Dropbox introduces new AI-powered productivity features
Cloud storage provider Dropbox is launching two new AI-powered productivity tools -- though they're not available to everyone just yet.
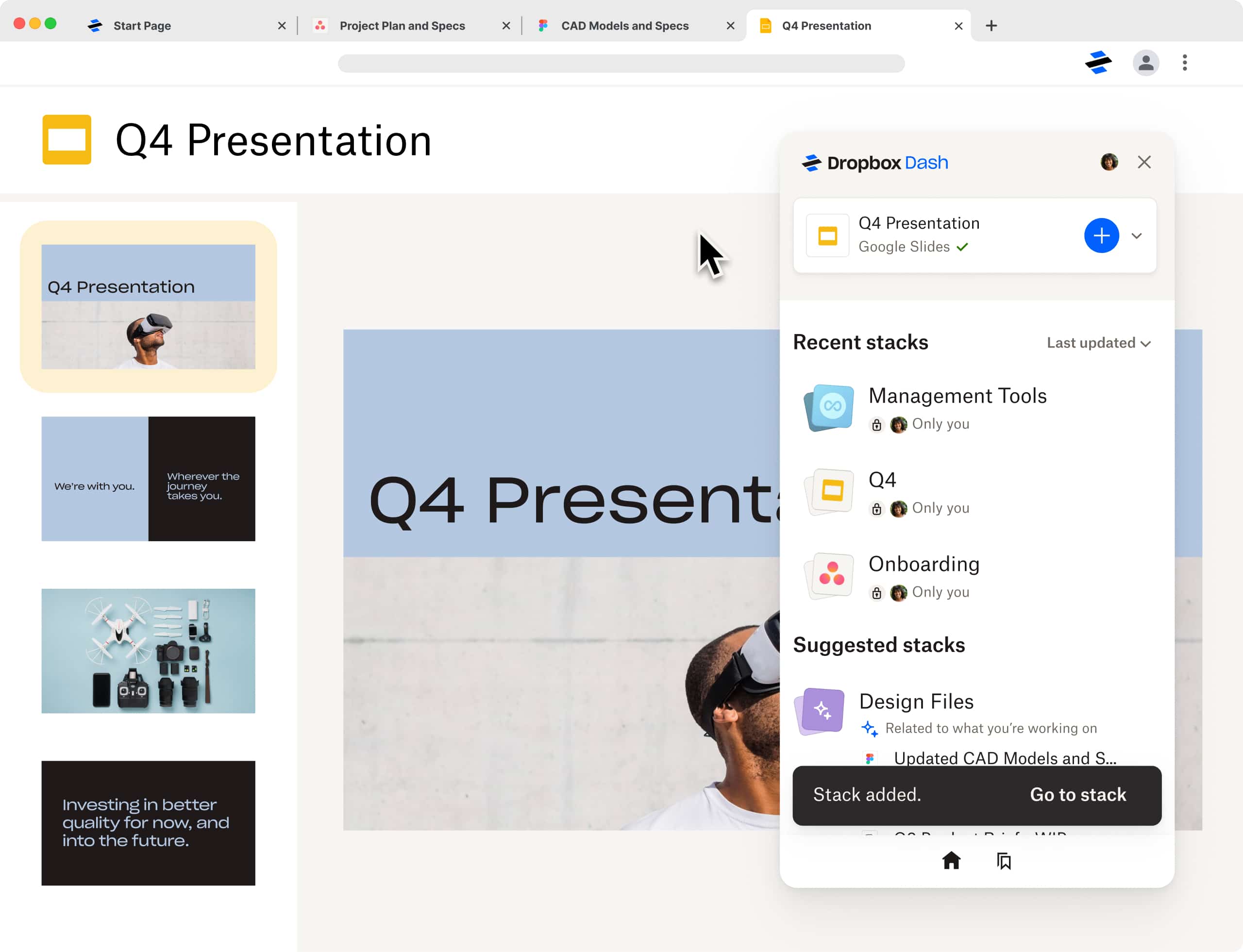
Dropbox Dash is a universal search that connects all of your tools, content, and apps in a single search bar to help you easily find what you need. There's also Dropbox AI, a new feature that lets customers quickly summarize and get information from their Dropbox files.

End of life data risks sustainability targets
Environmental sustainability has a high to moderate influence on their approach to processing end of life (EOL) data for 88 percent of respondents according to a new survey.
But more than a third (39 percent) of enterprises are yet to implement a plan to reduce their data footprint, leaving them at risk of compliance failures in light of upcoming sustainability regulations.

Enterprises rush to implement FinOps but aren't yet seeing value from it
FinOps is increasingly being adopted, with 98 percent of respondents to a new survey from Cloudbolt either having a FinOps strategy or planning to implement one. But while 71 percent of companies have expanded funding for FinOps resources in 2023, 99.8 percent say they are still waiting to see any value from it.
In case you haven't been paying attention, FinOps is an operational framework that brings technology, finance, and business together to drive financial accountability and accelerate value through cloud transformation.

