
ADATA T5000C USB power bank has a floral design and fun pastel colors
We are currently in spring, and Mother’s Day is fast approaching, so you had better start thinking about colorful and whimsical gifts for mom. Sure, you can get her a foot bath, bird house, or some other crappy present, but this year, why not get her something she can actually use? Maybe something technology related...
Today, ADATA unveils a new tech product that’s not only perfect for springtime, but it should make an ideal Mother’s Day gift too. Called “T5000C,” it is a USB power bank that features a fantastically feminine floral design and pastel colors that are sure to delight your mom. The girly power bank even offers both USB-A and USB-C, so it is very versatile too.
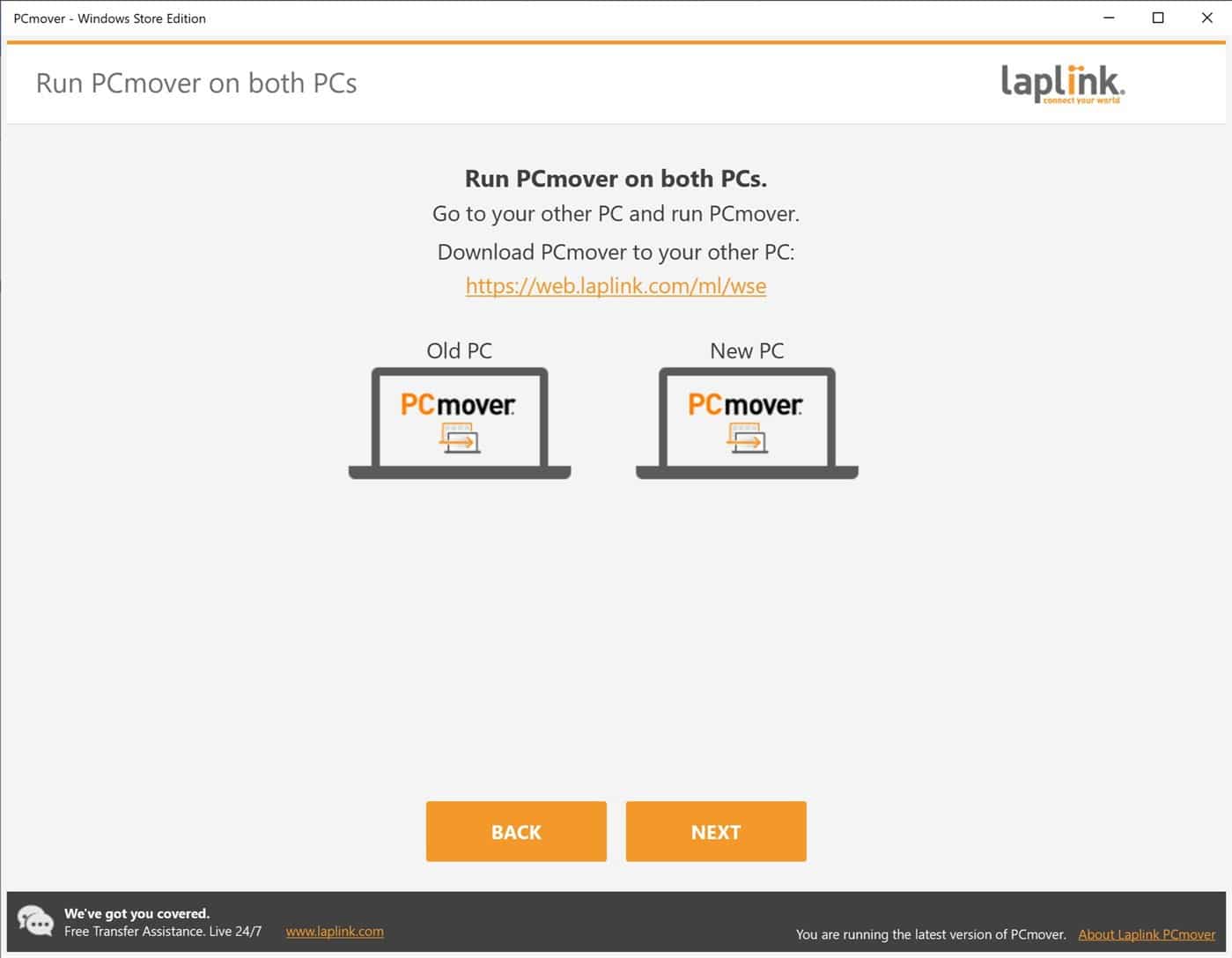
Laplink launches a free Windows Store edition of PCmover
Laplink's PCmover tool has been around for a while now, making the process of migrating to a new PC easier and faster than ever. Now the company has launched the new PCmover - Windows Store Edition which has a key difference to other versions.
This particular edition of the software brings support for Windows 10 S. Also known as Windows 10 in S Mode this is a more secure mode of Windows which aims to improve security by only allowing users to install apps from the Microsoft Store. PCmover - Windows Store Edition is the first PC migration tool to offer support for Windows 10 S, so it's ideal for anyone who wants to move away from a computer that is in this mode, or who wants to migrate to a newer Windows 10 S system.

