
Webroot launches VPN to protect Wi-Fi users
Many people rely on connecting to Wi-Fi networks when they are out and about, but using public hotspots does present a significant security risk.
The best way to protect yourself is to use a VPN and cybersecurity company Webroot is launching its own in the form of Webroot WiFi Security, to provide security and privacy for users who connect to WiFi networks using Windows, Mac, and Android operating systems.

Cybersecurity faces a worldwide shortage of almost 3 million staff
New research from (ISC)² -- the world's largest non-profit association of cybersecurity professionals -- reveals a worldwide skills gap of 2.9 million.
The Asia-Pacific region is experiencing the highest shortage, at 2.14 million, in part thanks to its growing economies and new cybersecurity and data privacy legislation being enacted throughout the region. North America has the next highest gap at 498,000, while EMEA and Latin America contribute 142,000 and 136,000 to the staffing shortfall, respectively.

Bye bye, TLS 1.0 and 1.1: Apple, Microsoft, Mozilla and Google all wave adieu to old security protocol
As part of a coordinated movement between four of the biggest names in tech, the old TLS 1.0 and 1.1 security protocols are to be killed off in Safari, Edge, Internet Explorer, Firefox and Chrome in 2020.
Apple, Microsoft, Mozilla and Google have come together to purge the internet of these old and buggy protocols, noting that most people have now moved to TLS 1.2, if not TLS 1.3. Although 94 percent of sites already support version 1.2, a tampering off period over the next 18 months will give everyone a chance to catch up.

Complexity is an obstacle to effective security tools
Although IT operations personnel often help influence the selection of cyber security tools, nearly two out of three say complexity is one of the biggest hindrances in their effectiveness.
The study by privileged access management company Thycotic shows complexity in deployment is cited by30 percent and complexity in daily use by 34 percent.

Digital transformation increases risk of cyberattacks
The drive to digital transformation is exposing companies to higher and more costly cyber risks according to a new study of over 1,300 businesses.
The study from research firm ESI ThoughtLab, together with a cross-industry coalition of organizations, including HP, KnowBe4, Opus and others, shows that cyber risks rise dramatically as companies embrace new technologies, adopt open platforms, and tap into the ecosystems of partners and suppliers.

New technology helps businesses to assess cyber risks
In a world of digital transformation projects that increasingly mean more links to suppliers and partners, it can be hard for companies to assess the risk presented by opening up their data to third-parties.
To address this problem RiskRecon is launching new asset valuation algorithms that automatically determine the inherent risk value of any internet facing system.

Cyberattacks shift their focus onto business in third quarter
After a relatively quiet first half of the year, cyberattacks have come back with a bang in the third quarter according to the latest report from Malwarebytes.
Businesses seem to have become the main focus of attacks, experiencing more cybercriminal activity this quarter, with detections up by 55 percent, while consumer detections increased by only four percent over the last quarter.

Malicious messages are locking up PlayStation 4 consoles
We've heard of problems with specially-crafted messages being used to lock up iPhones, and now a similar problem has been found with the PlayStation 4. Anyone who receives one of these messages will find that their console completely locks up -- and the only way out of it is to perform a factory reset.
The problem lies in messages that include unrecognized characters, and it is being exploited by some gamers to boot people offline in the middle of games -- Rainbow Six in particular. While there is no fix available at the moment, there are steps you can take to prevent the issue affecting you.

UK government launches guidance to help secure IoT devices
There are expected to be more than 420 million internet connected devices in use across the UK within the next three years and if poorly secured these can leave people exposed to security issues and even large scale cyberattacks.
To address this, a new voluntary Code of Practice is being launched by the UK government to help manufacturers boost the security of internet-connected devices such as smartwatches, virtual assistants and toys.
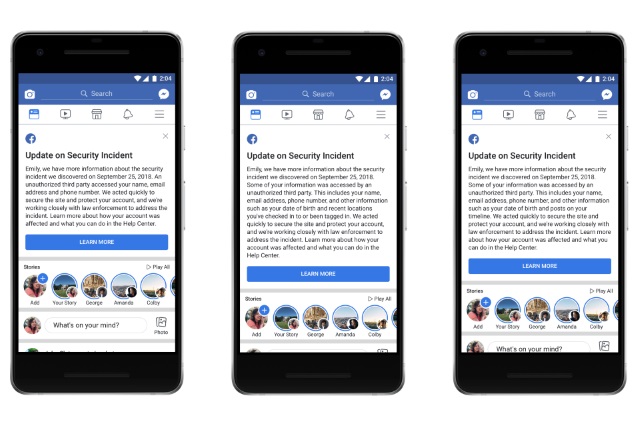
How to see if you were affected by the huge Facebook hack
The most recent Facebook security issue is one of the most serious yet for users of the social network. Depending on which numbers you are look at, the hackers who exploited a security flaw have impacted on anything between 14 and 30 million people.
Facebook is still -- with the help of law enforcement agencies -- investigating the incident, and in the meantime many people feel as those they are being left in the dark. If you want to find out if your account has been affected, here's what you need to do.

Facebook says hackers accessed highly-detailed personal data of 15 million users
In a news release with the bizarrely vague title of "An Update on the Security Issue", Facebook has revealed that the "View As" security breach it opened up about recently gave hackers access to the personal details of 15 million users.
Having previously advised that the access tokens stolen by hackers had not been used to infiltrate other apps and services, the social networking giant now says 15 million people have had their names and contact details exposed. 14 million users had significantly more details revealed, including username, relationship status, religion, hometown, birthdate, places they have checked into, and recent searches.
Businesses risk penalties by not wiping data from old equipment
New research from IT procurement company Probrand shows that 68 percent of UK businesses have failed to wipe the data from IT equipment before disposal, leaving them open to fines under GDPR if data is exposed.
In addition 70 percent admit to not having an official process or protocol for disposing of obsolete IT equipment.

Should businesses prepare for ransomware with a cryptocurrency stash? [Q&A]
An increasing number of enterprises are considering pre-purchasing cryptocurrency in anticipation of potential ransomware attacks. But is this a valid risk-reduction strategy for enterprises?
To get some views on this controversial issue, we spoke with Mike Doran, senior security consultant with the enterprise incident management team at cybersecurity specialist Optiv, and former computer forensics examiner with the St. Louis Metropolitan Police Department.

Two out of three worry about identity theft but half still engage in risky behavior
A new survey from identity management specialist SailPoint in conjunction with US National Cybersecurity Awareness Month finds two out of three professionals are extremely concerned about their personal identity being stolen.
Yet despite this half admit that they would participate in the types of risky behavior that increase the threat of leaked information and a potential breach.

Hackers, geeks and thieves -- analysis of dark web communities reveals varied motives
When we talk about the dark web it's easy to think of it as an amorphous malevolent blob. But new research from Recorded Future reveals some key differences between dark web communities in different parts of the world.
The company's Inskit Group of researchers has actively analyzed underground markets and forums tailored to Russian and Chinese audiences over the past year and has discovered a number of differences in content hosted on forums, as well as differences in forum organization and conduct.