Why cloud connectivity doesn't have to be complicated
Whether it’s a delay on the first leg of a connecting flight, buffering on Netflix, or a weak signal during a train journey, nobody likes it when a connection fails. We live in a world of instant gratification and downtime (even seconds) frustrates us all.
That’s especially true for organizations that have migrated their applications and workloads to the cloud. A study by Netwrix determined that, on average, companies have 41 percent of their workloads in the cloud and plan to reach 54 percent by the end of 2023. What’s more, Flexera found that 89 percent of businesses using cloud storage embrace a multi-cloud strategy, and 80 percent of those organizations take a hybrid approach. Cloud strategies are becoming more popular, flexible and complex than ever.

Enterprises paying too much for cloud as economic climate bites
A new global survey of 600 IT decision makers finds that 54 percent say the cloud is vital to balancing their IT spending, however, 44 percent are actively looking for ways to reduce and/or control their cloud spend due to economic conditions.
The study, from database platform Couchbase, finds that on average enterprises spend $28.91 million on cloud services, resulting in an overspend of approximately $6.5 million.

Cloud revolution: Reinventing IT infrastructure for the modern era
One of the greatest misconceptions about cloud technology? That it somehow downplays the significance of IT infrastructure. Nothing is more false than that. The importance of infrastructure to the success of the company has never been greater. That's because technology has never had a bigger role than it does now in assisting businesses in generating profitable growth, developing cutting-edge experiences, and conducting sustainable, accountable business.
The foundation of the modern "ever-ready" digital enterprise is infrastructure. Infrastructure serves as the framework on which businesses can run this enormous growth of potential with ease. It offers the computing, networking, workspace, and database platform characteristics required to execute the business-critical applications. Additionally, it offers the base upon which outstanding consumer and staff experiences can be created.

Complex environments mean enterprises can't use a third of their data effectively
New research from hybrid data company Cloudera reveals that organizations currently estimate they are not using 33 percent of their data effectively.
The survey 850 IT decision makers (ITDMs) across the EMEA region shows 72 percent of respondents agree that having data sitting across different cloud and on-premises environments makes it complex to extract value from all the data in their organization.

Canonical brings OpenStack to small-scale clouds
Canonical has announced the extension of its commercial OpenStack offering to small-scale cloud environments with a new project, Sunbeam.
The project is 100 percent open source and is available free-of-charge, but enterprise customers can also opt-in for comprehensive security coverage and full commercial support under the Ubuntu Pro + Support subscriptions once they’ve completed the deployment.

Industry cloud platforms: The complete guide
Although general-purpose cloud platforms paved the way for new business technologies, they only address horizontal market issues. Simply put, these cloud computing products provide generalized solutions. SaaS products leave little room for configuration, while IaaS and PaaS systems require extensive coding experience.
To tackle vertical market challenges, you need industry cloud platforms. They’re an emerging trend that combines SaaS, IaaS, and PaaS technologies into one out-of-the-box system, and you can configure them to focus on industry-specific issues. Since they’re new to the market, you might find them confusing. Don’t worry -- we’ll discuss everything you should know about industry cloud platforms, their advantage over general cloud products, and the common challenges faced when executing them.

Microsoft no longer supports Windows 8, and soon neither will Google Drive
It is now several months since Microsoft stopped supporting Windows 8 and Windows 8.1. As such, the developers of numerous apps and services are following suit -- Google included.
The company has revealed that it will end support for Google Drive for desktop on Windows 8, Windows 8.1 and Windows Server 2012 later this summer. No 32-bit version of Windows will be supported either, meaning that Drive users will have to upgrade their operating system, or stick with the web-based version of Google's cloud storage service.

The challenge of protecting data in the cloud [Q&A]
Modern enterprises hold huge volumes of data and increasingly it's stored in the cloud. This means that protecting the information is a significant challenge and it can even be easy to lose track of where data is.
We spoke to Dan Benjamin, co-founder and CEO of Dig Security, to discuss the risks around cloud data storage and how to address them.

Google Drive security flaw allows data to be stolen without trace
Cloud incident response company Mitiga has released research on a significant forensic security deficiency in Google Workspace that enables threat actors to exfiltrate data in Google Drive without any trace.
Data theft is one of the most common motives for attack, and with more than six million businesses using Google Workspace -- including Google Drive -- the cloud-based repository has been a prime target for data exfiltration.

90 percent of organizations have had identity-related incidents in the past year
In the last 12 months, 90 percent of organizations have suffered an identity-related incident, an increase of six percent over the previous year.
A new report, based on an online survey of over 500 identity and security professionals, from The Identity Defined Security Alliance, shows that only 49 percent of respondents say that their leadership teams understand identity and security risks and proactively invest in protection before suffering an incident, while 29 percent only engage and support after an incident.

Beating the headache of SaaS sprawl [Q&A]
Moving to the cloud has always presented something of a challenge, but the pandemic made things even more difficult because of the need to manage more applications across a distributed workforce.
Add in the issue of shadow IT, and enterprises are increasingly struggling with SaaS sprawl. We spoke to BetterCloud CTO, Jamie Tischart to learn more about the problem and how to deal with it.

The top five cloud security risks
New analysis by Orca Security of scan results from its Cloud Security Platform reveals the top risks facing organizations this year.
The analysis of workload, configuration and identity data from real-world production cloud assets on Amazon Web Services (AWS), Microsoft Azure, Google Cloud, Kubernetes and more identifies five of the most common, yet severe, cloud security risks which are found in many cloud environments.