ViacomCBS brings Comedy Central, MTV, Nickelodeon, and more to YouTube TV
When I decided to "cut the cord," I switched to YouTube TV and never looked back. Quite frankly, switching to Google's live TV service was one of the most rewarding tech-related choices of my life. It felt so good to turn in my rented TV boxes to the cable company after getting "nickeled and dimed" for years. More importantly, YouTube TV offers a great television-watching experience where I can watch anywhere I have an internet connection -- it is quite remarkable.
As great as YouTube TV was, however, it was not perfect. When I first signed up, there were many missing channels, but thankfully, the service has since added many of them. Sadly, my family still had a few ViacomCBS channels that we really missed, such as MTV, TV Land, and Comedy Central. For me personally, it was tough not to have the TV show South Park. Today we learn that this will soon change, as the channels I desire -- plus more -- are finally coming to YouTube TV!
Zoom is gaining end-to-end encryption following acquisition of Keybase
As part of its 90-day security focus, Zoom has announced that it has acquired Keybase, an app that features end-to-end encryption to secure chats and file sharing. The Keybase team will help to bring the same security to Zoom.
The lack of end-to-end encryption has been one of the many criticisms of Zoom in recent months, and the company is keen to address this. However, Zoom says that it will only be bringing an end-to-end encrypted meeting mode to paid accounts and points out that this "privacy over compatibility" option will mean missing out on some features.

Gaming helps people cope with lockdown -- but at a cost
A new survey, commissioned by cybersecurity company BullGuard, has revealed that gamers are taking advantage of the social isolation to up their playing time
By doing so, 49 percent say they are alleviating lockdown anxiety, 84 percent are understandably relieving their boredom, while 60 percent are battling it out online to help block out the current situation.

The average password is reused 2.7 times
Despite the fact that credential stuffing using stolen passwords is one of the most common ways of breaching systems, new research from Balbix for this year's World Password Day finds that over 99 percent of employees reuse passwords across work accounts, or between work and personal accounts.
In addition the average password is reused not just once, but 2.7 times, and the average user is sharing eight passwords between all their accounts with 7.5 passwords shared between work and personal accounts.

Google delays Android 11
Google has released a new preview version of Android 11 for developers to play with, and also revealed details of a revised release schedule for the operating system.
Android 11 Developer Preview 4 has been released ahead of the first beta version, and it should come as no surprise to anyone that, given what's been going on in the world recently, this launch has been pushed back a bit. The good news is that everyone will be able to attend the launch event.
Hacker group has targeted Asia Pacific governments in five-year campaign
Researchers at Check Point have uncovered a China-based hacker group that has been targeting multiple national Governments in the APAC region over the past five years, to gather political intelligence and conduct espionage.
Targets include Australia, Indonesia, Philippines, Vietnam, Thailand, Myanmar and Brunei. After infiltrating one government body, the hacker group uses that body’s contacts, documents and servers to launch targeted phishing attacks against new government targets.

