprepared for cyberattacks
No business is immune from cyber attack, and smaller companies are often targeted as they lack the resources to put into first class protection.
A new survey by cybersecurity company Webroot of 600 IT decision makers (ITDMs) at small- to medium-sized businesses, finds that the attacks organizations believed themselves to be most susceptible to in 2017 are rapidly shifting in 2018, while businesses still feel underprepared.

Consumers don't fully trust digital assistants
Given recent scares about digital assistants recording conversations, it's perhaps not surprising that levels of trust in these devices are not high.
The latest State of Digital Lifestyles survey from Limelight Networks reveals that adoption of digital assistants is highest in the US where 35 percent of consumers currently own one, however, these consumers still have major trust issues with the devices.

Wi-Fi Alliance starts to certify WPA3 devices
The rise in popularity of smart devices in the home -- coupled with our continuing love of laptops, tablets and phones -- means that we're more reliant on wireless networks than ever before. But the security we rely on to keep things safe is at least 14 years old, if not older (the widely used WPA2 started life back in 2004).
Clearly, it's time for a security upgrade, and to this end, the Wi-Fi Alliance has just started certifying devices that support WPA3 -- the predictably-named successor to WPA2. This latest security protocol includes a number of important enhancements, and is available in two varieties: WPA3-Personal for the average home user, and WPA3-Enterprise for environments that work with sensitive data and require even greater security.

Privacy group EFF announces STARTTLS Everywhere to secure emails with hop-to-hop -- but not end-to-end -- encryption
When it comes to messaging tools, people have started to show greater interest in whether encryption is used for security, and the same for websites -- but not so much with email. Thanks to the work of the Electronic Frontier Foundation, however, email security is being placed at the top of the agenda.
The privacy group today announces STARTTLS Everywhere, its new initiative to improve the security of the email eco-system. STARTTLS is an addition to SMTP, and while it does not add end-to-end encryption, it does provide hop-to-hop encryption, which is very much a step in the right direction.

Average initial coin offering has at least five vulnerabilities
Every month there are fresh cryptocurrencies springing up, but new research by Positive.com has discovered an average of five separate vulnerabilities in each initial coin offering (ICO) project examined in 2017.
What's more, 47 percent of the ICO vulnerabilities uncovered were medium to high severity. Just one vulnerability is enough for attackers to steal investors' money and do irreparable damage to corporate reputation.
Google adds DRM to Android APKs to verify the authenticity of apps from Google Play
DRM is something that's usually associated with streaming music and video, but there's no reason that it can't be put to other uses. Proving this, Google has started using a form of DRM to improve app security by verifying that APKs originate from the Play Store. It's a system that works much like signed drivers in Windows.
The aim is simple: to improve the security of Android users by ensuring that they are using genuine apps that have not been tampered with in any way. Google is not referring to the new system as DRM, saying instead that it is adding a "small amount of security metadata on top of APKs to verify that the APK was distributed by Google Play".

Don't panic! Hackers have not found a way to bypass the iPhone passcode limit
Enter the wrong passcode into an iPhone and you'll not only be denied access to it, but also run the risk of wiping its contents if you enter an incorrect code too many times. This is a problem faced by law enforcement agencies when they encounter iPhones in the cases they're working on -- as well as people trying to hack into phones for nefarious purposes -- so it's little wonder that hackers are constantly trying to find a way to earn unlimited guesses at passcodes.
One hacker thought he had cracked it. Security researcher Matthew Hickey proudly boasted at having discovered a delightfully simple method for brute-forcing entry into an iPhone -- he even posted a video of his hack in action. But there's no need to panic. Apple explains that "incorrect testing" renders Hickey's method worthless.
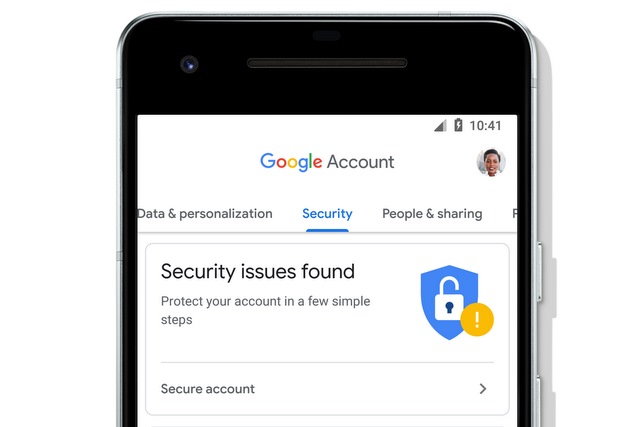
Google Account revamped -- increased transparency and new security and privacy options
Google has unveiled a new look for users' accounts, making information clearer, improving transparency and adding new options.
To make it easy to find information, Google has added a search function and there's also a cleaner look to aid navigation. Building on the previous update to Security Checkup, your Google account now also highlights settings you can change to improve your security.