Microsoft releases Windows 10 Insider Build 19624
Today is a big day for Microsoft as the firm has announced a number of new hardware devices, including Surface Book 3 and Surface Go 2.
It has also rolled out yet another new Windows 10 build for Insiders on the Fast ring.
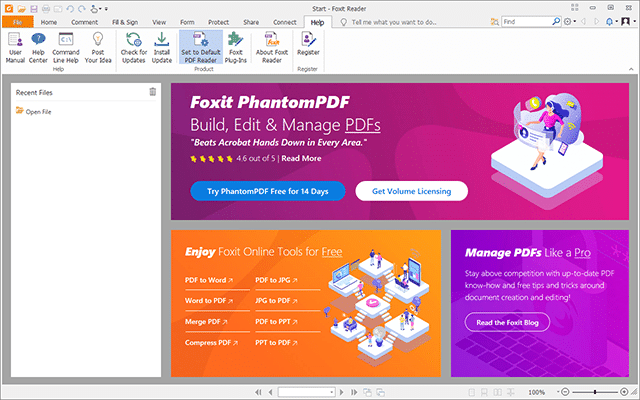
Foxit Reader 10 unveils new Fill & Sign tool, but drops ability to create PDFs
Foxit Software has unveiled landmark updates across its range of PDF viewing and editing tools for Windows PCs. There’s the brand-new free Foxit Reader 10.0 for those who simply need a fast, lightweight PDF viewing tool with handy extras like basic annotation and editing tools.
For those looking for more functionality, Foxit Phantom Standard 10.0 offers more advanced tools for editing, creating and converting PDF files to other formats.

Collaboration between teams helps boost security confidence
Organizations using software to help their IT and information security teams collaborate and align are three times more confident in the effectiveness of their information security efforts according to a new study.
The report from security automation specialist SaltStack shows that 54 percent of InfoSec leaders say they communicate effectively with IT professionals, but only 45 percent of IT professionals agree.

Microsoft unveils Surface Go 2, proving the company doesn't know when to quit
The Surface Go was always a very curious device. It is essentially a smaller Surface Pro with very deficient specifications. It was hard to know who it was really for. Power users certainly weren't interested since it was so woefully under-powered, and home consumers weren't clamoring for the terrible Windows 10 tablet experience. Who the heck wanted a netbook that couldn't even be used comfortably in a lap? A better and bigger laptop can be had for the same price. Ultimately, the Go was universally panned as a joke.
With all of that said, Microsoft has cut its losses and moved on, right? Of course not! This is Microsoft we are talking about. Instead, the company is releasing a sequel. Yes, the Surface Go 2 is officially on the way, and while the screen is a bit larger, it will once again have a terrible processor and no real target audience.

Vulnerabilities allow hackers access to two popular VPNs
New research from VPNpro has found that two of the top 20 premium VPN apps have crucial vulnerabilities that can allow hackers to push fake updates and install malicious programs or steal user data.
The vulnerabilities in PrivateVPN and Betternet, can allow hackers to intercept communications and force the apps to download a fake update. The update may be automatically installed or the user prompted to install it.

Microsoft takes on Apple's new MacBook Pro with Surface Book 3
Earlier this week, Apple revealed its new 13-inch MacBook Pro with double the storage, improved performance, and the company’s Magic Keyboard.
Following on from that announcement, Microsoft has takes the wraps off Surface Book 3, its most powerful laptop to date.

Translation Service DeepL adds Glossary feature to customize translations
Translation service DeepL just announced the introduction of the new glossary feature on the site to improve translations further.
DeepL was established in 2017 as an alternative to Google Translate, Microsoft Translate and other translation services. The developers promised that translations would be more human-like than those of competing services; several blind tests were conducted by DeepL to confirm the claim.
